A year right after COVID-19 was formally established to be a pandemic, the procedures and practices applied by cybercriminals have considerably changed.
COVID-19-relevant phishing emails, brute-drive attacks on distant staff, and a emphasis on exploiting or abusing collaboration platforms are the hallmarks of cybercriminal business as the coronavirus marks its 1st anniversary of going international.
A calendar year following the COVID-19 crisis was formally identified to be a pandemic, the way people reside and function has radically transformed – and so have “the procedures and methods employed by criminals on the internet seeking to exploit the significant increase in on the net targeted visitors,” according to a report from Kaspersky, issued on Monday.
Phishing Ripoffs Exploit COVID-19 Themes
Email scamming (and phishing in specific) is continue to 1 of the most successful forms of assaults in the coronavirus period, in accordance to Kaspersky, considering that panic and anxiety are two of the most-exploited thoughts for this kind of social-engineering attack.
Strategies these kinds of as those purporting to offer N95 masks or hand sanitizer (which prompted people to put in their payment aspects) became endemic around the class of the yr. Impersonating COVID-19 authorities was also a poplar gambit, with cybercriminals offering “important” updates. In fact, all they have been providing was malware.
“In 2020, criminals released a range of frauds that exploited the pandemic subject matter from just about each individual angle, from advertisements to masks when they ended up in brief offer to exclusive refunds from the authorities,” in accordance to the report. “Scammers typically imitated primary authority figures on the pandemic, like the CDC and the World Health Group, to give their emails extra authority — and improve the chances that customers would click a malicious hyperlink.”
Cybercriminals also utilised lures involving delayed shipments – taking benefit of the reality that ordering by mail skyrocketed throughout lockdowns. In 2020, shipping and delivery products and services entered the leading 10 most-spoofed corporations for these kinds of attacks, according to Kaspersky.
“They would send e-mail declaring that, due to COVID, an critical shipping and delivery experienced been delayed and that the focus on ought to verify the new shipping facts (a circumstance easy to believe in the middle of a pandemic) in buy to get it,” in accordance to the report. “However, on clicking the attachment, the people would down load trojans ranging from adware to backdoors.”
Brute-Pressure Attacks on Distant Workers
As hundreds of thousands of employees had been despatched household to get the job done remotely in 2020, cybersecurity steps ended up an afterthought for quite a few companies. Cybercriminals, suspecting this, focused personnel logging in to company resources from own units and on unsecured house networks, according to the assessment.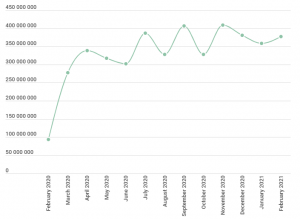
Specifically, brute-drive attacks (the place attackers consider random usernames and passwords in opposition to accounts) on Distant Desktop Protocol (RDP) connections ramped up globally, surging 197 p.c from 93.1 million globally in February to 277.4 million in March. RDP is Microsoft’s proprietary protocol that allows customers to entry Windows workstations or servers.
“RDP is one of the most well known distant-obtain protocols utilized by companies, producing it a favorite focus on for attackers,” according to the report. “In spring of 2020, the variety of brute-drive attacks from the RDP protocol skyrocketed across nearly the complete world.”
A calendar year afterwards, the number of assaults has not returned to pre-pandemic concentrations, Kaspersky noted: In February, there had been 377.5 million brute-force assaults.
Cyberattacks on Collaboration Platforms Ramp Up
Cyberattackers have also gone just after customers of various cloud services, in particular collaboration services like Flock, GotoMeeting, HighFive, Sign up for.me, Lifesize, MS Groups, Slack, Webex and Zoom. Kaspersky identified that by May possibly of last year, the typical every day number of attacks on these products and services seen in its telemetry experienced jumped 25 p.c just due to the fact February 2020.
These much too have not definitely abated.
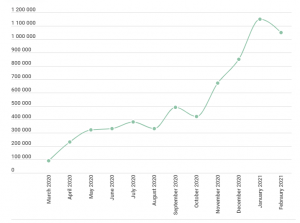
Collaboration attacks more than the previous year. Click to enlarge. Supply: Kaspersky.
“The range of web attacks, following displaying a decline in the summertime of 2020, reached a new peak in December as much of the world was dealing with a next wave of the pandemic,” in accordance to Kaspersky. “A large part of users’ time invested on the web was focused to assembly and collaborating practically. That is why meeting and messenger apps, like Zoom and Teams, became a preferred lure for distributing cyberthreats.”
Most of these attacks contain destructive files currently being distribute beneath the guise of these apps’ names, Kaspersky discovered that in January, there had been 1.15 million these types of documents detected — the greatest number considering the fact that the lockdown began.
“These information are normally bundled as portion of seemingly reputable application installers, which can be encountered in many means: By phishing e-mails saying to have notifications or specific features from their platforms or by way of phishing web pages,” in accordance to the report.
What’s Upcoming for COVID-19 Cyberattacks?
With the pandemic heading into a new stage involving vaccinations, there is also a new crop of matters for phishers and scammers to exploit, like overall health passports for travel or vaccine distribution, Kaspersky warned.
“Chances are they will exploit them,” according to the report. “It is essential that customers look at any email or web site referencing the pandemic with a skeptical eye. What is more, recent events have demonstrated how keen criminals are to take benefit of disaster, and, although this pandemic will subside, it surely will not be the last crisis.”
The report also mentioned that remote functioning will possible remain in area even post-pandemic.
“RDP is not going everywhere — and neither are assaults towards the protocol,” the report concluded. “That suggests companies will need to reevaluate their utilization of RDP and learn how to protected distant obtain. If there is has ever been a time for firms to reevaluate and bolster their security system, that time is now.”
Microsoft’s probe comes amidst news that ransomware gangs are starting up to acquire purpose at the Exchange Server vulnerabilities, adding a new sense of urgency to the will need for organization to apply patches and disinfect backdoors from networks.
Test out our free upcoming dwell webinar events – special, dynamic conversations with cybersecurity experts and the Threatpost local community:
- March 24: Economics of -Working day Disclosures: The Very good, Terrible and Unsightly (Master far more and sign up!)
- April 21: Underground Markets: A Tour of the Dark Financial system (Find out extra and sign up!)
Some parts of this article are sourced from:
threatpost.com

 Facebook sextortionist sentenced to 75 years in prison
Facebook sextortionist sentenced to 75 years in prison