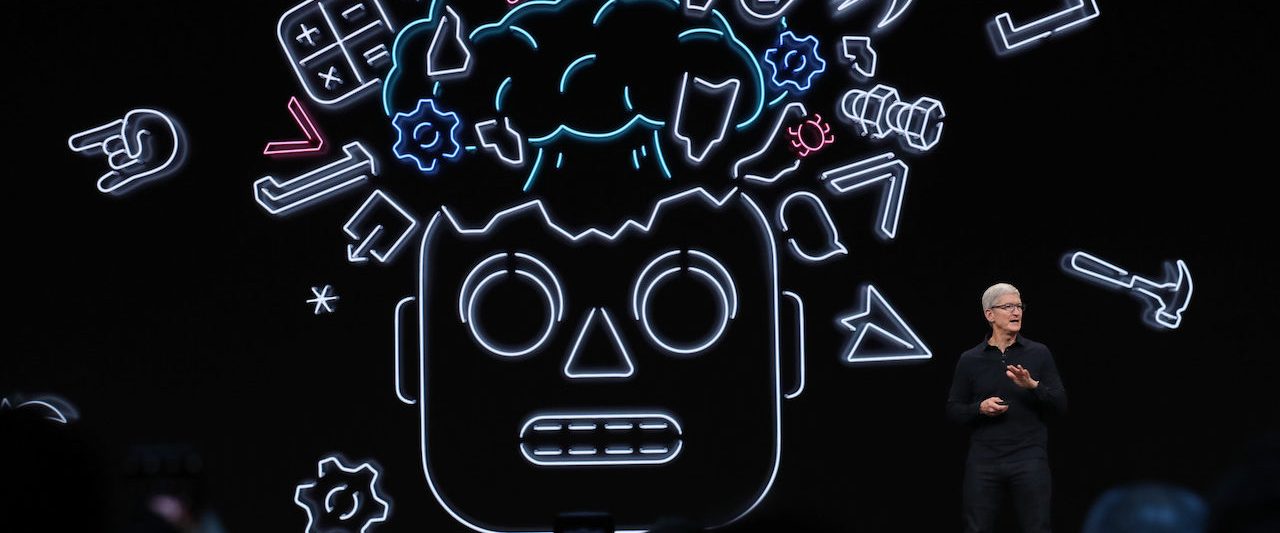
Apple CEO Tim Cook delivers the keynote deal with in the course of the 2019 Apple Worldwide Developer Meeting (WWDC) at the San Jose Convention Centre on June 03, 2019 in San Jose, California. New investigation found that most enhancement teams, 81%, experienced knowingly pushed flawed code stay.(Image by Justin Sullivan/Getty Photographs)
Confused and source-starved application builders are approving vulnerable code and pushing it into reside purposes in alarming quantities, according to a new research report.
Similarly troubling: 44% of polled security groups mentioned they doubted their application develop natural environment is safe plenty of to repel a devoted attacker’s endeavor at a compromise, these kinds of as the 1 that SolarWinds experienced last calendar year.
The report, from Immersive Labs and Osterman Analysis, drew its conclusions from a survey of 260 enhancement and security groups in large companies. Most growth teams, 81%, discovered they experienced knowingly pushed flawed code are living, and 20% senior of managers even admitted to committing this unsafe follow often.
The disappointing study responses illustrate some of the causes why President’s Biden’s executive purchase on cybersecurity is looking for to build cures for program vulnerabilities.
“The actuality that protected program growth is given these prominence in the EO in the wake of the Colonial Pipeline attack is a good indicator and underlines a rising acceptance of its worth as a risk issue,” said Sean Wright, principal application security engineer at Immersive Labs, in emailed reviews. “Unfortunately, our exploration that just went stay these days shows there is a great deal of challenging function in advance to realize the wanted society of security in application development. With the vast majority of developers admitting to knowingly pushing vulnerable code are living, it underlines the truth that security is however not presented priority.”
The report exposes a number of key complications that can impede or introduce risk into the application enhancement lifecycle. For occasion, only 39% of security groups said they have sufficient time and sources to commit to shifting remaining.
Specifically troubling: Immersive Labs noticed a “worrying disconnect” concerning entrance-line builders and their administrators. Indeed, only 27% of the former team said they agreed that security is amid their responsibilities, though 80% of the latter team did.
“If the people today producing the code really do not feel it’s essential, it is tricky to make development,” said Chris Eng, main investigate officer at Veracode. “It’s good that 80% of advancement administrators truly feel some feeling of ownership for security, but they obviously are not carrying out a quite fantastic occupation of holding builders accountable.”
Immersive Labs’ conclusions appear to guidance preceding research attempts that have also highlighted the prevalence of software flaws.
“Veracode’s very own analysis observed that 76% of apps consist of at minimum 1 security vulnerability, and 71% inherit at the very least just one vulnerability from open-resource libraries,” Eng continued. “We also know that in about fifty percent of all programs, builders are introducing new security flaws a lot quicker than they are repairing current types. So it’s not at all surprising that this 81% of development teams in this study admitted to transport recognized vulnerable merchandise.”
Robert Haynes, open source and software composition analysis evangelist at Checkmarx, said that the study outcomes “just go to clearly show how far we as an market have to go to make security a foundational element of computer software excellent. Till the security of the solutions that advancement groups are manufacturing is found by all people as intrinsic to good quality of operate, we are going to continue on to see these sorts of disconnects.”
Haynes ongoing: If these results appear surprising, talk to you: How many progress teams would be celebrated for halting an urgent create or release in the title of security? If we believe that that security is essential to application high quality – as we should really – we will need to understand the lessons of quality-centered production techniques, in which behaviors that increase very long-expression top quality and integrity are rewarded, even if this usually means prioritizing security about speed of manufacturing in sure instances.”
But this will demand a culture change. Improved equipment and teaching can aid accelerate the transformation, explained Haynes – primarily when they help spotlight security issues in an automatic and friction-cost-free way. But this kind of products and services “must also be coupled with companywide obtain-in and an authentic alter in the way improvement teams and corporations imagine about and strategy application high quality.”
Some parts of this article are sourced from:
www.scmagazine.com

 Volkswagen targets fully autonomous electric taxi vans by 2025
Volkswagen targets fully autonomous electric taxi vans by 2025