Scientists have shut down an “expansive” advertisement fraud scheme that spoofed additional than 1,700 programs from 120 publishers and impacted roughly 11 million equipment.
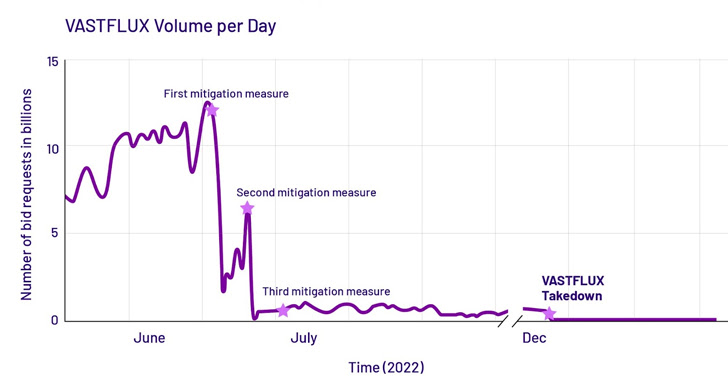
“VASTFLUX was a malvertising attack that injected destructive JavaScript code into digital ad creatives, letting the fraudsters to stack several invisible movie advertisement players powering a person another and register ad sights,” fraud avoidance firm HUMAN mentioned.
The operation gets its name from the use of a DNS evasion system identified as Rapid Flux and Broad, a Digital Movie Advertisement Serving Template that’s utilized to serve adverts to video clip gamers.
The refined procedure especially exploited the limited in-application environments that operate adverts on iOS to area bids for displaying advert banners. Need to the auction be won, the hijacked advert slot is leveraged to inject rogue JavaScript that establishes get hold of with a distant server to retrieve the listing of applications to be targeted.
The features the bundle IDs that belong to genuine apps so as to perform what is actually identified as as an app spoofing attack, in which a fraudulent application passes off as a really-regarded app in an endeavor to trick advertisers into bidding for the advertisement space.
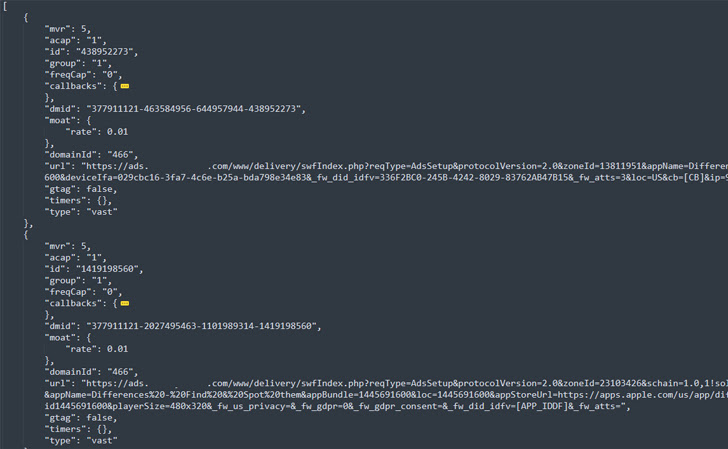
The best goal, for every HUMAN, was to sign-up sights for as a lot of as 25 movie advertisements by layering them atop one particular a different in a way that is completely invisible to the users and generates illicit income.
“It won’t quit with the stacked ads, though,” the firm reported. “For as a lot of of those people as may well be rendering on a user’s system at as soon as, they continue to keep loading new advertisements until eventually the advert slot with the malicious advertisement code is shut.”
“The actors at the rear of the VASTFLUX plan plainly have an intimate knowledge of the digital promoting ecosystem,” it further more extra, stating the campaign also rendered an endless “playlist” of advertisements to defraud both of those the promotion companies and applications that demonstrate adverts.
The takedown of VASTFLUX comes a few months after the disruption of Scylla, a fraud operation focusing on advertising software program development kits (SDKs) in 80 Android apps and 9 iOS apps released on the formal storefronts.
VASTFLUX, which generated about 12 billion bid requests per working day at its peak, is only the most current in a extend of advert fraud botnets that have been shuttered in current decades, following 3ve, PARETO, and Methbot.
Identified this report interesting? Adhere to us on Twitter and LinkedIn to read more special information we write-up.
Some parts of this article are sourced from:
thehackernews.com

 Microsoft will shut down AltspaceVR on March 10th
Microsoft will shut down AltspaceVR on March 10th