Destructive actors are deploying a beforehand undiscovered binary, an Internet Information Companies (IIS) webserver module dubbed “Owowa,” on Microsoft Trade Outlook Web Obtain servers with the goal of stealing credentials and enabling distant command execution.
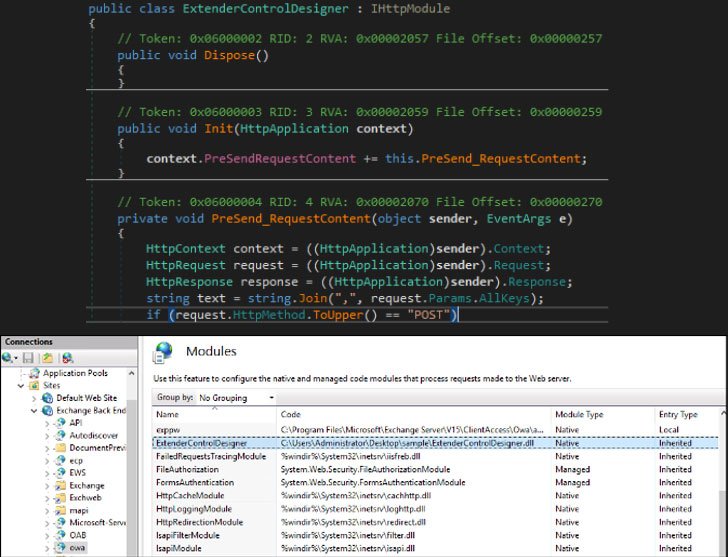
“Owowa is a C#-developed .NET v4. assembly that is intended to be loaded as a module within just an IIS web server that also exposes Exchange’s Outlook Web Accessibility (OWA),” Kaspersky scientists Paul Rascagneres and Pierre Delcher claimed. “When loaded this way, Owowa will steal qualifications that are entered by any consumer in the OWA login website page, and will permit a distant operator to operate commands on the underlying server.”
The thought that a rogue IIS module can be fashioned as a backdoor is not new. In August 2021, Slovak cybersecurity business ESET’s examine of the IIS landscape revealed as several as 14 malware people that were being created as indigenous IIS modules in an attempt to intercept HTTP visitors and remotely commandeer the compromised computers.

As a persistent ingredient on the compromised method, Owawa is engineered to seize the qualifications of buyers who are productively authenticated on the OWA authentication web web page. Exploitation can then be attained by sending “seemingly innocuous requests” to the uncovered web products and services by moving into exclusively crafted instructions in the username and password fields in the OWA authentication page of a compromised server.
Especially, if the OWA username is “jFuLIXpzRdateYHoVwMlfc,” Owawa responds again with the encrypted credentials. If the username, on the other hand, is “dEUM3jZXaDiob8BrqSy2PQO1”, the PowerShell command typed in the OWA password discipline is executed, the outcomes of which are despatched back again to the attacker.
The Russian security company said it detected a cluster of targets with compromised servers found in Malaysia, Mongolia, Indonesia, and the Philippines that generally belong to authorities corporations, with the exception of a person server which is connected to a government-owned transportation organization. That explained, more organizations in Europe are thought to have been victimized by the actor as perfectly.
Whilst no links have been unearthed amongst the Owowa operators and other publicly documented hacking teams, a username “S3crt” (read through “magic formula”) that was found embedded in the supply code of the determined samples has yielded supplemental malware executables that are probable the work of the exact developer. Chief among the them are a selection of binaries developed to execute an embedded shellcode, load next-phase malware retrieved from a remote server, and trigger the execution of Cobalt Strike payloads.
Kaspersky’s World Research and Evaluation Staff (Good) also reported it identified an account with the similar username on Keybase, where by the person has shared offensive instruments this kind of as Cobalt Strike and Core Impact, in addition to demonstrating an interest in the latter on RAIDForums.
“IIS modules are not a prevalent format for backdoors, particularly when in comparison to normal web application threats like web shells and can thus easily be skipped throughout regular file checking initiatives,” Rascagneres and Delcher explained. “The malicious module […] signifies an successful solution for attackers to achieve a robust foothold in specific networks by persisting inside of an Trade server.”
Discovered this short article interesting? Comply with THN on Facebook, Twitter and LinkedIn to go through a lot more unique content material we post.
Some parts of this article are sourced from:
thehackernews.com

