Cybersecurity scientists on Monday tied a string of attacks concentrating on Accellion File Transfer Equipment (FTA) servers in excess of the earlier two months to data theft and extortion campaign orchestrated by a cybercrime team known as UNC2546.
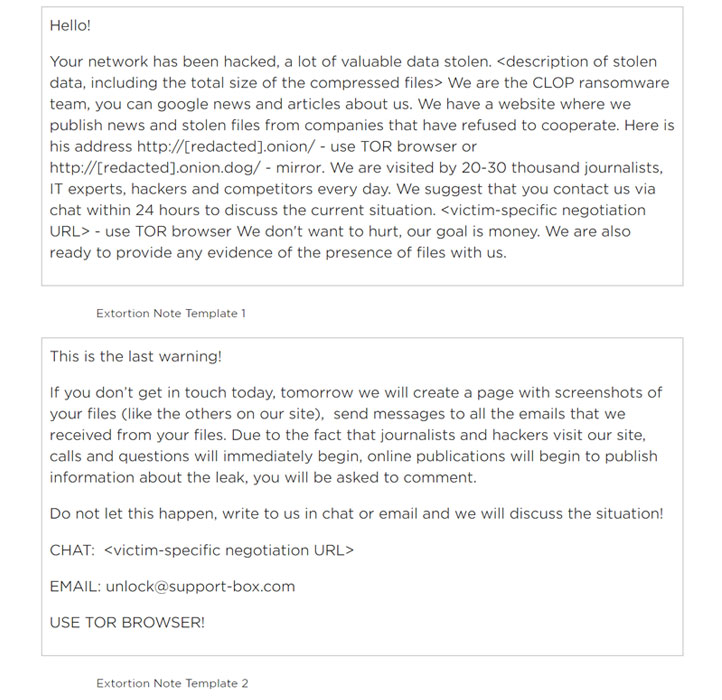
The assaults, which began in mid-December 2020, concerned exploiting a number of zero-working day vulnerabilities in the legacy FTA application to put in a new web shell named DEWMODE on target networks and exfiltrating delicate info, which was then released on a information leak internet site operated by the CLOP ransomware gang.
But in a twist, no ransomware was truly deployed in any of the latest incidents that hit businesses in the U.S., Singapore, Canada, and the Netherlands, with the actors in its place resorting to extortion e-mails to threaten victims into paying bitcoin ransoms.

According to Dangerous Business enterprise, some of the providers that have had their info stated on the web page involve Singapore’s telecom supplier SingTel, the American Bureau of Shipping, regulation company Jones Working day, the Netherlands-primarily based Fugro, and lifetime sciences company Danaher.
Next the slew of attacks, Accellion has patched 4 FTA vulnerabilities that had been recognised to be exploited by the menace actors, in addition to incorporating new monitoring and alerting capabilities to flag any suspicious conduct. The flaws are as follows –
- CVE-2021-27101 – SQL injection by way of a crafted Host header
- CVE-2021-27102 – OS command execution by way of a nearby web provider connect with
- CVE-2021-27103 – SSRF by means of a crafted Submit ask for
- CVE-2021-27104 – OS command execution by using a crafted Put up ask for
FireEye’s Mandiant risk intelligence staff, which is main the incident response efforts, is tracking the follow-on extortion scheme beneath a different menace cluster it phone calls UNC2582 irrespective of “persuasive” overlaps recognized concerning the two sets of malicious activities and preceding assaults carried out by a financially motivated hacking team dubbed FIN11.
“Numerous of the organizations compromised by UNC2546 had been formerly qualified by FIN11,” FireEye mentioned. “Some UNC2582 extortion e-mail noticed in January 2021 ended up despatched from IP addresses and/or email accounts made use of by FIN11 in multiple phishing campaigns amongst August and December 2020.”
When mounted, the DEWMODE web shell was leveraged to down load files from compromised FTA situations, primary to the victims obtaining extortion e-mail proclaiming to be from the “CLOP ransomware crew” many weeks later.
Deficiency of reply in a timely way would outcome in additional emails despatched to a broader group of recipients in the target organization as nicely as its associates containing backlinks to the stolen data, the scientists specific.
Apart from urging its FTA customers to migrate to kiteworks, Accellion claimed less than 100 out of 300 overall FTA consumers were being victims of the attack and that fewer than 25 appear to have experienced “major” knowledge theft.
The advancement will come right after grocery chain Kroger disclosed previous 7 days that HR information, pharmacy records, and funds expert services documents belonging to some buyers may have been compromised as a end result of the Accellion incident.
Then earlier currently, Transportation for New South Wales (TfNSW) grew to become the most up-to-date entity to confirm that it experienced been impacted by the around the world Accellion knowledge breach.
“The Accellion system was extensively applied to share and retail outlet files by organisations close to the globe, including Transportation for NSW,” the Australian company reported. “Before the attack on Accellion servers was interrupted, some Transportation for NSW info was taken.”
Found this write-up exciting? Follow THN on Facebook, Twitter and LinkedIn to browse far more exceptional material we article.
Some parts of this article are sourced from:
thehackernews.com

 The Ready! Model 100 is a Raspberry Pi enclosure for cyberpunk enthusiasts
The Ready! Model 100 is a Raspberry Pi enclosure for cyberpunk enthusiasts