SharePoint servers are being picked at with high-risk, respectable-looking, branded phish messages and preyed on by a ransomware gang employing an outdated bug.
A phishing marketing campaign, uncovered by scientists at Cofense, is draping by itself in a Microsoft Business SharePoint theme and productively bypassing security email gateways (SEGs). In a submit on Tuesday, the organization mentioned that this is an illustration of why it’s not constantly prudent to share paperwork through Microsoft’s vastly popular, widely utilized SharePoint collaboration platform.
The phish is concentrating on Office 365 buyers with a genuine-seeking SharePoint doc that claims to urgently need an email signature. The campaign cropped up in a spot that is intended to be shielded by Microsoft’s very own SEG. This isn’t the initial time that we’ve noticed the SEG sanctuary get polluted:: In December, spearphishers spoofed Microsoft.com by itself to concentrate on 200 million Workplace 365 end users, efficiently slipping earlier SEG controls due to Microsoft’s noted failure to enforce domain-based concept authentication, reporting & conformance (DMARC): an email authentication protocol designed exclusively to quit correct area spoofing (SPF/DKIM).
‘Response Urgently…?’
As this impression of the text in the phishing email shows, the spelling and grammar utilized in the boobytrapped concept aren’t the most egregious, atrociously spelled, syntactically weird giveaways you can obtain in these types of phishing campaigns. But then once more, it’s possibly secure to suppose that any SharePoint information that asks you to “response urgently” isn’t coming from a indigenous speaker.
Click Picture to Enlarge
The mere actuality that the information presses urgency on its recipients should really be a tip-off, of training course: “Rush-rush” is a usual phishing ploy. Cofense notes that other purple flags include the actuality that the user’s name isn’t apparent in the opening message: an sign that it is a mass-distribution marketing campaign intended to achieve numerous targets.
As perfectly, when recipients hover over the hyperlink, they’ll see conceal nor hair of any reference to Microsoft. These who click on the hyperlink will alternatively be shuffled about to the landing web page proven under, which display’s Microsoft’s SharePoint emblem and the “Pending file” notification in front of a blurry qualifications and a request for the supposed sufferer to log in to look at the doc. That “could suffice for risk actors to extract and harvest users’ individual data,” Cofense states. If and when credentials are handed in excess of, the campaign redirects the person to a spoofed, unrelated document, “which may well be more than enough to trick the consumer into thinking this is a legitimate transaction,” Cofense suggests.
In its X-Force Danger Action Report, IBM labelled the phish a superior-risk menace and gave these suggestions:
- Make certain anti-virus software program and related files are up to day.
- Look for for present symptoms of the indicated incidents of compromise (IoCs) in your environment.
- Take into consideration blocking and/or environment up detection for all URL and IP dependent IoCs.
- Hold purposes and working devices managing at the present-day unveiled patch stage.
- Work out warning with attachments and backlinks in e-mail.
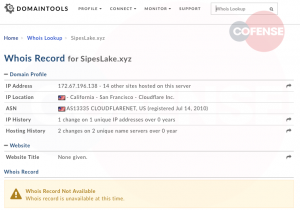
Click Graphic to Enlarge
While it’s large risk, this phishing marketing campaign is basically just an additional story of a destructive actor putting up bogus substance that seems reputable in purchase to lure customers into clicking, in the hopes of acquiring credentials. Do not shrug it off, however: it is nonetheless a further attack versus SharePoint servers, which have now joined the roster of network products – including significantly-bedeviled Microsoft Trade email servers, SonicWall gateways and Pulse Safe gateways – that are being used by ransomware gangs to jimmy open company networks.
Which brings us to ransomware: the next slap in the double-SharePoint whammy:
Ransomware Gang Pings the Soreness By way of Wickr
It is a reasonably new variant, to start with spotted in January by Pondurance. Analysts are contacting it two names: Hello there, since some samples use .hello there as an extension or WickrMe, since the gang that is pushing it are employing the Wickr encrypted immediate messaging services to check out to shake down victims for ransom.
The attackers are employing a dusty Microsoft SharePoint 2019 vulnerability (CVE-2019-0604) to pry their way into victims’ networks. From there, they’re applying Cobalt Strike to pivot to the domain controller and launch ransomware attacks.
CVE-2019-0604 is a large-severity CVE that can direct to remote code-execution. Microsoft patched the flaw in March 2019, but nevertheless, there seems to be no stop to the assaults that have made use of it to penetrate unpatched servers given that then. One particular example: Microsoft warned in Oct 2020 that Iranian nation-state actors were making use of CVE-2019-0604 to exploit remotely unpatched servers and to then implant a web shell to get persistent access and code execution. Following the web shell installation, an attacker deploys Cobalt Strike – a commercially out there penetration-screening instrument that they later on use to set up a backdoor that lets them operate automated PowerShell script, which inevitably download and set up the remaining payload: the Hi there/Wickr ransomware.
Download “The Evolution of Ransomware” to obtain valuable insights on emerging tendencies amidst speedily developing attack volumes. Simply click earlier mentioned to hone your protection intelligence!
Jeff Costlow, CISO of ExtraHop, told Threatpost on Wednesday that the ransomware attacks in opposition to the 2019 vulnerability affecting SharePoint servers are the far more insidious danger in the double whammy, in that they install distant manage program and therefore enable direct access to the infrastructure the place attackers can freely frolic.
“The popular thread is the SharePoint server,” Costlow claimed in an email. “Anyone applying SharePoint needs to guarantee that they are patching any situations of SharePoint to stay clear of the malware/ransomware installations. Long expression, no sum of patching will fix the phishing difficulty. It’s also quick for attackers to create websites that mimic legit websites. We need to rethink how sharing is finished. Security groups need to have to just take a proactive stance to help their consumers conduct enterprise securely. There are various strategies to support notify users to feasible assaults, these kinds of as environment up just about every SharePoint server to use a acquainted qualifications or graphic for consumers to ensure that they only enter credentials on genuine internet sites.”
Two Separate SharePoint Jabs
Cofense informed Threatpost in an email on Wednesday early morning that there’s no evident relationship in between the SharePoint phishing campaign that its analysts uncovered and the Wickr/Hi ransomware gang’s ongoing exploitation of SharePoint server vulnerabilities.
But 1 professional pointed out that there is a monotonous regularity in the sample that these assaults abide by: 1st we get the information about a vulnerability, then it gets jumped on by attackers hunting for the sitting ducks of unpatched servers.
In an email to Threatpost on Wednesday, Avihai Ben-Yossef, CTO and co-founder of Cymulate, claimed that we’ve found this happen over and more than. “In the past 12 months, we see a repetitious pattern in this kind of assaults. A zero-day is taken advantage of by a country-point out actor,” he reported. “The affected business – in this circumstance, Microsoft – announces the vulnerability and subsequently patches it. Then other nation-point out actors studying about the vulnerability subsequently start assaults on all those who have not patched. Lastly, the legal ransomware attackers arrive in, socialize the exploit on Dark Net sites and use it … to start their possess attacks. The double-SharePoint whammy is the simple fact that country condition actors utilised it first as a zero working day (and then as a regarded vulnerability). Then ransomware actors arrived in and made use of it as perfectly.
“The concept is to know what variety of difficulties you have and in which,” he stated. “If you never know, you just can’t protect by yourself. Companies ought to create a far better response ability to monitor these announcements and risk intelligence and patch a lot quicker.”
Be part of Threatpost for “Fortifying Your Small business From Ransomware, DDoS & Cryptojacking Attacks” – a Reside roundtable party on Wed, Could 12 at 2:00 PM EDT. Sponsored by Zoho ManageEngine, Threatpost host Becky Bracken moderates an specialist panel discussing greatest defense methods for these 2021 threats. Issues and Reside audience participation encouraged. Be a part of the lively discussion and Register HERE for absolutely free.
Some parts of this article are sourced from:
threatpost.com


 Samsung’s Galaxy Book Pro is a series of super thin, light AMOLED laptops
Samsung’s Galaxy Book Pro is a series of super thin, light AMOLED laptops