Microsoft on Friday warned of active attacks exploiting unpatched Exchange Servers carried out by various risk actors, as the hacking campaign is considered to have infected tens of thousands of organizations, government entities in the U.S., Asia, and Europe.
The enterprise claimed “it continues to see improved use of these vulnerabilities in assaults targeting unpatched programs by several destructive actors further than HAFNIUM,” signaling an escalation that the breaches are no longer “limited and focused” as was beforehand deemed.
According to unbiased cybersecurity journalist Brian Krebs, at minimum 30,000 entities throughout the U.S. — primarily smaller companies, cities, cities, and regional governments — have been compromised by an “unusually aggressive” Chinese group that has set its sights on thieving e-mails from sufferer businesses by exploiting formerly undisclosed flaws in Trade Server.
Victims are also currently being documented from outside the house the U.S., with email devices belonging to enterprises in Norway and the Czech Republic impacted in a sequence of hacking incidents abusing the vulnerabilities. The Norwegian Nationwide Security Authority claimed it has executed a vulnerability scan of IP addresses in the region to establish susceptible Exchange servers and “consistently notify these corporations.”
The colossal scale of the ongoing offensive versus Microsoft’s email servers also eclipses the SolarWinds hacking spree that arrived to light-weight previous December, which is explained to have focused as quite a few as 18,000 clients of the IT management resources provider. But as it was with the SolarWinds hack, the attackers are most likely to have only gone just after substantial-worth targets dependent on an first reconnaissance of the target equipment.
Unpatched Exchange Servers at Risk of Exploitation
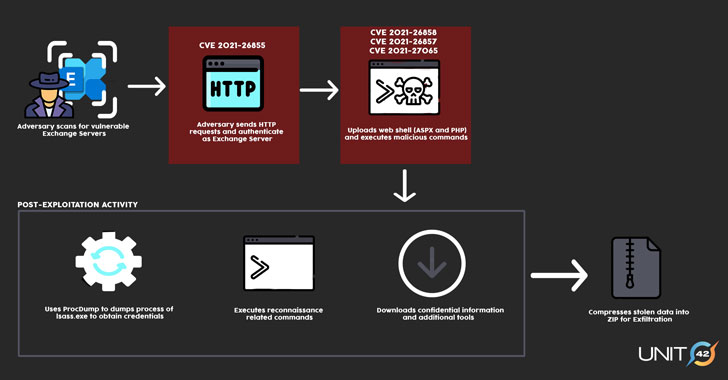
A successful exploitation of the flaws makes it possible for the adversaries to crack into Microsoft Exchange Servers in focus on environments and subsequently permit the installation of unauthorized web-primarily based backdoors to aid long-expression accessibility. With multiple threat actors leveraging these zero-day vulnerabilities, the put up-exploitation functions are predicted to vary from one group to the other based on their motives.
The 4 security issues in concern have been patched by Microsoft as portion of an unexpected emergency out-of-band security update past Tuesday, even though warning that “quite a few country-condition actors and criminal groups will shift speedily to get advantage of any unpatched systems.”
The U.S. Cybersecurity and Infrastructure Security Company (CISA), which produced an emergency directive warning of “lively exploitation” of the vulnerabilities, urged governing administration organizations operating susceptible variations of Trade Server to possibly update the application or disconnect the items from their networks.
“CISA is conscious of widespread domestic and intercontinental exploitation of Microsoft Exchange Server vulnerabilities and urges scanning Trade Server logs with Microsoft’s IoC detection device to support ascertain compromise,” the agency tweeted on March 6.
It can be truly worth noting that just putting in the patches issued by Microsoft would have no result on servers that have presently been backdoored. Organizations that have been breached to deploy the web shell and other put up-exploitation resources continue to stay at risk of long run compromise right until the artifacts are completely rooted out from their networks.
A number of Clusters Spotted
FireEye’s Mandiant menace intelligence staff explained it “noticed many scenarios of abuse of Microsoft Trade Server within just at least just one customer ecosystem” because the get started of the yr. Cybersecurity firm Volexity, one particular of the corporations credited with finding the flaws, mentioned the intrusion strategies appeared to have started off all over January 6, 2021.
Not substantially is recognised about the identities of the attackers, apart from that Microsoft has principally attributed the exploits with large assurance to a group it phone calls Hafnium, a expert government-backed team working out of China. Mandiant is monitoring the intrusion action in 3 clusters, UNC2639, UNC2640, and UNC2643, including it expects the selection to increase as much more attacks are detected.
In a assertion to Reuters, a Chinese authorities spokesman denied the region was at the rear of the intrusions.
“There are at the very least 5 unique clusters of action that appear to be exploiting the vulnerabilities,” explained Katie Nickels, director of threat intelligence at Crimson Canary, whilst noting the dissimilarities in the methods and infrastructure from that of the Hafnium actor.
In one certain occasion, the cybersecurity company observed that some of the prospects compromised Trade servers experienced been deployed with a crypto-mining software package called DLTminer, a malware documented by Carbon Black in 2019.
“1 likelihood is that Hafnium adversaries shared or marketed exploit code, resulting in other teams staying in a position to exploit these vulnerabilities,” Nickels stated. “Another is that adversaries could have reverse engineered the patches released by Microsoft to independently determine out how to exploit the vulnerabilities.”
Microsoft Issues Mitigation Assistance
Apart from rolling out fixes, Microsoft has published new alternate mitigation steerage to enable Trade shoppers who have to have more time to patch their deployments, in addition to pushing out a new update for the Microsoft Basic safety Scanner (MSERT) device to detect web shells and releasing a script for examining HAFNIUM indicators of compromise. They can be found in this article.
“These vulnerabilities are major and want to be taken very seriously,” Mat Gangwer, senior director of managed threat response at Sophos reported. “They make it possible for attackers to remotely execute commands on these servers without the need of the want for credentials, and any menace actor could potentially abuse them.”
“The wide set up of Trade and its publicity to the internet necessarily mean that lots of businesses running an on-premises Trade server could be at risk,” Gangwer extra.
Located this post appealing? Stick to THN on Fb, Twitter and LinkedIn to browse much more distinctive content material we publish.
Some parts of this article are sourced from:
thehackernews.com


 Microsoft Edge's vertical tabs will arrive this month
Microsoft Edge's vertical tabs will arrive this month