Ransomware is not a new attack vector. In fact, the initially malware of its type appeared much more than 30 several years in the past and was distributed via 5.25-inch floppy disks. To pay back the ransom, the victim had to mail funds to a P.O. Box in Panama.
Rapid ahead to now, reasonably priced ransomware-as-a-service (RaaS) kits are out there on the dark web for any one to acquire and deploy and attackers have an infinite variety of channels available to them to infiltrate companies as a final result of reliance on cloud and cell technologies.
Initiating a ransomware attack is all about discretely attaining access. And as staff can now access your details from any where, you have misplaced visibility into how they do so. To safeguard towards these assaults, you’re not just wanting for malware, you need steady insights into your people, the endpoints they use and the programs and info they accessibility.
Lookout, a chief in endpoint-to-cloud security, has published an interactive infographic to support you visualize how a ransomware attack occurs and fully grasp how to shield your information. Lookout will use this blog site to established up 1) the weather that resulted in $20-billion bucks in ransom payments in 2021, and 2) how you can defend your organization from these ongoing threats.
Function from any place increases the two productiveness and attacker infiltration
While the genuine malware used to hold your info hostage is referred to as “ransomware,” which is not what you ought to concentrate on. Before nearly anything is deployed, attackers will need obtain to your infrastructure.
These days, customers are accessing data working with networks you do not control and devices you you should not deal with, rendering whatever on-premises security steps you experienced out of date.
This means threat actors can start phishing assaults to compromise person qualifications or exploit a susceptible app with minor consequence. And as soon as they are within your infrastructure, they quickly deploy malware to develop persistent backdoors that help them to occur and go as they please. If they escalate privileges, it gets to be almost impossible to prevent them from relocating around laterally and keeping your facts hostage.
Step-by-stage: how to safeguard against ransomware
There are a number of methods that materialize concerning an attacker accessing your infrastructure and inquiring for a ransom. These actions are outlined in the anatomy of a ransomware attack infographic and in this article is a superior-level rundown of what takes place and how you can protect your business.
1 — Block phishing attacks and cloak web-enabled applications
1 of the least difficult ways attackers gain entry is by taking more than a person account by compromising credentials with phishing assaults. It truly is critical to be able to examine web targeted traffic on any machine to block these attacks from affecting equally Pc and cell end users. This will be certain that ransomware operators can’t kick off their attacks by compromising accounts.
Threat actors will also crawl the web to locate vulnerable or exposed internet-facing infrastructure to exploit. Several organizations have apps or servers uncovered to the web to enable distant entry, but this implies attackers can discover them and glance for vulnerabilities. Cloaking these applications from discovery is a vital defense tactic. This aids you move absent from the unbridled obtain delivered by VPNs and make sure only authorized end users access the knowledge they need.
2 — Detect and reply to anomalous behaviors
If attackers regulate to enter your infrastructure, they will start out shifting laterally to perform reconnaissance. This is to obtain more vulnerabilities with the ultimate aim of uncovering delicate information. Some of the measures they could choose incorporate switching your settings to lower security permissions, exfiltrating details and uploading malware.
Some of these ways could not be outright destructive actions but can be viewed as anomalous conduct. This is exactly where an being familiar with of consumer and machine behavior and segmenting obtain at the software stage gets to be necessary. To stop lateral motion, you want to ensure no customers have absolutely free roam of your infrastructure and that they usually are not performing in a destructive manner. It really is also important to be ready to detect too much or misconfigured privileges so that you can reduce adjustments to your application and cloud posture.
3 — Render info useless for ransom with proactive encryption
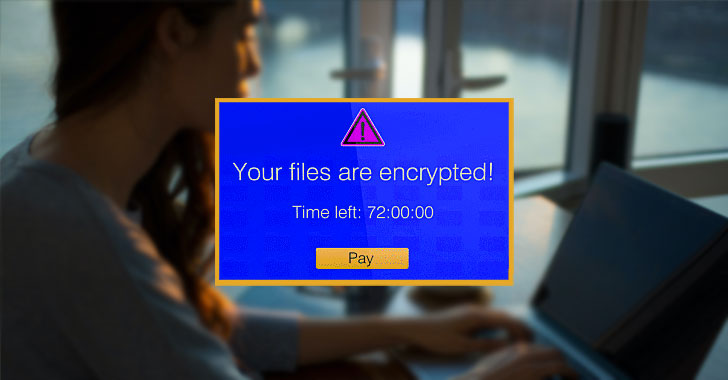
The last action of a ransomware attack is to hold your details hostage. In addition to encrypting the information and locking your admins out, the attacker could also exfiltrate some information to use as leverage, then delete or encrypt what is actually left in your infrastructure.
Exfiltration and influence are generally when the attacker ultimately reveals their presence. The adjustments they make to information, no matter of if it is really at relaxation or in movement, will established off alarm bells and they will desire payments. Nonetheless, you can make all their attempts for naught if that data is encrypted proactively by your security platform and renders it unquestionably worthless to the attacker. Encryption is a critical aspect of any data decline prevention (DLP) system, and triggering it off of contextual data safety policies can assist you guard your most sensitive details from compromise.
Securing towards ransomware: point merchandise as opposed to a unified system
A ransomware attack isn’t just a one event it is a persistent danger. To protected your group, you have to have a whole image of what is happening with your endpoints, buyers, apps and details. This assures that you can block phishing assaults, cloak web applications, detect and react to lateral motion, and safeguard your facts even if it is exfiltrated and held for ransom.
Traditionally, businesses have acquired new tools to mitigate new difficulties. But this sort of solution will not function with threats like ransomware. Even though you might have some telemetry into your users’ accessibility exercise, the wellness of their company-owned product and how your details is dealt with, your security crew will have to manage various consoles that really don’t do the job with each other.
Lookout have an understanding of the will need for a system strategy and have built a Security Assistance Edge (SSE) platform that incorporates DLP, User and Entity Habits Analytics (UEBA) and Company Digital Rights Administration (EDRM).
With a system that offers integrated insights into every thing that’s going on within your firm, we allow you to safe sensitive information without having hindering efficiency. Lookout’s SSE platform was just lately named a Visionary by the 2022 Gartner Magic Quadrant for SSE. Lookout also scored in the leading 3 for all SSE use circumstances in the 2022 Gartner Critical Abilities for SSE.
To find out additional about critical lessons you can understand from large ransomware attacks in 2021, and how to secure your sensitive facts, down load Lookout’s latest guidebook on ransomware.
Identified this report interesting? Comply with THN on Facebook, Twitter and LinkedIn to examine much more distinctive content we put up.
Some parts of this article are sourced from:
thehackernews.com

 New York City reportedly has more Airbnb listings than rentable apartments
New York City reportedly has more Airbnb listings than rentable apartments