Misconfigured dashboards are yet again at the heart of a popular, ongoing cryptocurrency marketing campaign squeezing Monero and Ethereum from Kubernetes clusters.
Microsoft has noticed a new, prevalent, ongoing attack targeting Kubernetes clusters running Kubeflow occasions, in purchase to plant destructive TensorFlow pods that are made use of to mine for cryptocurrency.
The Kubeflow open-source venture is a popular framework for jogging device finding out (ML) duties in Kubernetes, while TensorFlow is an stop-to-conclude, open up-resource ML platform.
Specified that the attack is nevertheless active, any new Kubernetes clusters that operate Kubeflow could be compromised, in accordance to Microsoft.
On Tuesday, Microsoft security researchers warned that towards the finish of Could, they noticed a spike in deployments of TensorFlow pods on Kubernetes clusters – pods that are working reputable TensorFlow illustrations or photos from the official Docker Hub account. But a closer glance at the entry issue of the pods revealed that their intent is to mine cryptocurrency.
Yossi Weizman, senior security exploration computer software engineer at Microsoft’s Azure Security Centre, said in a write-up on Tuesday that the “burst” of these malicious TensorFlow deployments was “simultaneous,” indicating that the attackers at first scanned the clusters, retained a listing of potential targets, and then pulled the trigger on all of them at the moment.
Weizman discussed that the attackers employed two individual pictures: The to start with is the latest edition of TensorFlow (tensorflow/tensorflow:latest) and the 2nd is the hottest version with GPU assistance (tensorflow/tensorflow:newest-gpu). The use of TensorFlow photos in the cluster “makes a ton of feeling,” Weizman said, specified that “if the photographs in the cluster are monitored, use of [a] respectable image can avert attackers from staying identified.”
Another reason why the attackers’ option is comprehensible is that the TensorFlow graphic they chose is a handy way to run GPU jobs employing CUDA, which “allows the attacker to increase the mining gains from the host,” he explained. CUDA is a toolkit made by NVIDIA, applied to create, enhance and deploy GPU-accelerated apps.
Identical to Past Year’s Cryptomining Attack
The newly discovered attack is equivalent to a cryptocurrency mining attack that Microsoft reported last June. That earlier marketing campaign also qualified Kubeflow workloads, exploiting misconfigured dashboards to launch a common XMRIG Monero-mining campaign. Quickly-ahead a 12 months, and this not long ago discovered cryptomining pulls a equivalent transfer, using uncovered Kubeflow interfaces for operating cryptocurrency mining containers.
The latest marketing campaign provides some tweaks: As Weizman described it, this time close to, the attackers abused the access to the Kubeflow centralized dashboard in purchase to generate a new pipeline.
As Weizman detailed in the post, Kubeflow Pipelines is a system for deploying ML pipelines, centered on Argo Workflow, which an open-resource, container-indigenous workflow engine for orchestrating parallel jobs on Kubernetes. Pipeline entails a collection of techniques, every single a person of them as an impartial container, that collectively form a ML workflow. The graphic of the container that operates in just about every stage is decided in the pipeline configuration, he stated.
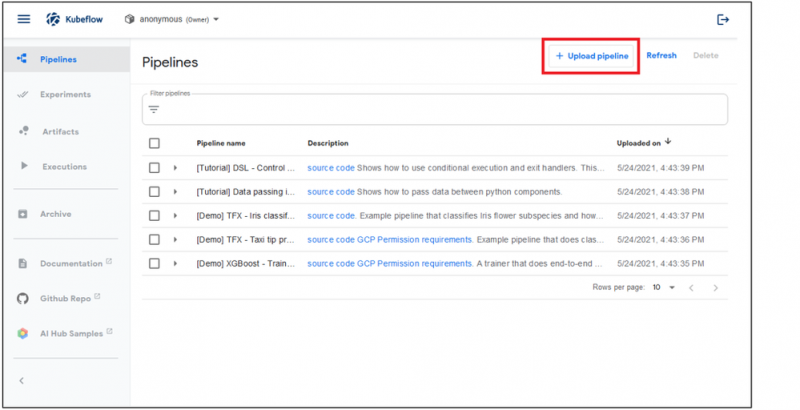
Kubeflow pipelines. Supply: Microsoft
Entry to the pipeline’s consumer interface is essential in this attack: Once attackers attain access to that dashboard, they can produce a new cluster in the pipeline. In this case, that means containers that run TensorFlow illustrations or photos that established up cryptocurrentcy mining.
All of the destructive pods had been set up with the exact pattern: “sequential-pipeline-random pattern”. That title is originated in the “generateName” discipline of the Argo Workflow object that is utilized for developing the pipeline, Weizman claimed.
At least two pods had been deployed on just about every cluster: 1 for CPU mining, and the other for GPU mining. The GPU container applied the open up-resource Ethminer to mine Ethereum, although the CPU miner used the aforementioned open-source XMRIG Monero miner.
As aspect of the ongoing attack movement, the attackers are making use of a reconnaissance container – also operate from a TensorFlow pod – to scoop up information about the surroundings, these types of as GPU and CPU particulars, in planning for mining.
What to Do to Avoid a Cyberattack
Microsoft encouraged that those people who operate Kubeflow must make guaranteed they’ve locked down the centralized dashboard so it is not insecurely exposed to the internet. If Kubeflow has to be exposed to the internet, make confident it necessitates authentication.
Microsoft gave the illustration of Kubeflow remaining applied to assistance OpenID Hook up (OIDC) using Azure Active Listing for Azure deployments. In buy to get all the pods running in the cluster in JSON format, run: kubectl get pods –all-namespaces -o json …
… and look for for containers that run TensorFlow photographs. If they exist, examine the entry position of those people containers, Microsoft advised.
Cryptomining: Lead Weights That Bathroom Down the Cloud
Yaniv Bar-Dayan, CEO and co-founder at Vulcan Cyber, reported that cryptomining is absolutely nothing to shrug off, specified the strike it places on cloud assets.
“While cryptomining campaigns can feel innocuous, they place surplus strain on cloud methods, inflict additional cloud and utility expenditures on attacked events, shorten the lifespan of IT devices and result in unwanted small business disruption,” he explained to Threatpost by using email on Thursday.
These strategies also spotlight organizations’ risk of exposure, he mentioned – in other phrases, if an attacker can pull off a cryptomining attack, they can pull off even worse. “If an attacker can start a cryptomining marketing campaign on an organization’s infrastructure, it is likely that they can launch ransomware as very well or acquire access to knowledge, mental residence, staff information and other at-risk assets that can hurt a enterprise if breached,” he ongoing.
Bar-Dayan claimed that Vulcan Cyber endorses taking the appropriate steps for defense. For example, assure proper configurations, and, echoing Microsoft, make guaranteed that techniques aren’t uncovered to the open internet. Also, make guaranteed the right identification and access controls are in place.
Obtain our distinctive Free of charge Threatpost Insider Ebook, “2021: The Evolution of Ransomware,” to enable hone your cyber-defense methods versus this growing scourge. We go over and above the standing quo to uncover what’s subsequent for ransomware and the relevant rising pitfalls. Get the whole tale and Down load the E book now – on us!
Some parts of this article are sourced from:
threatpost.com


 Steam Gaming Platform Delivering Malware
Steam Gaming Platform Delivering Malware