It really is no mystery that 3rd social gathering applications can strengthen efficiency, permit remote and hybrid perform and are overall, crucial in making and scaling a firm’s perform procedures.
An innocuous course of action a great deal like clicking on an attachment was in the previously times of email, folks don’t imagine two times when connecting an app they need with their Google workspace or M365 atmosphere, etcetera. Simple steps that end users consider, from making an email to updating a get hold of in the CRM, can final result in several other computerized actions and notifications in the connected platforms.
As observed in the graphic below, the OAuth system helps make it exceptionally simple to interconnect applications and many you should not contemplate what the probable ramifications could be. When these applications and other add-ons for SaaS platforms question for permissions’ access, they are generally granted without having a next thought, presenting much more opportunities for poor actors to obtain accessibility to a company’s facts. This puts firms at risk for supply chain obtain assaults, API takeovers and destructive 3rd occasion applications.
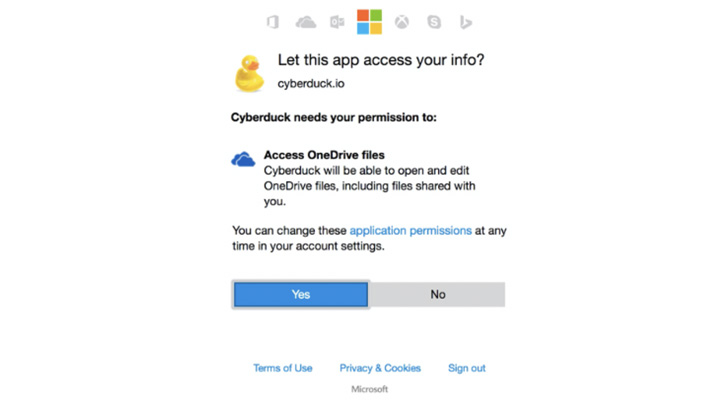 Oauth system permission ask for
Oauth system permission ask for
When it arrives to area equipment and executable files, businesses previously have control designed in that enables security groups to block problematic courses and files. It requires to be the identical when it comes to SaaS apps.
Master how to acquire visibility into 3rd bash apps
How Do 3rd Social gathering Applications Obtain Entry?
OAuth 2. has tremendously simplified authentication and authorization, and gives a fine-grained delegation of access legal rights. Represented in the kind of scopes, an software asks for the user’s authorization for particular permissions. An application can ask for a single or additional scopes. By approval of the scopes, the consumer grants these apps permissions to execute code to perform logic at the rear of the scenes in just their environment. These applications can be harmless or as threatening as an executable file.
Click on below to schedule a 15-minute demo to understand how to obtain visibility of your SaaS apps
Best Tactics to Mitigate 3rd Occasion App Obtain Risk
To protected a company’s SaaS stack, the security group needs to be in a position to identify and monitor all that occurs in just their SaaS ecosystem. This is what a security team can share with staff members and cope with on their own to mitigate 3rd party application entry risk.
1 — Teach the employees in the group
The initially move in cybersecurity normally arrives again to elevating consciousness. At the time the staff develop into much more aware of the challenges and risks that these OAuth mechanisms existing, they will be additional hesitant to use them. Corporations need to also create a plan that enforces staff to post requests for 3rd social gathering applications.
2 — Obtain visibility into the 3rd bash obtain for all enterprise-critical apps
Security teams should achieve visibility into each organization critical application and assessment all the various third party apps that have been integrated with their small business-critical SaaS applications – across all tenets. One of the very first techniques when shrinking the threat area is gaining an knowledge of the full environment.
3 — Map the permissions and access ranges requested by the related third occasion applications
At the time the security group understands which third occasion applications are connected, they need to map the permissions and the kind of access that each 3rd bash application has been supplied. From there they will be equipped to see which third occasion application presents a increased risk, centered on the better degree of scope. Remaining able to differentiate involving an application that can browse vs . an app that can compose will assist the security workforce prioritize which desires to be managed first.
In addition, the security crew must map which end users granted these permissions. For instance, a significant-privileged user, a person who has sensitive files in their workspace, who grants accessibility to a third celebration application can present a large risk to the business and demands to be remediated straight away.
4 — Get the automated approach to take care of 3rd party application access
SaaS Security Posture Administration remedies can automate the discovery of 3rd social gathering apps. The correct SSPM resolution, like Adaptive Protect, has built-in logic that maps out all the 3rds get together apps with access to the organization’s SSPM built-in apps. This visibility and oversight empowers security teams so whether a enterprise has a 100 or 600 apps, they can conveniently continue to be in command, watch and safe their firm’s SaaS stack.
The Even bigger SaaS Security Photograph
To protected a company’s SaaS stack, the security team needs to be able to determine and monitor all that transpires inside their SaaS ecosystem. 3rd party app entry is just 1 ingredient of the SaaS Security Posture Administration image.
Most current cybersecurity remedies however do not supply sufficient security or a convenient way to monitor a firm’s SaaS stack, allow by itself the communications concerning their identified applications and platforms, leaving organizations vulnerable and not able to effectively know or regulate which functions have accessibility to delicate corporate or own knowledge.
Organizations require to be able to see all the configurations and person permissions of every single and just about every application, which include all the 3rd social gathering apps that have been granted obtain by customers. This way security groups can keep command of the SaaS stack, remediate any issues, block any applications employing much too numerous privileges and mitigate their risk.
Find out how to safe your 3rd occasion application obtain and SaaS stack
Located this write-up interesting? Comply with THN on Fb, Twitter and LinkedIn to browse extra special written content we article.
Some parts of this article are sourced from:
thehackernews.com


 Apple's MagSafe Battery pack is the cheapest it's been this year
Apple's MagSafe Battery pack is the cheapest it's been this year