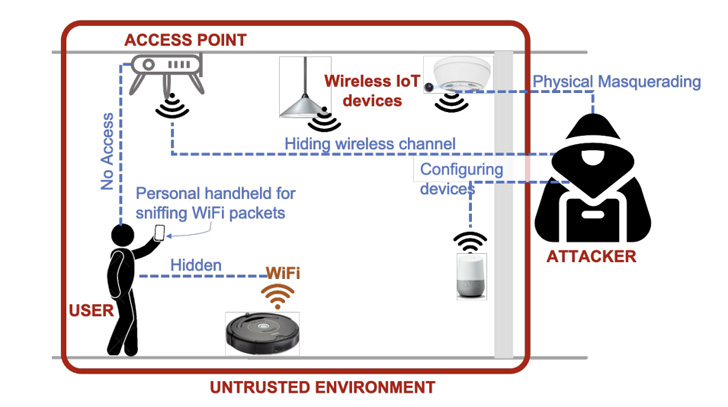
A team of lecturers has devised a program that can be made use of on a phone or a notebook to establish and locate Wi-Fi-related concealed IoT gadgets in unfamiliar physical spaces.
With hidden cameras staying significantly applied to snoop on people in hotel rooms and Airbnbs, the purpose is to be in a position to pinpoint these types of rogue units without a lot of a headache.
The method, dubbed Lumos, is intended with this intent in mind and to “visualize their existence working with an augmented truth interface,” said Rahul Anand Sharma, Elahe Soltanaghaei, Anthony Rowe, and Vyas Sekar of Carnegie Mellon College in a new paper.

At its core, the platform performs by snuffing and amassing encrypted wi-fi packets around the air to detect and discover concealed devices. Subsequently, it estimates the site of every discovered device with regard to the person as they stroll all over the perimeter of the area.
The localization module, for its aspect, combines sign power measurements that are readily available in 802.11 packets (aka Acquired Sign Strength Indicator or RSSI) with relative person situation established by visible inertial odometry (VIO) information and facts on cellular telephones.
On Apple’s iOS equipment, for occasion, the positional tracking is realized by suggests of ARKit, a developer API that can make it possible to build augmented reality ordeals by taking edge of the phone’s digital camera, CPU, GPU, and motion sensors.
“As the user walks closer to just about every unit, the RSSI values corresponding to these info factors increase and then cut down as she walks absent from the product,” the scientists stated. “Lumos leverages the spatial measurements of RSSI values and their variations to estimate the locale of each individual device.”
What is extra, Lumos can localize IoT devices irrespective of the user’s going for walks pace. Also included is a fingerprinting module that analyzes the captured 802.11 visitors designs employing a device discovering product to determine the units primarily based on the MAC addresses.
The exploration evaluated Lumos throughout 44 various IoT products spanning various forms, products, and models throughout six various environments, finding that it can establish concealed equipment with 95% accuracy and locate them with a median error of 1.5m within 30 minutes in a two-bed room, 1000 sq.ft. condominium.
That reported, an advanced attacker can leverage techniques like MAC handle randomization to evade detection and sidestep localization by arbitrarily modifying the devices’ transmit electric power.
“Lumos can likely generalize across different unit brands and models, as long as it has observed at minimum one particular product with related actions in the coaching period,” the researchers said, pointing to how the method can even establish unprofiled products.
Observed this article interesting? Adhere to THN on Fb, Twitter and LinkedIn to go through far more exceptional articles we publish.
Some parts of this article are sourced from:
thehackernews.com


 Amazon is taking up to 60 percent off WD and SanDisk storage for today only
Amazon is taking up to 60 percent off WD and SanDisk storage for today only