A application bundle offered from the official NPM repository has been disclosed to be really a front for a software that is designed to steal saved passwords from the Chrome web browser.
The package deal in question, named “nodejs_net_server” and downloaded in excess of 1,283 times considering that February 2019, was last up-to-date 7 months in the past (model 1.1.2), with its corresponding repository leading to non-existent places hosted on GitHub.
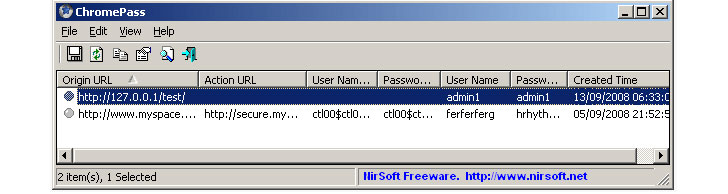
“It is just not destructive by by itself, but it can be when put into the destructive use context,” ReversingLabs researcher Karlo Zanki claimed in an evaluation shared with The Hacker News. “For occasion, this package uses it to accomplish malicious password stealing and credential exfiltration. Even while this off-the-shelf password restoration software comes with a graphical person interface, malware authors like to use it as it can also be operate from the command line.”

Though the first edition of the deal was posted just to test the process of publishing an NPM bundle, the developer, who went by the title of “chrunlee”, made revisions to put into practice a distant shell operation which was improvised above several subsequent variations.
This was adopted by the addition of a script that downloaded the ChromePass password-thieving instrument hosted on their own web site (“hxxps://chrunlee.cn/a.exe”), only to modify it three weeks later on to run TeamViewer distant entry computer software.
Apparently, the author also abused the configuration options of NPM offers specified in the “offer.json” file, specifically the “bin” subject which is made use of to install JavaScript executables, to deploy a genuine offer named “jstest,” a cross-system JavaScript exam framework, exploiting it to launch a company through command line that is able of getting an array of commands, including file lookup, file add, shell command execution, and display and digital camera recording.
ReversingLabs said it claimed the rogue package to NPM’s security workforce two times, when on July 2 and once more on July 15, but observed that no motion has been taken to date to acquire it down. We have reached out to NPM for further clarification, and we are going to update the tale as soon as we listen to again.

If anything at all, the growth the moment once again exposes the gaps in relying on 3rd-bash code hosted on general public offer repositories as software package source chain attacks grow to be a preferred tactic for menace actors to abuse the have confidence in in interconnected IT software to stage progressively innovative security breaches.
“Escalating popularity of software package package repositories and their ease of use make them a perfect target,” Zanki reported. “When builders reuse present libraries to put into action the desired performance more quickly and easier, they seldom make in-depth security assessments before like them into their challenge.”
“This omission is a result of the too much to handle character, and the wide quantity, of prospective security issues located in third-social gathering code. As a result in common, offers are speedily put in to validate whether they resolve the problem and, if they don’t, go on to the alternative. This is a perilous observe, and it can lead to incidental set up of destructive program,” Zanki extra.
Observed this report fascinating? Abide by THN on Fb, Twitter and LinkedIn to browse additional special articles we submit.
Some parts of this article are sourced from:
thehackernews.com


