Four high severity vulnerabilities have been disclosed in a framework utilized by pre-put in Android Program applications with millions of downloads.
The issues, now fixed by its Israeli developer MCE Methods, could have most likely authorized risk actors to stage distant and local attacks or be abused as vectors to get hold of sensitive info by having advantage of their extensive method privileges.
“As it is with many of pre-mounted or default applications that most Android units occur with these days, some of the influenced apps simply cannot be entirely uninstalled or disabled with no getting root accessibility to the gadget,” the Microsoft 365 Defender Research Staff claimed in a report printed Friday.

The weaknesses, which assortment from command-injection to community privilege escalation, have been assigned the identifiers CVE-2021-42598, CVE-2021-42599, CVE-2021-42600, and CVE-2021-42601, with CVSS scores concerning 7. and 8.9.
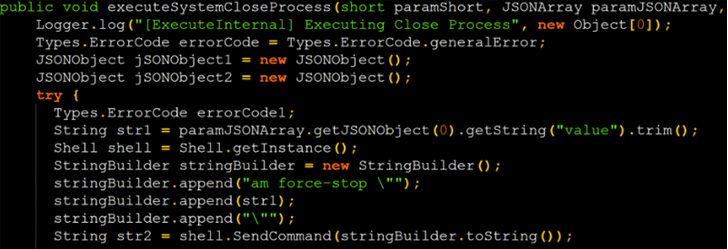 Command injection proof-of-thought (POC) exploit code
Command injection proof-of-thought (POC) exploit code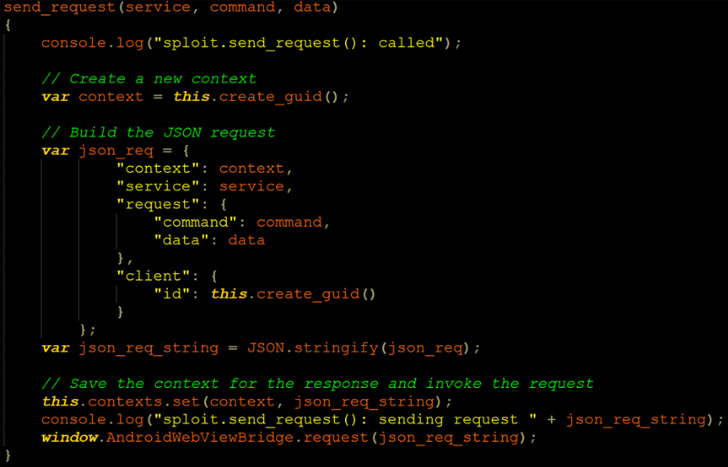 Injecting a comparable JavaScript code to the WebView
Injecting a comparable JavaScript code to the WebView
The vulnerabilities were being identified and reported in September 2021 and there is no evidence that the shortcomings are becoming exploited in the wild.
Microsoft didn’t disclose the total record of applications that use the susceptible framework in concern, which is developed to offer you self-diagnostic mechanisms to identify and resolve issues impacting an Android gadget.
This also intended that the framework experienced wide entry permissions, such as that of audio, digital camera, electrical power, site, sensor knowledge, and storage, to carry out its functions. Coupled with the issues identified in the provider, Microsoft explained it could permit an attacker to implant persistent backdoors and acquire over regulate.

Some of the impacted applications are from big intercontinental mobile company providers this kind of as Telus, AT&T, Rogers, Flexibility Cell, and Bell Canada –
- Mobile Klinik Product Checkup (com.telus.checkup)
- Gadget Assistance (com.att.dh)
- MyRogers (com.fivemobile.myaccount)
- Freedom Product Care (com.flexibility.mlp.uat), and
- Gadget Material Transfer (com.ca.bell.contenttransfer)
Additionally, Microsoft is recommending end users to search out for the app package “com.mce.mceiotraceagent” — an app that may possibly have been set up by mobile phone fix retailers — and take away it from the phones, if located.
The vulnerable applications, despite the fact that pre-installed by the phone vendors, are also offered on the Google Engage in Store and are explained to have passed the application storefront’s automatic basic safety checks with no boosting any crimson flags mainly because the process was not engineered to appear out for these issues, anything that has given that been rectified.
Identified this report interesting? Comply with THN on Facebook, Twitter and LinkedIn to read through additional distinctive content we write-up.
Some parts of this article are sourced from:
thehackernews.com


 Apple Store workers in Georgia call off union vote over intimidation claims
Apple Store workers in Georgia call off union vote over intimidation claims