Present day password policies are comprised of lots of unique features that contribute to its success. A single of the parts of an efficient latest password coverage would make use of what is recognised as a customized dictionary that filters out selected terms that are not permitted as passwords in the ecosystem.
Using customized dictionaries, companies can significantly strengthen their cybersecurity posture and filter out apparent passwords that offer very poor security for person accounts.
When working with password dictionaries in your password policy, there are many various ways to take into consideration. 1st, let’s take into account crafting a tailor made dictionary for your password policy, including normal assistance on how these are made, configured, and how you can simply use customized dictionaries in an energetic listing setting.
Why customize your dictionary?
Tailor made dictionaries are born from the require to “imagine as a hacker thinks.” Compromised credentials are one of the foremost causes of malicious data breaches throughout the board. They are also just one of the most high priced to businesses. IBM’s Charge of a Information Breach Report 2020, compromised credentials amplified the typical total value of a breach by nearly $1 million to $4.77 million.
Hackers generally use credential-primarily based assaults to compromise weak passwords, passwords that have been earlier breached, common passwords used in a unique small business sector, or typical spelling transformations.
Sad to say, all of us tend to use passwords that we can easily try to remember. In addition, finish-consumers often include widespread numbers or image patterns to the commencing or finish of passwords to get all around password complexity requirements.
Both equally human mother nature and the technology instruments offered make it possible for easily cracking or guessing weak, common, or envisioned passwords. Even though attackers have accessibility to huge databases of breached and or else popular or weak passwords, the “very good men” can apply a password file in a excellent way – the custom dictionary.
The custom password dictionary is effective in favor of securing the passwords in your atmosphere.
When carried out, the personalized dictionary gives a implies to filter the picked out password or finish-customers in this sort of a way as to disallow passwords or variations of the passwords contained in the customized dictionary.
So, aren’t all passwords that meet the Energetic Listing Password Coverage prerequisites safe? Not precisely.
Though password policy demands outlined by Energetic Directory Password Policy are a superior commencing point, they leave substantially to be preferred when taking into consideration the cracking and other password equipment that cybercriminals are utilizing currently.
As an illustration, a password plan may perhaps require that an end-user fulfill the following necessities:
- Minimum amount of 8 people
- Password ought to fulfill complexity requirements (Should consist of uppercase, lowercase, numbers, and non-alphabetic figures such as symbols)
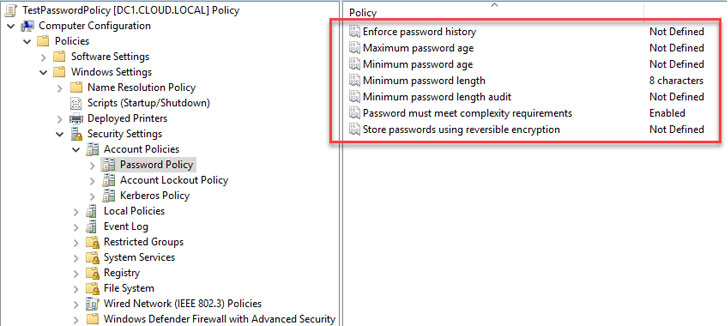 A password policy outlined in Energetic Directory Area Providers
A password policy outlined in Energetic Directory Area Providers
Employing the native Active Listing Password Coverage settings above, a person could most likely set passwords these types of as:
- P@$$w0rd123
- MybusinessName123!
- Letmein1$
The above passwords satisfy all the criteria defined as element of the size and complexity necessities.
Nonetheless, they are weak and quickly guess thanks to various explanations. As the higher than examples display, these could be identified variants of prevalent phrases such as “Password,” relevant to your specific enterprise identify or sector, or a widespread phrase contained in a cracked password databases this sort of as “Letmein1$.”
Downloadable tailor made password dictionaries
You may possibly not want to “reinvent the wheel” when it will come to collecting passwords to use in a personalized dictionary for your password policy. There are out-of-the-box password dictionaries and password files that can be freely downloaded as the foundation for a custom password dictionary. An case in point features the Have I Been Pwned password record: Have I Been Pwned: Pwned Passwords.
Businesses can also use easily obtainable applications these kinds of as Crunch, offered in Kali Linux or installable from your Linux distribution repository. In Ubuntu, you can install Crunch making use of the command:
- sudo apt-get install crunch
It enables building a wordlist that can be made use of for brute power or password energy auditing by SecOps teams in your corporation. In addition, these quickly accessible equipment can supply the foundation for producing your very own tailor made password lists in your setting.
Utilizing a Password filter .dlls
On the other hand, there is additional associated than only developing a password dictionary file. Organizations that want to carry out their personal personalized password filter .dll, along with words that contains their enterprise title or business-distinct keyword phrases, have to have the improvement expertise and assets offered to produce the .dll file essential for the password filter performance in Active Listing.
Microsoft outlines the approach of registering and putting in a password filter .dll in this article: Putting in and Registering a Password Filter DLL – Gain32 applications | Microsoft Docs.
Custom dictionary answers in your password coverage equipment
Is there an straightforward way to craft a personalized dictionary for your password coverage? Specops Password Policy usually takes the tougher get the job done out of utilizing personalized dictionaries for your password insurance policies and enables for the negation of about 2 billion recognized breached passwords moreover any custom made phrases like your company title, or locale, to be included to a password coverage device.
Superior-good quality password policy applications like this integrate with your indigenous Active Listing Password Guidelines applied at the Team Policy level.
With simple checkboxes, the Specops answer makes it possible for IT admins to conveniently and immediately put into practice several password dictionaries as element of the password guidelines configured for their business.
 Specops Password Plan dictionary options
Specops Password Plan dictionary options
 Configuring the personalized dictionaries location in Specops Password Plan
Configuring the personalized dictionaries location in Specops Password Plan
Configuring the Use custom made dictionaries enables importing password files, hash files, or making new dictionaries proper from the interface.
Under the downloaded dictionaries configuration, admins have access to commonly readily available password dictionary files that can be downloaded directly from the Specops Password Plan interface.
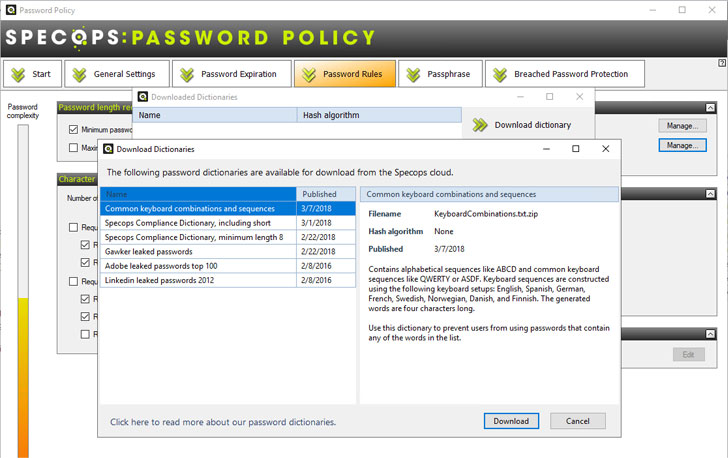 Downloading password dictionary data files from the Specops Password Plan interface
Downloading password dictionary data files from the Specops Password Plan interface
Specops Password Plan makes configuring, utilizing, and retaining personalized dictionary data files for your organization’s password coverage easier—with no programming expertise or knowledge essential.
Get started out employing a custom made dictionary in your password plan
Companies nowadays need to bolster the security of account passwords to fortify their total cybersecurity posture. Making use of custom dictionaries as portion of their password policies is a excellent way to factor in an offensive technique to your cybersecurity attempts.
Having said that, implementing a personalized password filter .dll in the environment necessitates producing the tailor made password filter .dll file expected by Energetic Listing. This progress can existing roadblocks to corporations applying personalized dictionaries like cost, servicing, and performance blockers.
Specops Password Policy lets implementing many custom made dictionary files with just a handful of clicks, doing away with the complexity and security issues associated with utilizing this correctly.
Find out additional about Specops Password Coverage or get started your cost-free trial.
Found this article intriguing? Adhere to THN on Fb, Twitter and LinkedIn to read through much more exclusive content material we submit.
Some parts of this article are sourced from:
thehackernews.com


 Hackers Spread BIOPASS Malware via Chinese Online Gambling Sites
Hackers Spread BIOPASS Malware via Chinese Online Gambling Sites