Malicious actors can acquire unauthorized accessibility to users’ online accounts by way of a new approach referred to as “account pre-hijacking,” new investigate has observed.
The attack normally takes aim at the account creation approach that is ubiquitous in web sites and other online platforms, enabling an adversary to perform a established of steps ahead of an unsuspecting victim makes an account in a focus on company.
The examine was led by impartial security researcher Avinash Sudhodanan in collaboration with Andrew Paverd of the Microsoft Security Reaction Middle (MSRC).
Pre-hijacking banking institutions on the prerequisite that an attacker is by now in possession of a distinctive identifier connected with a victim, such as an email tackle or phone number, which can be acquired either from the target’s social media accounts or credential dumps circulating on the web.

The attacks can then enjoy out in 5 different methods, together with the use of the exact same email address throughout account generation by both of those the adversary and the sufferer, probably granting the two functions concurrent obtain to the account.
“If the attacker can build an account at a goal support employing the victim’s email deal with just before the target produces an account, the attacker could then use many methods to set the account into a pre-hijacked condition,” the researchers stated.
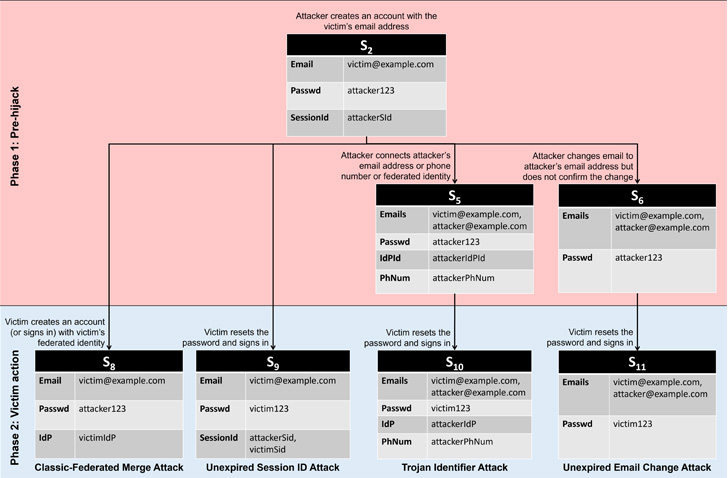
“Immediately after the target has recovered entry and begun applying the account, the attacker could get back accessibility and choose about the account.” The five styles of pre-hijacking attacks are below –
- Typical-Federated Merge Attack, in which two accounts created applying typical and federated identification routes with the identical email deal with let the target and the attacker to accessibility to the similar account.
- Unexpired Session Identifier Attack, in which the attacker makes an account applying the victim’s email deal with and maintains a prolonged-running energetic session. When the person recovers the account using the identical email address, the attacker carries on to retain access for the reason that the password reset did not terminate the attacker’s session.
- Trojan Identifier Attack, in which the attacker produces an account making use of the victim’s email deal with and then provides a trojan identifier, say, a secondary email deal with or a phone quantity less than their control. Consequently when the true user recovers obtain following a password reset, the attacker can use the trojan identifier to get back accessibility to the account.
- Unexpired Email Modify Attack, in which the attacker creates an account using the victim’s email deal with and proceeds to adjust the email handle to 1 beneath their regulate. When the provider sends a verification URL to the new email tackle, the attacker waits for the sufferer to recover and begin working with the account before completing the modify-of-email approach to seize management of the account.
- Non-Verifying Identity Company (IdP) Attack, in which the attacker produces an account with the goal provider employing a non-verifying IdP. If the target makes an account making use of the traditional registration process with the exact same email deal with, it permits the attacker to obtain entry to the account.
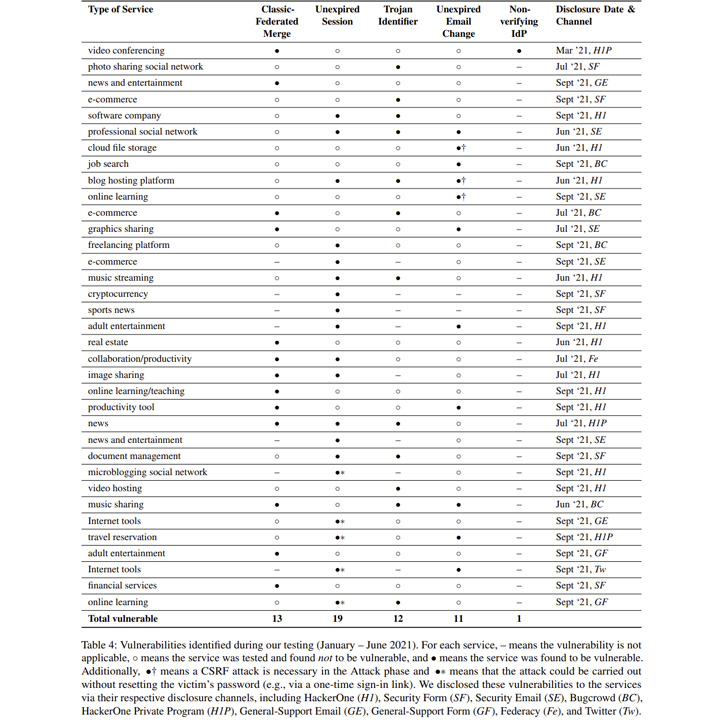
In an empirical evaluation of 75 of the most common web sites from Alexa, 56 pre-hijacking vulnerabilities ended up discovered on 35 services. This incorporates 13 Classic-Federated Merge, 19 Unexpired Session Identifier, 12 Trojan Identifier, 11 Unexpired Email Alter, and one particular Non-Verifying IdP attacks –
- Dropbox – Unexpired Email Alter Attack
- Instagram – Trojan Identifier Attack
- LinkedIn – Unexpired Session and Trojan Identifier Assaults
- WordPress.com – Unexpired Session and Unexpired Email Adjust Attacks, and
- Zoom – Basic-Federated Merge and Non-verifying IdP Assaults
“The root induce of all of the attacks […] is a failure to verify possession of the claimed identifier,” the scientists claimed.

“While many products and services do perform this form of verification, they frequently do so asynchronously, allowing for the person to use certain options of the account just before the identifier has been confirmed. Although this could possibly boost usability (lowers person friction throughout sign up), it leaves the user vulnerable to pre-hijacking assaults.”
Whilst employing stringent identifier verification in services is important to mitigating pre-hijacking assaults, it can be proposed that consumers protected their accounts with multi-variable authentication (MFA).
“Properly implemented MFA will protect against the attacker from authenticating to a pre-hijacked account immediately after the sufferer starts utilizing this account,” the scientists mentioned. “The company ought to also invalidate any classes designed prior to the activation of MFA to avoid the Unexpired Session attack.”
On major of that, on the net services are also recommended to periodically delete unverified accounts, implement a low window to verify a improve of email tackle, and invalidate sessions during password resets for a protection in-depth method to account administration.
“When a support merges an account designed via the classic route with one designed via the federated route (or vice-versa), the provider have to be certain that the user currently controls both of those accounts,” Sudhodanan and Paverd said.
Located this report appealing? Observe THN on Facebook, Twitter and LinkedIn to go through additional unique written content we article.
Some parts of this article are sourced from:
thehackernews.com

 Dyson's been secretly working on robots that do household chores
Dyson's been secretly working on robots that do household chores