As quite a few as 75 apps on Google Engage in and 10 on Apple Application Retail outlet have been found out engaging in ad fraud as aspect of an ongoing marketing campaign that commenced in 2019.
The hottest iteration, dubbed Scylla by On the web fraud-prevention organization HUMAN Security, follows comparable attack waves in August 2019 and late 2020 that go by the codename Poseidon and Charybdis, respectively.
Prior to their removing from the app storefronts, the apps experienced been collectively set up far more than 13 million instances.

The unique Poseidon operation comprised over 40 Android apps that were intended to show adverts out of context or hidden from the view of the device person.
Charybdis, on the other hand, was an improvement above the previous by creating use of code obfuscation strategies to target advertising platforms.
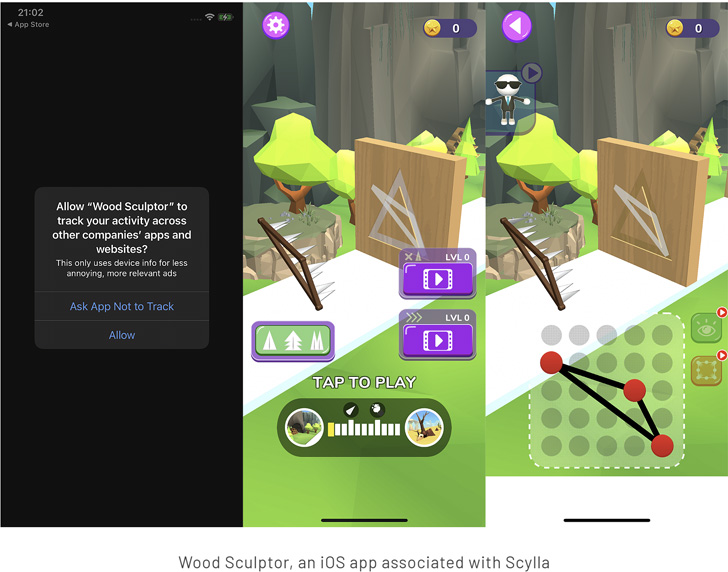
Scylla presents the latest adaption of the plan in that it expands past Android to make a foray into the iOS ecosystem for the 1st time, together with relying on supplemental levels of code roundabout utilizing the Allatori device.
These applications, after put in, are engineered to commit distinct forms of ad fraud, marking a major action up in sophistication from past variants.
These include things like spoofing popular apps this sort of as streaming providers to trick promotion SDKs into putting advertisements, serving out-of-context and “hidden” ads by way of off-display screen WebViews, and making fraudulent advertisement clicks to earnings off adverts.
“In layman’s conditions, the menace actors code their applications to fake to be other apps for marketing needs, generally for the reason that the application they are pretending to be is worthy of more to an advertiser than the application would be by alone,” the firm claimed.
As generally, end users are suggested to scrutinize applications prior to downloading them, and stay away from 3rd-celebration application merchants on the web that could harbor malicious apps.
Found this post fascinating? Stick to THN on Fb, Twitter and LinkedIn to read through additional exclusive articles we article.
Some parts of this article are sourced from:
thehackernews.com


 The Morning After: Netflix is building its own game studio
The Morning After: Netflix is building its own game studio