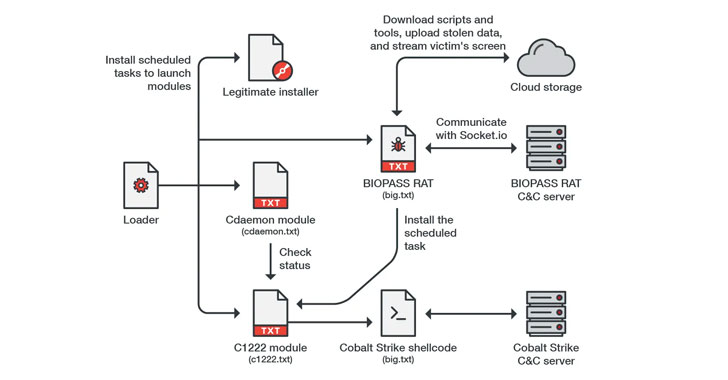
Cybersecurity researchers are warning about a new malware which is placing online gambling providers in China via a watering gap attack to deploy possibly Cobalt Strike beacons or a beforehand undocumented Python-centered backdoor referred to as BIOPASS RAT that usually takes gain of Open Broadcaster Program (OBS) Studio’s stay-streaming application to seize the monitor of its victims to attackers.
The attack entails deceiving gaming web page visitors into downloading a malware loader camouflaged as a authentic installer for popular-but-deprecated apps these types of as Adobe Flash Participant or Microsoft Silverlight, only for the loader to act as a conduit for fetching next-phase payloads.
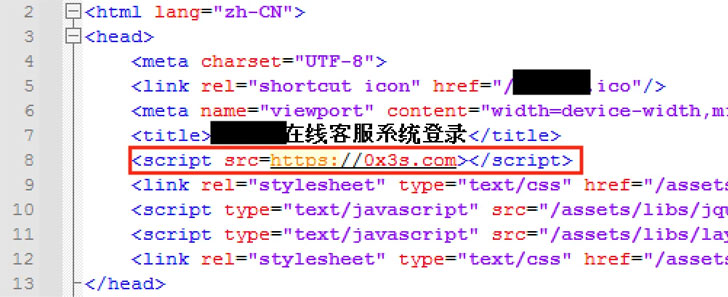
Especially, the websites’ on the internet assist chat internet pages are booby-trapped with malicious JavaScript code, which is employed to supply the malware to the victims.

“BIOPASS RAT possesses essential capabilities identified in other malware, this kind of as file process assessment, remote desktop access, file exfiltration, and shell command execution,” Development Micro scientists mentioned in an assessment published Friday. “It also has the ability to compromise the personal facts of its victims by stealing web browser and instant messaging client information.”
OBS Studio is an open-resource program for video clip recording and dwell streaming, enabling consumers to stream to Twitch, YouTube, and other platforms.
Moreover featuring an array of abilities that operate the normal adware gamut, BIOPASS is equipped to build reside streaming to a cloud services less than the attacker’s control by using Real-Time Messaging Protocol (RTMP), in addition to communicating with the command-and-regulate (C2) server using the Socket.IO protocol.
The malware, which is reported to be less than lively growth, is also noteworthy for its aim on thieving private facts from web browsers and fast messaging applications chiefly well-liked in Mainland China, like QQ Browser, 2345 Explorer, Sogou Explorer, and 360 Risk-free Browser, WeChat, QQ, and Aliwangwang.

It isn’t very clear just as to who is behind this malware pressure, but Development Micro researchers said they located overlaps amongst BIOPASS and that of TTPs typically affiliated with the Winnti Team (aka APT41), a refined Chinese hacking team specialized in cyber espionage attacks, based on the use of stolen certificates and a Cobalt Strike binary that was previously attributed to the threat actor.

What’s additional, the identical Cobalt Strike binary has also been related to a cyber attack concentrating on MonPass, a important certification authority (CA) in Mongolia, earlier this year whereby its installer software program was tampered with to set up Cobalt Strike beacon payloads on contaminated methods.
“BIOPASS RAT is a subtle variety of malware that is implemented as Python scripts,” the scientists stated. “Provided that the malware loader was sent as an executable disguised as a legit update installer on a compromised site, […] it is advisable to down load applications only from dependable resources and formal internet websites to prevent currently being compromised.”
Discovered this post appealing? Abide by THN on Facebook, Twitter and LinkedIn to browse extra exceptional material we publish.
Some parts of this article are sourced from:
thehackernews.com

 Recommended Reading: How ESPN called Euro 2020 matches from the US
Recommended Reading: How ESPN called Euro 2020 matches from the US