Destructive actors have been observed abusing genuine adversary simulation software program in their attacks in an try to stay below the radar and evade detection.
Palo Alto Networks Unit 42 stated a malware sample uploaded to the VirusTotal database on May well 19, 2022, contained a payload associated with Brute Ratel C4, a somewhat new refined toolkit “created to prevent detection by endpoint detection and reaction (EDR) and antivirus (AV) abilities.”
Authored by an Indian security researcher named Chetan Nayak, Brute Ratel (BRc4) is analogous to Cobalt Strike and is explained as a “customized command-and-regulate center for red crew and adversary simulation.”
The business application was first launched in late 2020 and has due to the fact attained in excess of 480 licenses across 350 prospects. Every license is supplied at $2,500 per consumer for a calendar year, after which it can be renewed for the exact same duration at the cost of $2,250.
BRc4 is outfitted with a broad range of options, these kinds of as procedure injection, automating adversary TTPs, capturing screenshots, uploading and downloading documents, assistance for various command-and-handle channels, and the potential to keep memory artifacts hid from anti-malware engines, among other people.
The artifact, which was uploaded from Sri Lanka, masquerades as a curriculum vitae of an person named Roshan Bandara (“Roshan_CV.iso”) but in fact is an optical disc picture file that, when double-clicked, mounts it as a Windows generate containing a seemingly harmless Term doc that, on launching, installs BRc4 on the user’s equipment and establishes communications with a remote server.
The delivery of packaged ISO files is usually despatched via spear-phishing email campaigns, although it is really not clear if the exact process was used to deliver the payload to the target setting.
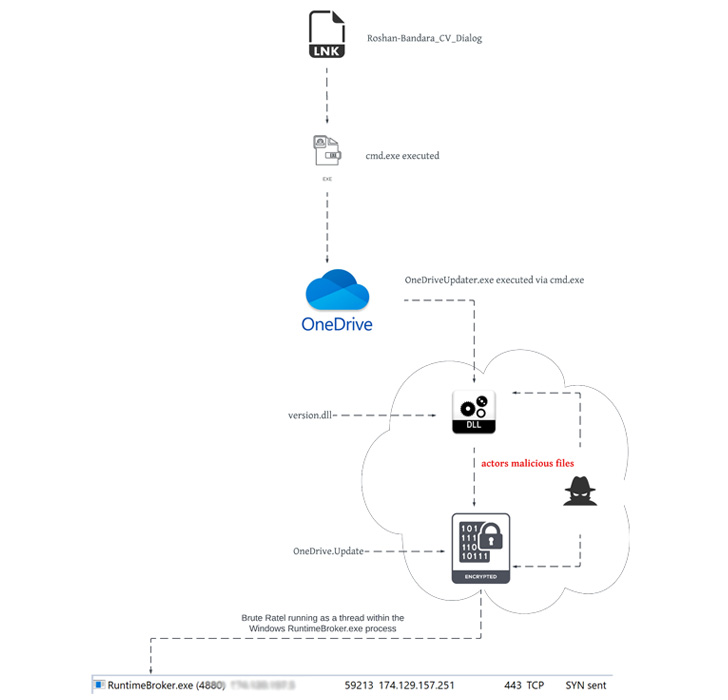
“The composition of the ISO file, Roshan_CV.ISO, carefully resembles that of other nation-point out APT tradecraft,” Device 42 researchers Mike Harbison and Peter Renals reported, calling out similarities to that of a packaged ISO file previously attributed to Russian nation-condition actor APT29 (aka Cozy Bear, The Dukes, or Iron Hemlock).
APT29 rose to notoriety last calendar year following the condition-sponsored group was blamed for orchestrating the large-scale SolarWinds supply chain attack.

The cybersecurity organization pointed out it also spotted a second sample that was uploaded to VirusTotal from Ukraine a working day later on and which exhibited code overlaps to that of a module dependable for loading BRc4 in memory. The investigation has because unearthed seven more BRc4 samples dating back again to February 2021.
By inspecting the C2 server that was utilized as a covert channel, a range of prospective victims have been identified. This features an Argentinian group, an IP tv provider giving North and South American material, and a significant textile company in Mexico.
“The emergence of a new penetration screening and adversary emulation capacity is sizeable,” the researchers reported. “Still much more alarming is the efficiency of BRc4 at defeating fashionable defensive EDR and AV detection capabilities.”
Shortly right after the findings became community, Nayak tweeted that “proper steps have been taken versus the discovered licenses which have been offered in the black market,” adding BRc4 v1.1 “will improve each element of IoC located in the preceding releases.”
Found this post intriguing? Adhere to THN on Fb, Twitter and LinkedIn to go through extra exceptional content material we post.
Some parts of this article are sourced from:
thehackernews.com


 The Morning After: ASUS’ ROG Phone 6 has a clip-on thermoelectric cooler
The Morning After: ASUS’ ROG Phone 6 has a clip-on thermoelectric cooler