The 2022 SaaS Security Study Report, in collaboration with CSA, examines the condition of SaaS security as observed in the eyes of CISOs and security experts in today’s enterprises. The report gathers nameless responses from 340 CSA users to look at not only the growing hazards in SaaS security but also how unique corporations are at present performing to safe on their own.
Demographics
The vast majority (71%) of respondents had been located in the Americas, another 17% from Asia, and 13% from EMEA. Of these members 49% influence the selection-generating approach whilst 39% run the procedure itself. The study examined companies from a selection of industries, these types of as telecommunications (25%), finance (22%), and government (9%).
Though there are lots of takeaways from the survey, these are our best seven.
1: SaaS Misconfigurations are Leading to Security Incidents
Considering the fact that 2019, SaaS misconfigurations have turn into a best problem for companies, with at minimum 43% of corporations reporting they have dealt with a person or extra security incidents caused by a SaaS misconfiguration. Nonetheless, considering the fact that lots of other organizations condition they are unaware if they had experienced a security incident, the number of SaaS misconfigured-associated incidents could be as high as 63%. These quantities are hanging when in contrast to the 17% of security incidents brought about by IaaS misconfiguration.
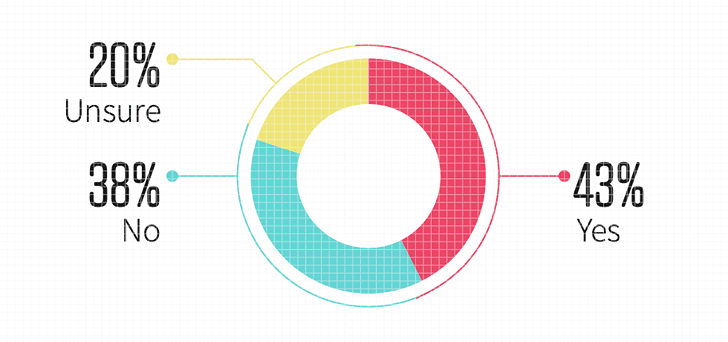 Figure 1. Organizations experienced a security incident owing to a SaaS misconfiguration
Figure 1. Organizations experienced a security incident owing to a SaaS misconfiguration
Discover how to avoid misconfigurations in your SaaS stack
2: Absence of Visibility and too Lots of Departments with Access Claimed as Foremost Result in for SaaS Misconfigurations
So what specifically is the bring about of these SaaS misconfigurations? While there are various elements to take into consideration, the survey respondents slim it down to the two top results in – having much too several departments with entry to SaaS security settings (35%), and a lack of visibility into the improvements in the SaaS security configurations (34%). These are two linked issues, neither of which are astonishing presented that deficiency of visibility was rated a leading issue when adopting SaaS programs, and that on regular organizations have many departments with access to security settings. 1 of the main factors for the lack of visibility is the actuality that as well lots of departments have obtain to security settings, and several of these departments you should not have appropriate teaching and target on security.
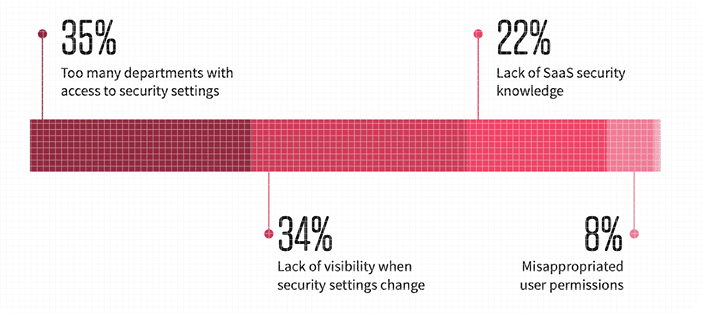 Figure 2. The principal results in of SaaS misconfigurations
Figure 2. The principal results in of SaaS misconfigurations
3: Investment in Organization-Critical SaaS Purposes are Outpacing SaaS Security Instruments and Staff members
It can be properly-recognized that organizations are adopting extra applications – this past calendar year by yourself, 81% of respondents say that they have enhanced their investments in enterprise-critical SaaS purposes. On the other hand, investment in security instruments (73%) and staff (55%) for SaaS security is lessen. This dissonance represents an rising burden on the present security groups to keep an eye on SaaS security.
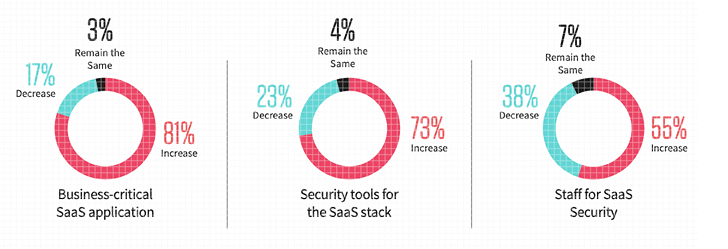 Determine 3. Companies’ investment decision in SaaS apps, security instruments, and personnel
Determine 3. Companies’ investment decision in SaaS apps, security instruments, and personnel
4: Handbook detection and remediation of SaaS misconfigurations keeps organizations exposed
46% of companies that manually monitor their SaaS security are conducting checks only once a thirty day period or significantly less, when 5% do not conduct checks at all. After exploring a misconfiguration, it will take further time for security groups to solve it. Close to 1 in 4 businesses acquire just one week or longer to resolve a misconfiguration when remediating manually. This prolonged timing leaves companies vulnerable.
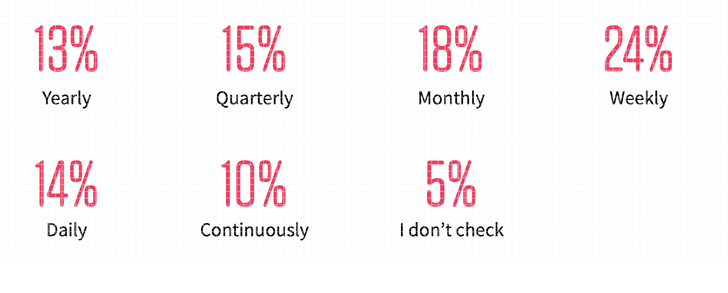 Figure 4. How usually businesses to manually check their SaaS misconfigurations
Figure 4. How usually businesses to manually check their SaaS misconfigurations
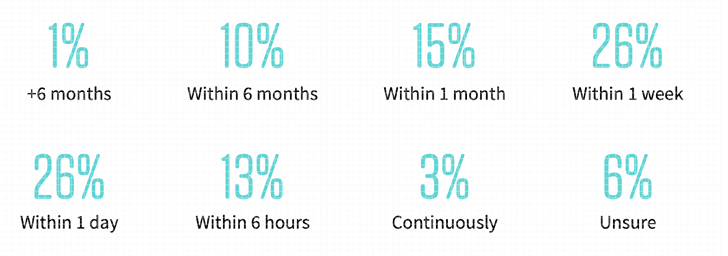 Determine 5. How very long it requires companies to manually deal with SaaS misconfiguration
Determine 5. How very long it requires companies to manually deal with SaaS misconfiguration
5: Use of an SSPM lessens timeline to detect and remediate SaaS misconfigurations
The flip facet of the coin for getting #4 is that the corporations that have applied an SSPM can far more swiftly and accurately detect and remediate their SaaS misconfigurations. The majority of these businesses (78%) employ an SSPM to check out their SaaS security configurations at the time a 7 days or far more. When it comes to resolving the misconfiguration, 81% of corporations applying an SSPM are equipped to resolve it in a day to a 7 days.
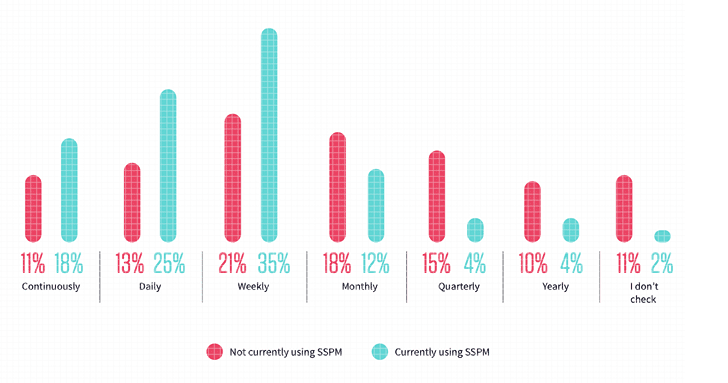 Determine 6. Frequency of SaaS security configuration checks
Determine 6. Frequency of SaaS security configuration checks
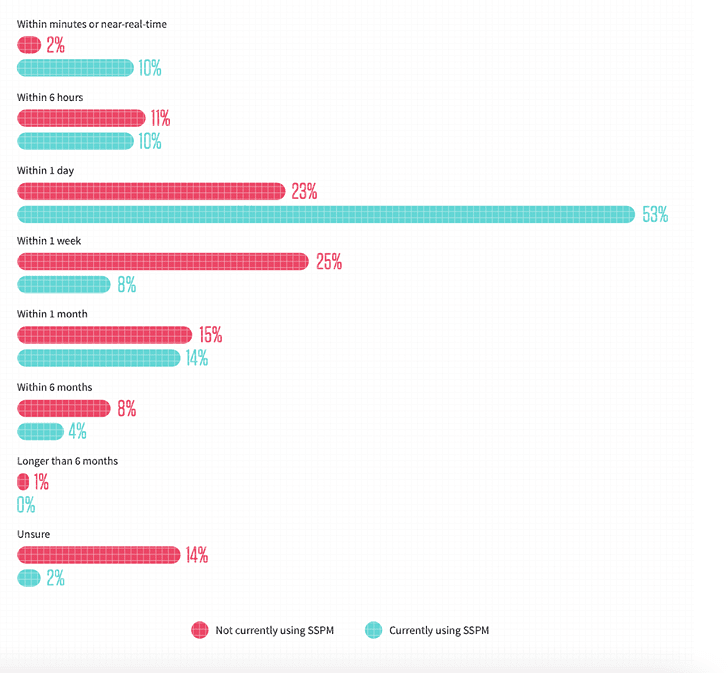 Figure 7. Size of time to resolve SaaS misconfigurations
Figure 7. Size of time to resolve SaaS misconfigurations
Simply click here to plan a 15-minute demo of how Adaptive Shield SSPM can aid you
6: 3rd celebration application access is a prime worry
Third-party apps, also termed no-code or low-code platforms, can raise productiveness, permit hybrid perform, and are overall crucial in constructing and scaling a firm’s do the job procedures. On the other hand, lots of buyers quickly hook up 3rd bash applications with out thinking about what permission these apps are requesting. At the time approved, the permissions and subsequent access granted to these 3rd occasion applications could be harmless or as malicious as an executable file. Without visibility into the SaaS-to-SaaS source chain, workforce are connecting to their organization’s company-critical apps, security teams are blind to quite a few opportunity threats. As companies carry on to undertake SaaS programs, a person of their leading considerations is the absence of visibility, primarily that of 3rd-occasion application obtain to the main SaaS stack (56%).
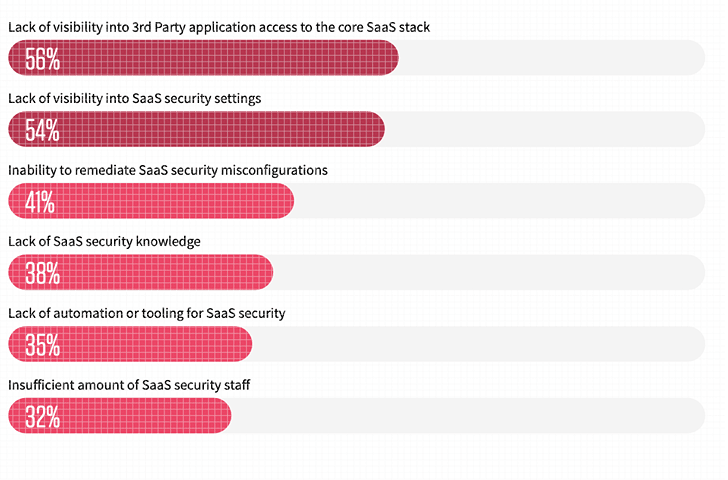 Figure 8. Companies’ leading concern when adopting SaaS applications
Figure 8. Companies’ leading concern when adopting SaaS applications
Preparing Forward and Applying SSPM
Despite the category being introduced to the current market two years ago, it is fast maturing. When assessing 4 cloud security alternatives, SSPM gets an average score of “relatively common.” Also, 62% of respondents report that they are currently using an SSPM or plan to employ one particular in the coming 24 months.
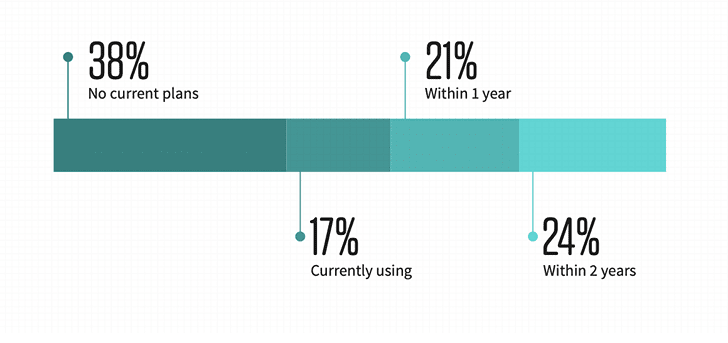 Figure 9. Organizations at present making use of or organizing to use SSPM
Figure 9. Organizations at present making use of or organizing to use SSPM
Conclusion
The 2022 SaaS Security Study Report delivers insights into how businesses are utilizing and defending their SaaS applications. It is with no a doubt that as corporations proceed to undertake a lot more enterprise-critical SaaS applications, there is more risk. To deal with this problem head-on firms must commence securing by themselves through two best tactics:
- The first being to permit security groups to obtain total visibility into all SaaS app security settings, like 3rd occasion app accessibility and user permissions, which in flip lets departments to preserve their accessibility without having risk of making improper modifications that depart the corporation vulnerable.
- Secondly, organizations should benefit from automated tools, such as SSPMs, to continuously keep track of and quickly remediate SaaS security misconfigurations. These automated resources allow for security groups to acknowledge and deal with issues in in close proximity to-true time, lessening the all round time the corporation is left susceptible or avoiding the challenge from developing all with each other.
Both of these changes present assistance to their security crew even though not preventing departments from continuing their perform.
Located this article exciting? Stick to THN on Facebook, Twitter and LinkedIn to read through far more special information we article.
Some parts of this article are sourced from:
thehackernews.com


 Critical Vulnerability in Premium WordPress Themes Allows for Site Takeover
Critical Vulnerability in Premium WordPress Themes Allows for Site Takeover