A new attack campaign has qualified the gaming and gambling sectors considering that at the very least September 2022, just months prior to the ICE London 2023 gaming business trade reasonable celebration which is scheduled next 7 days.
Israeli cybersecurity company Security Joes is monitoring the action cluster under the title Ice Breaker, stating the intrusions make use of clever social engineering practices to deploy a JavaScript backdoor.
The attack sequence proceeds as follows: The threat actor poses as a client even though initiating a conversation with a help agent of a gaming website and urges the unique on the other close to open up a screenshot graphic hosted on Dropbox.
Security Joes claimed that the menace actor is “properly-conscious of the point that the shopper support is human-operated.”
Clicking the destructive backlink despatched in the chat leads to the retrieval of an LNK payload or, alternatively, a VBScript file as a backup choice, the previous of which is configured to obtain and operate an MSI deal containing a Node.js implant.
The JavaScript file has all the options of a normal backdoor, enabling the threat actor to enumerate running procedures, steal passwords and cookies, exfiltrate arbitrary documents, acquire screenshots, operate VBScript imported from a remote server, and even open up a reverse proxy on the compromised host.
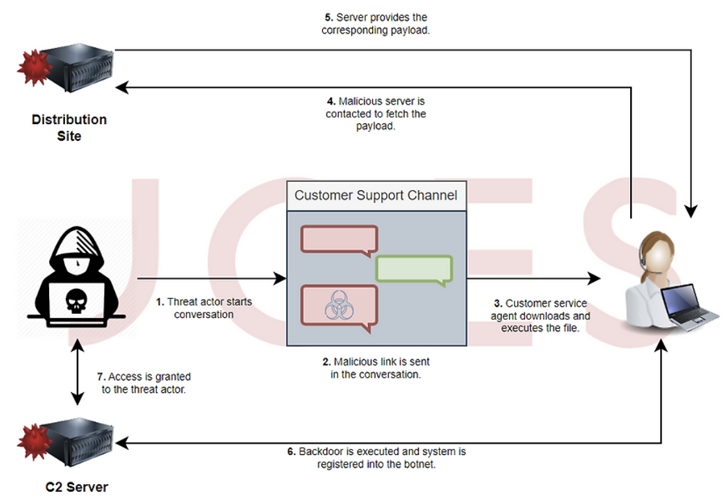
Need to the VBS downloader be executed by the victim, the infection culminates in the deployment of Houdini, a VBS-based mostly distant access trojan that dates again to 2013.
The risk actors’ origins are now unidentified, despite the fact that they have been observed using broken English throughout their discussions with purchaser provider agents. Some indicators of compromise (IoCs) associated with the campaign have been previously shared by the MalwareHunterTeam in Oct 2022.
“This is a remarkably productive attack vector for the gaming and gambling sector,” Felipe Duarte, senior threat researcher at Security Joes, stated.
“The in no way-observed-ahead of compiled JavaScript 2nd phase malware is remarkably intricate to dissect, displaying that we are dealing with a skilled danger actor with the potential of being sponsored by an interest proprietor.”
Located this short article intriguing? Observe us on Twitter and LinkedIn to read through far more exclusive material we article.
Some parts of this article are sourced from:
thehackernews.com


 BEC Group Uses Open Source Tactics in Hundreds of Attacks
BEC Group Uses Open Source Tactics in Hundreds of Attacks