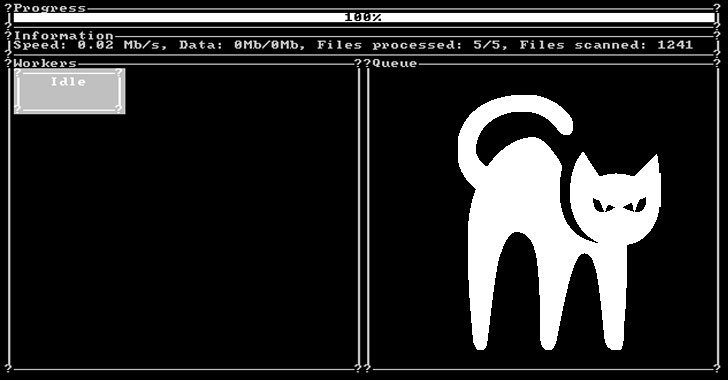
Aspects have emerged about what’s the first Rust-language-based ransomware strain spotted in the wild that has currently amassed “some victims from unique nations around the world” given that its start last month.
The ransomware, dubbed BlackCat, was disclosed by MalwareHunterTeam. “Victims can pay out with Bitcoin or Monero,” the scientists mentioned in a collection of tweets detailing the file-encrypting malware. “Also looks they are offering qualifications to intermediaries” for negotiations.
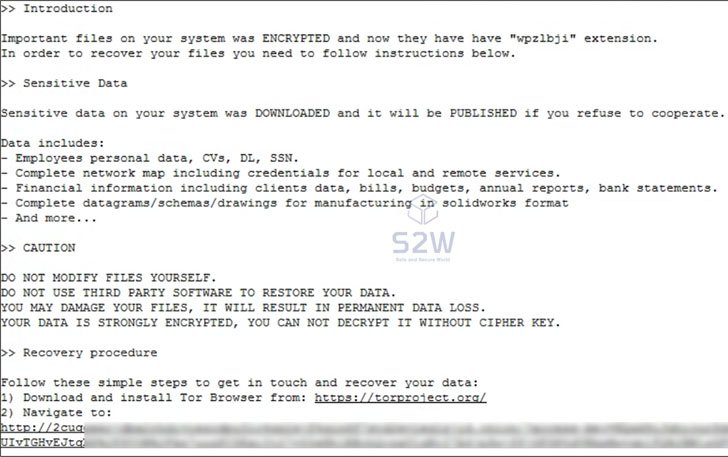
BlackCat, akin to numerous other variants that have sprung before it, operates as a ransomware-as-a-provider (RaaS), whereby the core builders recruit affiliates to breach corporate environments and encrypt files, but not prior to stealing the said paperwork in a double extortion scheme to tension the targets into spending the requested sum or risk exposure of the stolen details must the organizations refuse to pay up.
Security researcher Michael Gillespie referred to as it a “really sophisticated ransomware.”
South Korean cybersecurity business S2W, in a separate evaluation of BlackCat, said that the ransomware conducts its destructive actions by referring to an inner configuration like other RaaS programs, contacting out its similarities with BlackMatter, an additional ransomware that emerged from the ashes of DarkSide in July only to sunset its things to do in early November.
Even though it’s standard of ransomware teams to go underground, regroup, and resurface under a new title, the scientists cautioned against contacting BlackCat a BlackMatter rebrand, citing variations in the programming language applied (Rust vs. C++), the myriad execution choices, and the dark web infrastructure taken care of by the actor.
BlackCat, commencing December 4, 2021, has been advertised on Russian-language underground marketplaces like XSS and Exploit less than the username “alphv” and as “ransom” on the RAMP discussion board in a bid to recruit other participants, including penetration testers, and sign up for what it named “the subsequent era of ransomware.”
The ransomware actor is also mentioned to be running 5 onion domains, a few of which functionality as the group’s negotiation site, with the relaxation classified as an “Alphv” community leak website and a private leak site. Only two victims have been identified so much, suggesting that the nascent ransomware is currently being actively deployed versus providers in true-earth attacks.
“Right after details about the BlackCat ransomware and Alphv leak web page was exposed on Twitter, they deleted all details of both two victims and included their warning message on Alphv leak internet site,” S2W researchers observed.

The development alerts a increasing craze where risk actors are adopting lesser-acknowledged programming languages such as Dlang, Go, Nim, and Rust, to bypass security protections, evade evaluation, and hamper reverse engineering initiatives.
Rust is also attaining traction for its ability to achieve high-general performance compared to that of languages such as C and C++, although simultaneously presenting memory basic safety assures that could be leveraged to build malware that is a lot less inclined to exploitation and render them powerless.
Observed this article fascinating? Stick to THN on Fb, Twitter and LinkedIn to study additional special information we publish.
Some parts of this article are sourced from:
thehackernews.com

 Apple's third-gen AirPods fall to an all-time low of $140
Apple's third-gen AirPods fall to an all-time low of $140