Unpatched Fortinet VPN products are remaining focused in a series of assaults from industrial enterprises in Europe to deploy a new strain of ransomware identified as “Cring” inside of corporate networks.
At the very least one particular of the hacking incidents led to the non permanent shutdown of a output site, said cybersecurity agency Kaspersky in a report published on Wednesday, with out publicly naming the sufferer.
The attacks transpired in the initially quarter of 2021, between January and March.
“Different details of the attack indicate that the attackers experienced cautiously analyzed the infrastructure of the targeted group and well prepared their possess infrastructure and toolset based on the info collected at the reconnaissance stage,” said Vyacheslav Kopeytsev, a security researcher at Kaspersky ICS CERT.
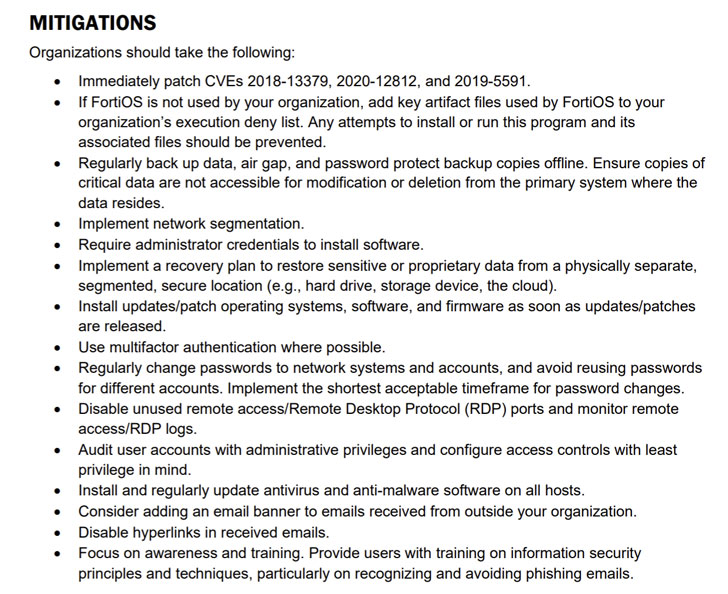
The disclosure comes times just after the Federal Bureau of Investigation (FBI) and the Cybersecurity and Infrastructure Security Agency (CISA) warned of state-of-the-art persistent menace (APT) actors actively scanning for Fortinet SSL VPN appliances susceptible to CVE-2018-13379, among the many others.
“APT actors may use these vulnerabilities or other popular exploitation methods to get original access to a number of governing administration, professional, and technology providers. Gaining original accessibility pre-positions the APT actors to carry out potential attacks,” the company explained.
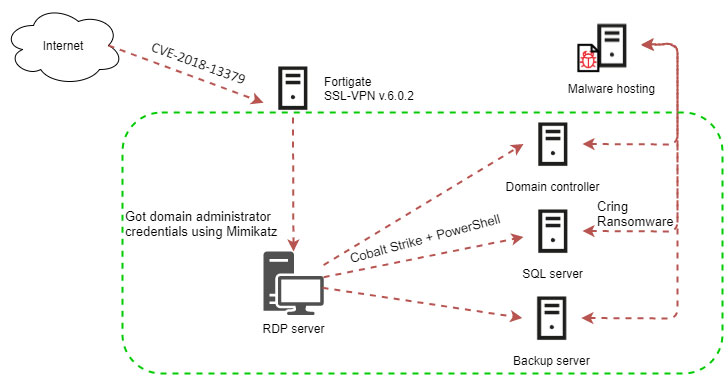
CVE-2018-13379 problems a path traversal vulnerability in the FortiOS SSL VPN web portal, which will allow unauthenticated attackers to browse arbitrary program information, which includes the session file, which includes usernames and passwords saved in plaintext.
Despite the fact that patches for the vulnerability have been unveiled in May possibly 2019, Fortinet said past November that it identified a “massive amount” of VPN appliances that remained unpatched, even though also cautioning that IP addresses of those people internet-going through vulnerable equipment had been staying bought on the dark web.
The attacks aimed at European businesses ended up no diverse, according to Kaspersky’s incident response, which located that the deployment of Cring ransomware concerned exploitation of CVE-2018-13379 to get accessibility to the goal networks.
“Some time prior to the key phase of the procedure, the attackers executed take a look at connections to the VPN Gateway, evidently in buy to make certain that the stolen person credentials for the VPN have been however legitimate,” Kaspersky researchers stated.
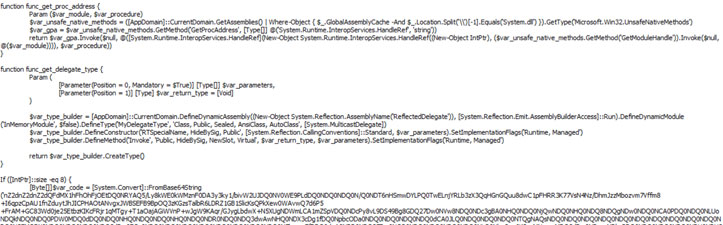
On attaining accessibility, the adversaries are reported to have utilised the Mimikatz utility to siphon account qualifications of Windows consumers who experienced earlier logged in to the compromised process, then employing them to break into the area administrator account, shift laterally throughout the network, and eventually deploy the Cring ransomware on each individual equipment remotely employing the Cobalt Strike framework.
Cring, a nascent pressure that was very first observed in January 2021 by telecom service provider Swisscom, encrypts precise information on the products applying robust encryption algorithms soon after taking away traces of all backup files and terminating Microsoft Business and Oracle Database processes. Pursuing effective encryption, it drops a ransom take note demanding payment of two bitcoins.
What is actually additional, the menace actor was thorough to conceal their action by disguising the destructive PowerShell scripts beneath the identify “kaspersky” to evade detection and ensured that the server hosting the ransomware payload only responded to requests coming in from European international locations.
“An evaluation of the attackers’ exercise demonstrates that, centered on the outcomes of the reconnaissance executed on the attacked organization’s network, they chose to encrypt those servers which the attackers believed would lead to the best hurt to the enterprise’s functions if lost,” Kopeytsev claimed.
Identified this short article exciting? Stick to THN on Fb, Twitter and LinkedIn to go through much more distinctive content we put up.
Some parts of this article are sourced from:
thehackernews.com

 NIST and HIPAA: Is There a Password Connection?
NIST and HIPAA: Is There a Password Connection?