Interest, Android customers! A banking malware capable of stealing delicate facts is “spreading promptly” across Europe, with the U.S. likely to be the subsequent goal.
In accordance to a new investigation by Proofpoint, the threat actors behind FluBot (aka Cabassous) have branched out beyond Spain to concentrate on the U.K., Germany, Hungary, Italy, and Poland. The English-language campaign by itself has been noticed to make use of much more than 700 distinctive domains, infecting about 7,000 gadgets in the U.K.
In addition, German and English-language SMS messages were identified currently being sent to U.S. customers from Europe, which Proofpoint suspects could be the consequence of malware propagating by way of contact lists stored on compromised telephones. A concerted marketing campaign aimed at the U.S. is but to be detected.

FluBot, a nascent entry in the banking trojan landscape, began its operations late last calendar year, with strategies leveraging the malware infecting much more than 60,000 customers in Spain, according to an investigation posted by Proactive Defence Against Long term Threats (PRODAFT) in March 2021. It is said to have amassed extra than 11 million phone quantities from the units, representing 25% of the complete inhabitants in Spain.
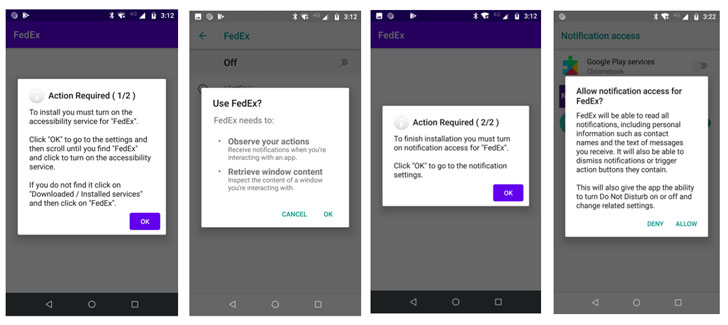
Largely distributed by way of SMS phishing (aka smishing), the messages masquerade as a delivery provider these as FedEx, DHL, and Correos, seemingly notifying customers of their offer or cargo supply position together with a backlink to observe the buy, which, when clicked, downloads malicious apps that have the encrypted FluBot module embedded within just them.
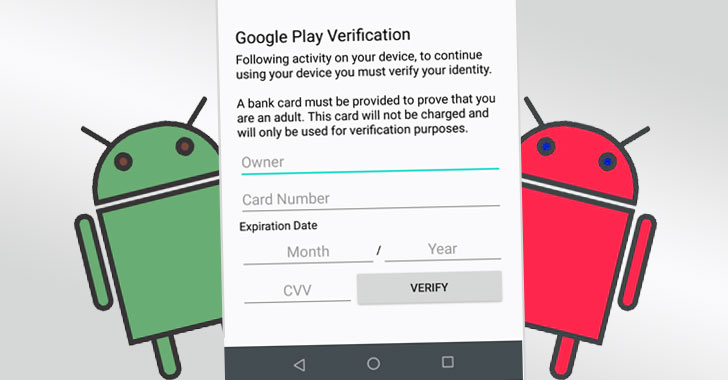
“FluBot is a new Android banking malware that uses overlay attacks to accomplish webview-centered application phishing,” the scientists famous. “The malware largely targets mobile banking and cryptocurrency purposes but also gathers a large vary of person data from all put in programs on a specified gadget.”
On installation, FluBot not only tracks the purposes launched on the system but also overlays login internet pages of financial applications with specifically-crafted destructive variants from an attacker-managed server, developed with the purpose of hijack qualifications, in addition to retrieving speak to lists, messages, calls, and notifications by abusing the Android Accessibility Provider.

Even though Spanish authorities arrested four criminals suspected to be at the rear of the FluBot campaign, bacterial infections have picked up, though at the same time increasing the international locations targeted to include Japan, Norway, Sweden, Finland, Denmark, and the Netherlands in a quick time period of time, for each the latest insights from ThreatFabric.
The spurt in FluBot exercise has prompted Germany’s Federal Business office for Information and facts Security (BSI) and the U.K.’s Nationwide Cyber Security Centre (NCSC) to issue alerts warning of ongoing assaults through fraudulent SMS messages that trick consumers into setting up “adware that steals passwords and other delicate information.”
“FluBot is very likely to continue to unfold at a relatively swift amount, moving methodically from place to nation by way of a aware effort by the threat actors,” Proofpoint scientists said. “As prolonged as there are end users prepared to have confidence in an unanticipated SMS information and follow the risk actors’ delivered guidelines and prompts, strategies these types of as these will be profitable.”
Observed this short article fascinating? Comply with THN on Facebook, Twitter and LinkedIn to examine much more exceptional content material we write-up.
Some parts of this article are sourced from:
thehackernews.com

 Nike's PlayStation 5-themed shoes arrive next month
Nike's PlayStation 5-themed shoes arrive next month