Tens of millions of texts top to the Flubot spy ware/banking trojan are targeting anyone who works by using Androids in the region, in an “exceptional” attack.
The Flubot banking trojan is blanketing Finland, spreading by way of Android phones that are sending millions of malicious textual content messages.
On Friday, the Countrywide Cyber Security Centre (NCSC-FI) at the Finnish Transport and Communications Company posted a “severe” warn about the malware blizzard, which it mentioned was spreading via dozens of concept variants that are sneezing out Flubot like mad.
When set up, Flubot sets about gaining permissions, thieving banking data and credentials, lifting passwords saved on the product and squirreling away numerous items of personal info. It also sends out additional textual content messages to the infected device’s call list, which allows it to “go viral” — like the flu.
“An Android malware referred to as Flubot is remaining unfold by SMS. According to our present estimate, tens of countless numbers of messages have been sent to persons in Finland for the duration of a single working day. We be expecting the amount to maximize in the coming days and months,” reported Aino-Maria Väyrynen, details security adviser at the NCSC-FI, in the alert.
It Started out Not-Gradual & Ongoing to Develop-Develop-Increase
The campaign did in fact get significantly extra virulent, just as Väyrynen predicted: In an article published early Tuesday early morning, Väyrynen was quoted by Bloomberg as stating that the each day messages now quantity in the tens of millions.
The country’s major telecom companies told the information outlet that they’ve intercepted hundreds of hundreds of messages. Teemu Makela, CISO at Elisa Oyj, called the attack “extremely extraordinary and incredibly worrying.”
When Androids, iPhones, And so forth. Attack
The NCSC-FI’s advisory reported that the malware is focusing on “everyone making use of an Android system and a cellular subscription,” while iPhones and other products “are directed to other fraudulent materials on the website.”
The destructive textual content messages are making use of come-ons that explain to targets that they’ve obtained a voicemail or a concept from their cell operator. All of the variant messages check with the recipient to open up a malicious website link.
The url does not set up the malware suitable off the bat: Instead, targets are prompted to grant voicemail permissions, which is really a entrance for malware set up. Then, once put in, the malware steals knowledge from the gadget and sends malware-spreading rip-off messages in the background.
There are telltale crimson flags: The messages “are frequently penned with no Scandinavian letters (å, ä and ö) and could have the figures +, /, &, % and @ in random and illogical spots in the text,” the advisory defined.
Finnish authorities shared illustrations of the messages, as properly as the malware’s set up ask for, both equally of which are revealed down below.
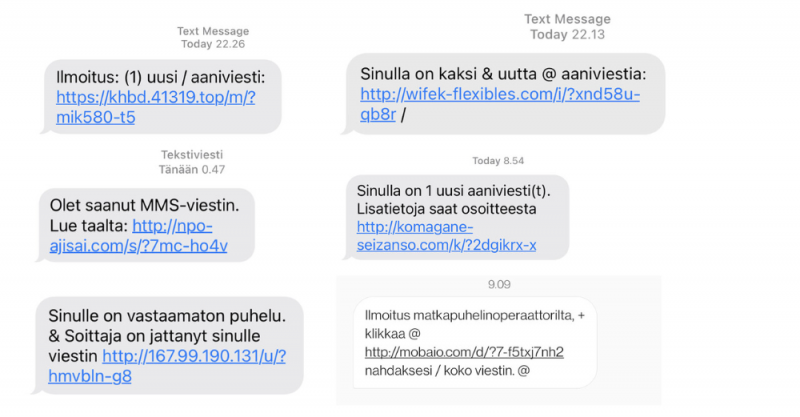
Examples of fraudulent textual content messages. Supply: NCSC-FI.
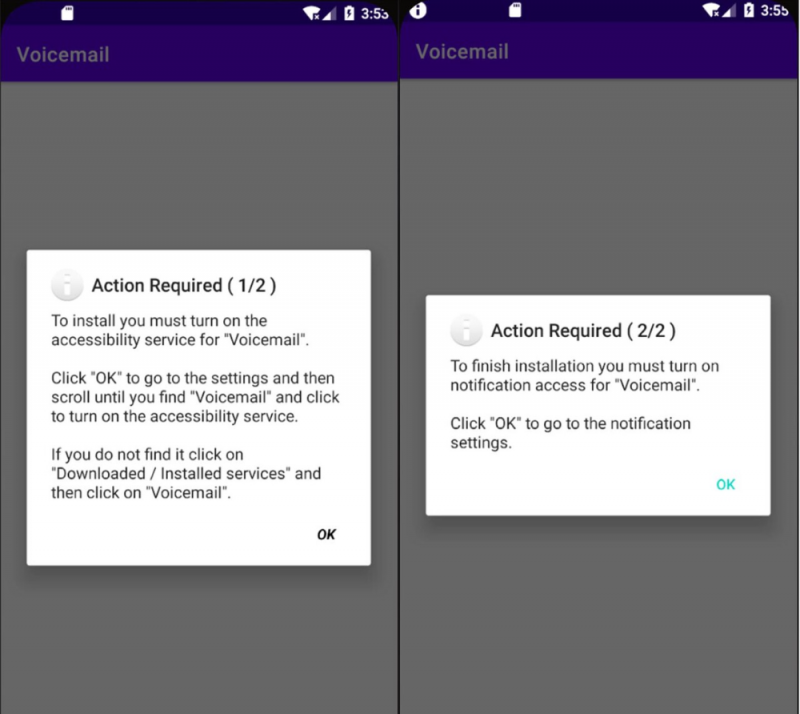
The malware’s set up request. Supply: NCSC-FI.
No Immunity Received Soon after Earlier Flubot Marketing campaign
This is the 2nd time that Flubot has buffeted Finland. A Flubot cellular malware marketing campaign was unleashed in Finland in June 2021 and persisted into August, sending messages prepared in Finnish to thousands of Finns. In that before marketing campaign, the destructive messages reported that there was a package in shipping and delivery and involved a monitoring connection that tried out to entice targets to a fraud web site that tried out to install Flubot.
That time, many thanks to cooperation in between the authorities and telecoms, the NCSC-FI claimed that the country managed to eradicate Flubot “almost completely.”
Antti Turunen, fraud supervisor at Swedish telco Telia (which operates in Finland) instructed Bloomberg that this time it’s even worse — a sentiment shared by the NCSC-FI. The new wave exhibits that the Flubot operators have mutated their malware to hook its tentacles into victims regardless of the management actions place in area to eradicate the summer Flubot marketing campaign, the security middle said.
Flubot generally switches up techniques: In October for occasion, the banking trojan was found employing a fake security warning to test to trick Android customers into pondering that they’d currently been contaminated … with Flubot.
It was a lie, but it became a truth for recipients of the textual content concept who clicked on the “install security update” button.
Menace Intel Is ‘King’ to Protect Against These Attacks
Hank Schless, senior supervisor of security remedies at Lookout, explained to Threatpost by way of email on Tuesday that Finland’s plight is an case in point of “the complications that the malware-as-a-company (MaaS) current market makes for people and enterprises alike.”
This marketplace has made malware and phishing kits “incredibly accessible for even the least experienced threat actors,” he explained. “Usually, for a incredibly smaller cost, someone can go on line and discover one particular of these kits thoroughly developed and all set to be employed. Once they receive the package, all the attacker wants to do is host it on a web area then make a delivery system. Most often, this mechanism is some variety of concept concentrating on mobile consumers mainly because of the amount of strategies you can supply a message to these products through SMS, email, social media platforms, third get together messaging applications, gaming and even courting apps.”
The only change among Finland’s before Flubot campaign and this a single are the distinctive social-engineering hooks, he mentioned – a indication of how “socially engineered phishing attacks can proceed to be productive around time.”
Phishing has become “the most about issue for each individual enterprise,” Schless observed. “Threat actors not only use it to steal login qualifications, but supply malware to gadgets and infrastructure as well. Lookout facts shows that menace actors seriously goal buyers by means of mobile channels these kinds of as SMS, social media platforms, 3rd social gathering messaging apps, gaming and even dating apps.”
He pointed to Lookout knowledge demonstrating that there was an regular quarterly publicity charge to phishing attacks of 15.35 per cent about the to start with 3 quarters of 2021: A jump from the 10.25 per cent exposure rate the company tracked in the very first a few quarters of 2020.
“Phishing is obviously a expanding issue for every organization,” he said.
Even though this Flubot marketing campaign targets people, the similar methods are employed to goal enterprise corporations, Schless claimed: For example, the attacker’s bait message could say that a target’s Outlook or Salesforce login were being compromised, luring them to a fake login web page with the intention of stealing their company login credentials.
“Once the attacker has individuals compromised qualifications, they’re free to log in to any corporate app and shift laterally by way of the infrastructure,” Schless continued. “This could lead to them exfiltrating or encrypting knowledge for an eventual ransomware attack.”
He concluded by calling risk intel “king” when it arrives to shielding against attacks like this. “Solutions backed by datasets with more than enough danger telemetry are the only way to detect and guard from these assaults before they can even achieve the conclusion user,” he claimed. “Since these campaigns usually run for a small amount of time, traditional security solutions will be way too slow on the uptake. Pushing automated coverage towards assaults like this as the malicious web site when it’s being developed, is the only way to mitigate the gap in safety.”
What to Do If You’ve Been Flubotted
The NCSC-FI provided guidance on what to do if your gadget has been contaminated with Flubot. Warning: The medication is bitter.
The simplest way to cure the ailment is to accomplish a manufacturing facility reset as before long as doable, the security heart explained. When restoring from backup, make sure to use a backup that dates again to pre-an infection, the advisory suggested.
It gave these additional instructions, meant to continue to keep the Flubot banking trojan from rampaging by way of monetary accounts:
- If you used a banking software or managed credit history card information and facts on the contaminated gadget, speak to your lender.
- Report any economical losses to the law enforcement.
- Reset your passwords on any products and services you have employed with the system. The malware could have stolen your password if you have logged in following you set up the malware.
- Get hold of your operator, because your subscription might have been utilised to send out text messages subject matter to a cost. The at the moment lively malware for Android units spread by sending textual content messages from contaminated equipment.
There is a sea of unstructured info on the internet relating to the hottest security threats. Register Currently to master key ideas of natural language processing (NLP) and how to use it to navigate the knowledge ocean and include context to cybersecurity threats (without having staying an specialist!). This Dwell, interactive Threatpost Town Corridor, sponsored by Fast 7, will characteristic security researchers Erick Galinkin of Quick7 and Izzy Lazerson of IntSights (a Fast7 organization), furthermore Threatpost journalist and webinar host, Becky Bracken.
Sign-up NOW for the Are living function!
Some parts of this article are sourced from:
threatpost.com


 Panasonic’s Data Breach Leaves Open Questions
Panasonic’s Data Breach Leaves Open Questions