A new Iranian risk actor has been discovered exploiting a now-tackled critical flaw in the Microsoft Windows MSHTML system to target Farsi-talking victims with a new PowerShell-primarily based details stealer intended to harvest considerable information from contaminated equipment.
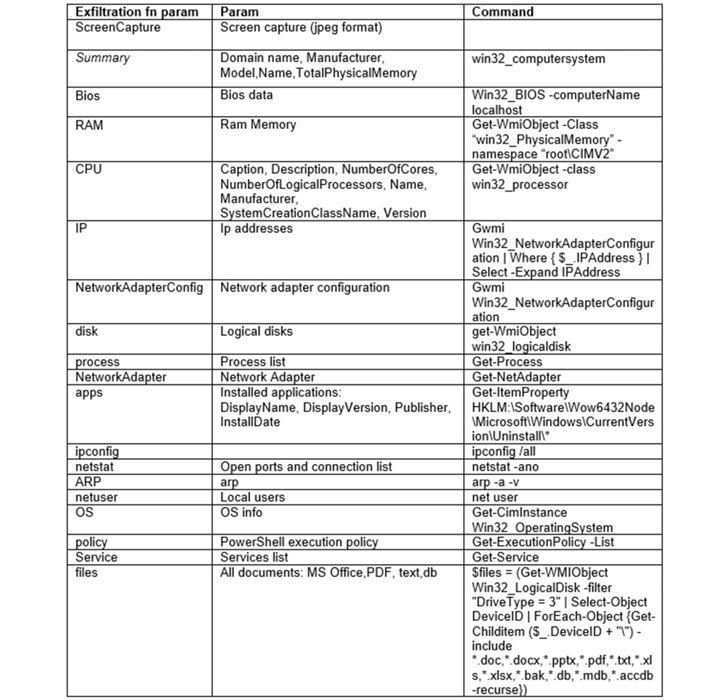
“[T]he stealer is a PowerShell script, shorter with effective assortment capabilities — in only ~150 traces, it provides the adversary a ton of critical information and facts which include display captures, Telegram documents, document collection, and substantial information about the victim’s ecosystem,” SafeBreach Labs researcher Tomer Bar reported in a report revealed Wednesday.

Almost half of the targets are from the U.S., with the cybersecurity agency noting that the assaults are probable aimed at “Iranians who stay abroad and may be noticed as a risk to Iran’s Islamic routine.”
The phishing marketing campaign, which began in July 2021, associated the exploitation of CVE-2021-40444, a remote code execution flaw that could be exploited employing specially crafted Microsoft Office files. The vulnerability was patched by Microsoft in September 2021, weeks immediately after reviews of lively exploitation emerged in the wild.
“An attacker could craft a destructive ActiveX manage to be applied by a Microsoft Workplace doc that hosts the browser rendering motor. The attacker would then have to persuade the person to open the malicious document. End users whose accounts are configured to have less consumer rights on the program could be less impacted than consumers who function with administrative person rights,” the Windows maker had famous.
The attack sequence described by SafeBreach begins with the targets obtaining a spear-phishing email that will come with a Word doc as an attachment. Opening the file triggers the exploit for CVE-2021-40444, resulting in the execution of a PowerShell script dubbed “PowerShortShell” that is able of hoovering delicate details and transmitting them to a command-and-manage (C2) server.

Although bacterial infections involving the deployment of the info-stealer had been noticed on September 15, a day right after Microsoft issued patches for the flaw, the aforementioned C2 server was also used to harvest victims’ Gmail and Instagram qualifications as part of two phishing campaigns staged by the same adversary in July 2021.
The advancement is the most up-to-date in a string of assaults that have capitalized on the MSTHML rendering motor flaw, with Microsoft earlier disclosing a specific phishing marketing campaign that abused the vulnerability as portion of an initial obtain marketing campaign to distribute personalized Cobalt Strike Beacon loaders.
Uncovered this short article appealing? Comply with THN on Facebook, Twitter and LinkedIn to browse far more distinctive content material we publish.
Some parts of this article are sourced from:
thehackernews.com


 Ukrainian Cops Bust Mobile Device Hacking Group
Ukrainian Cops Bust Mobile Device Hacking Group