Container technology has received traction amid corporations due to the increased effectiveness it supplies. In this regard, corporations extensively use Kubernetes for deploying, scaling, and taking care of containerized apps. Corporations need to audit Kubernetes to guarantee compliance with polices, obtain anomalies, and identify security pitfalls. The Wazuh open source platform performs a critical job in checking Kubernetes and other elements of an organization’s infrastructure.
What is Kubernetes?
Kubernetes is an open resource container management answer that automates the deployment and scaling of containers and also manages the existence cycle of containers. It organizes containers into sensible models for straightforward administration and discovery. Kubernetes extends how we scale containerized purposes so that we might use a genuinely persistent infrastructure.
You can establish cloud-native applications centered on microservices with Kubernetes. Lovers view Kubernetes as the cornerstone of software modernization. It enables the containerization of latest applications, permitting builders to generate applications immediately.
The complexity of managing plans grows when they unfold across quite a few servers and containers. To tackle this complexity, Kubernetes offers an open up supply API that manages exactly where and how all those containers will execute. Kubernetes incorporates load balancing, controls services discovery, retains monitor of source allocation, and scales based on compute use. Moreover, it assesses the problem of every single resource and gives systems the ability to self-fix by replicating containers or restarting them automatically.
Auditing Kubernetes
There are various guidelines that corporations really should comply with, based on the jurisdiction and sector in which they function. Some of these insurance policies enrich the cyber resilience of the IT infrastructure, for example, PCI DSS and GDPR. The Kubernetes cluster is section of the IT infrastructure, and companies need to be certain they comply with policies and security most effective techniques wherever relevant.
One particular of the requirements that look in most IT policy paperwork is the log retention coverage. Log retention procedures dictate how lengthy you must store logs. You can use these logs to establish threats in the course of active monitoring and incident investigation.
Directors interact with the Kubernetes cluster via the Kubernetes API, and the cluster can log all API requests and responses. You can detect unconventional or unwelcome API calls from the Kubernetes audit logs. In far more depth, you can get alerts for activities this kind of as authentication failure, container generation, modification, and deletion. The Kubernetes audit logging element is disabled by default. Hence, you want to consider some necessary actions to flip it on.
Working with Wazuh to observe and archive Kubernetes audit logs
You want to observe the audit logs to detect security threats and anomalies. Additionally, you require to index the logs to search for relevant information and facts throughout an incident investigation. Wazuh monitors, outlets, and indexes the Kubernetes audit logs. Wazuh is an open up source unified XDR and SIEM system. It is commercially absolutely free and has over 10 million yearly downloads.
The Wazuh enhancement staff has a thorough guide on auditing Kubernetes with Wazuh. The guide particulars actions on how to do the next:
- Configure the Wazuh server to obtain and course of action the Kubernetes audit logs.
- Allow audit logs on the Kubernetes cluster and ahead them to the Wazuh server.
You can create custom made procedures to set off alerts when Wazuh detects particular events in the Kubernetes audit log. For instance, you can develop procedures to trigger alerts when resources are designed or deleted on the Kubernetes cluster.
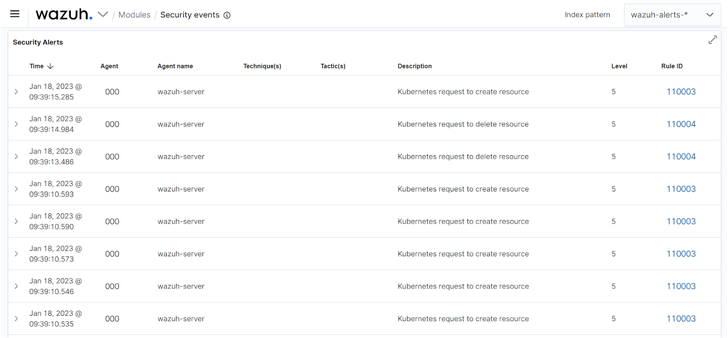 Figure 1: Alerts brought on from Kubernetes audit logs on the Wazuh dashboard
Figure 1: Alerts brought on from Kubernetes audit logs on the Wazuh dashboard
You can configure Wazuh to screen all archived logs on the dashboard. These are logs of Kubernetes functions that did not bring about an notify.
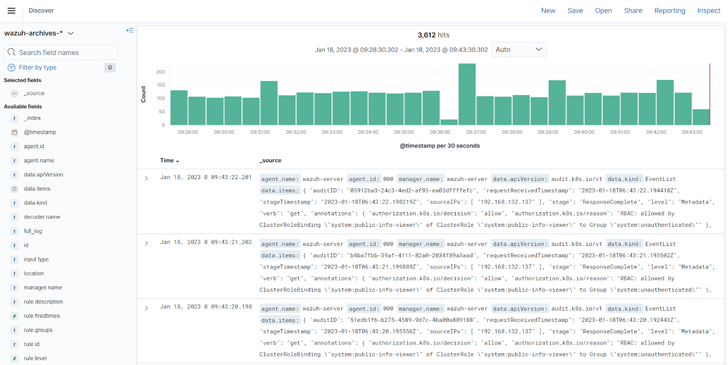 Determine 2: Kubernetes audit log archive on the Wazuh dashboard
Determine 2: Kubernetes audit log archive on the Wazuh dashboard
The Wazuh indexer is a highly scalable total-text lookup and analytics engine. The indexer indexes and shops the Kubernetes audit logs to supply you with actual-time facts research and analytics abilities. The Wazuh indexer improves performance during an incident investigation when you require to retrieve related info from the audit logs.
Summary
Kubernetes is broadly used to deploy, scale, and handle purposes. You should sustain Kubernetes audit logs for security and compliance needs. The audit logs have details that can indicate unconventional or unwelcome things to do. Wazuh is an open source XDR and SIEM alternative that screens, archives, and queries Kubernetes audit logs to detect security threats and other anomalies. Wazuh also protects other elements of an IT infrastructure, such as endpoints and cloud workloads.
Wazuh has a significant community of end users who assistance each and every other and help to strengthen the products. You can sign up for the Wazuh neighborhood to lead to the product or service and ask for help for any issues you may possibly have.
Discovered this posting intriguing? Observe us on Twitter and LinkedIn to browse far more unique articles we post.
Some parts of this article are sourced from:
thehackernews.com

 Hackers Abused Microsoft’s “Verified Publisher” OAuth Apps to Hack Corporate Email Accounts
Hackers Abused Microsoft’s “Verified Publisher” OAuth Apps to Hack Corporate Email Accounts