A never ever-ahead of-noticed malware-dropper, Clast82, fetches the AlienBot and MRAT malware in a savvy Google Participate in marketing campaign aimed at Android people.
A malware dropper that paves the way for attackers to remotely steal details from Android phones has been spreading by way of nine malicious applications on the official Google Play retail store, in accordance to scientists.
The malware is part of a campaign aimed at lifting victims’ monetary info, but which also permits eventual takeover of mobile telephones, according to Verify Level Research.
The dropper, dubbed Clast82, was disguised in benign apps, which really do not fetch a destructive payload till they have been vetted and cleared by Google Engage in Shield. Google Perform Shield is the store’s evaluation system, meant to weed out apps with sick intent and destructive features.
“During the Clast82 analysis time period on Google Perform, the configuration despatched from the [Google] Firebase [command-and-control server] is made up of an ‘enable’ parameter,” in accordance to Verify Point’s investigation, produced on Tuesday. “Based on the parameter’s price, the malware will choose to induce the destructive actions or not. This parameter is set to ‘false’ and will only alter to ‘true’ immediately after Google has published the Clast82 malware on Google Perform.”
Once ensconced in the App Shop, Clast82 fetches the AlienBot banking trojan, or in some scenarios MRAT, the investigation uncovered.
Data-stealers AlienBot and MRAT
AlienBot is offered in a malware-as-a-services (MaaS) product, and it allows a distant attacker to inject malicious code into authentic financial programs, Examine Point famous.

The Cake VPN app lurking in Google Participate in. Supply: Look at Stage.
“The attacker obtains access to victims’ accounts, and eventually totally controls their gadget,” according to the firm’s analysis. “Upon having manage of a system, the attacker has the capability to management specific functions, just as if they had been holding the system physically, like setting up a new application on the gadget, or even command it with TeamViewer.”
MRAT meanwhile has been all around due to the fact at minimum 2014, when it was employed in opposition to Hong Kong protestors. It was made for reconnaissance and details-accumulating, and athletics all of the usual spyware characteristics, furthermore detection evasion, specific checks for antivirus, application and file deletion operation, and additional.
The payloads had been equally hosted in GitHub. AlienBot was by far the most typical to be delivered to victims.
“In the case of Clast82, we had been ready to detect about 100 exclusive payloads of the AlienBot, an Android MaaS banker focusing on money applications and attempting to steal the qualifications and [two-factor authentication] 2FA codes for all those purposes,” researchers pointed out.
GitHub Assignments Tied to Malicious Android Apps
Verify Point’s evaluation uncovered that for each software, the actor designed a new developer consumer for the Google Enjoy shop, together with a corresponding code repository in GitHub.
“The actor utilized reputable and recognized open up-sourced Android applications, which the actor extra the destructive code into in order to give functionality to the malicious dropper, together with the motive for the target to down load and install it from the formal Google Engage in shop,” the scientists stated.
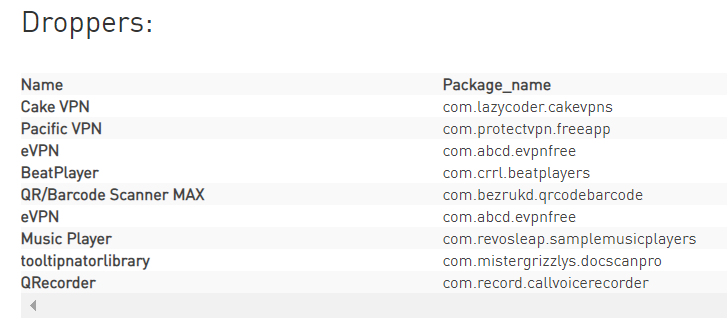
For occasion, the destructive Cake VPN application is primarily based on a genuine GitHub repository.
Across all of the pretend developer accounts on Google Play, there was a one email address outlined for speak to data: sbarkas77590ATgmail.com. Also, each software writeup up used the exact Coverage webpage, which in turn joined to the identical GitHub repository. Clearly, all of the apps have been the operate of a single writer.
Clast82 Malware Infection Move
Typically, one particular exercise in any specified Android app is specified as the “main” activity (MainActivity.java), which is offered to the person when the application is released. In this case, when a consumer launches a Clast82 application, MainActivity starts off a foreground support to execute the malicious dropping activity, Test Position observed.
This services is straightforwardly named “LoaderService.”
“Once a user downloads 1 of the fake apps and launches it, it commences a service from MainActivity that commences a dropping stream termed LoaderService,” researchers discussed. “The foreground provider registers a listener for the Firebase authentic-time databases, from which it receives the payload path from GitHub.”
Android developer policies specify that when an application generates a foreground provider like this, it should show an ongoing notification to the user about what the application is accomplishing.
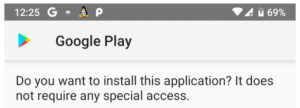
The neutral inform prompting buyers to start out the malware execution circulation. Resource: Test Level
“Clast82 bypassed this by showing a ‘neutral’ notification,” according to Examine Position. “In the scenario of…the Cake VPN application, the notification revealed is ‘GooglePlayServices’ with no added text.”
Meanwhile the app waits for a command from the Firebase C2. When it is instructed to start the “loadAndInstallApp” perform, this downloads the payload from GitHub. Then, it calls the “installApp” method to finalize the malicious action.
If the contaminated device stops installations of applications from mysterious resources, Clast82 prompts the user with a pretend ask for, pretending to be “Google Perform Solutions.” These fake requests will pop up each and every 5 seconds.
Infected Clast 82 Programs for Android
Right after Examine Point Exploration described its conclusions to the Android Security group, Google confirmed that all Clast82 apps were being eradicated from the Google Play Retailer. On the other hand, victims with the apps previously put in keep on being at risk. The affected applications are as follows:
- BeatPlayer
- Cake VPN
- Two versions of eVPN
- Tunes Participant
- Pacific VPN
- QR/Barcode Scanner MAX
- QRecorder
- tooltipnattorlibrary
Check out out our free upcoming are living webinar events – unique, dynamic conversations with cybersecurity professionals and the Threatpost community:
- March 24: Economics of -Working day Disclosures: The Superior, Undesirable and Hideous (Find out extra and sign-up!)
- April 21: Underground Marketplaces: A Tour of the Dark Financial state (Study extra and register!)
Some parts of this article are sourced from:
threatpost.com


 This Alexa-enabled smart ring light from GE is on sale for 55 percent off
This Alexa-enabled smart ring light from GE is on sale for 55 percent off