The suspected Pakistan-aligned threat actor identified as SideCopy has been observed leveraging themes linked to the Indian armed forces investigate organization as section of an ongoing phishing campaign.
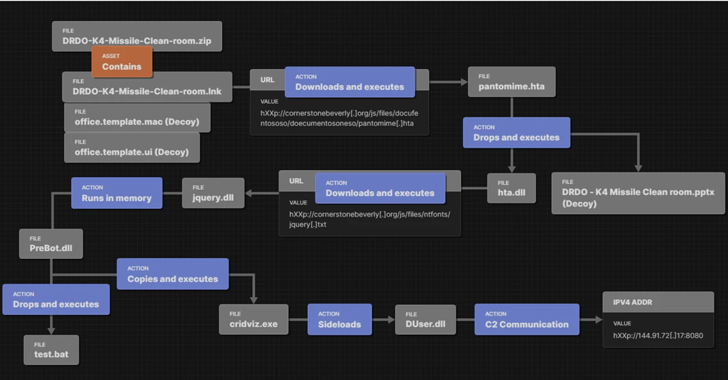
This entails applying a ZIP archive entice pertaining to India’s Defence Study and Growth Business (DRDO) to produce a malicious payload capable of harvesting sensitive data, Fortinet FortiGuard Labs stated in a new report.
The cyber espionage group, with exercise dating back to at the very least 2019, targets entities that align with Pakistan govt pursuits. It’s considered to share overlaps with yet another Pakistani hacking crew termed Clear Tribe.

SideCopy’s use of DRDO-relevant decoys for malware distribution was beforehand flagged by Cyble and Chinese cybersecurity agency QiAnXin in March 2023, and once more by Group Cymru past month.
Curiously, the same attack chains have been observed to load and execute Motion RAT as perfectly as an open up supply remote entry trojan known as AllaKore RAT.
The newest infection sequence documented by Fortinet is no unique, major to the deployment of an unspecified pressure of RAT which is capable of speaking with a remote server and launching added payloads.
The progress is an indicator that SideCopy has continued to carry out spear-phishing email attacks that use Indian govt and defense forces-linked social engineering lures to drop a broad vary of malware.
 Resource: Group Cymru
Resource: Group Cymru
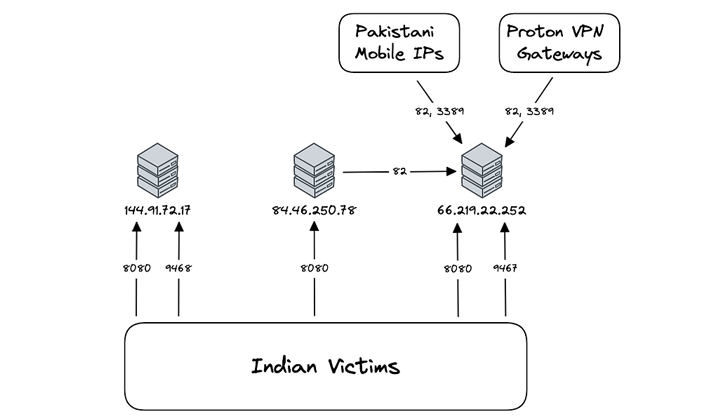
Additional examination of the Motion RAT command-and-manage (C2) infrastructure by Crew Cymru has recognized outbound connections from one of the C2 server IP addresses to one more tackle 66.219.22[.]252, which is geolocated in Pakistan.
The cybersecurity corporation also claimed it observed “communications sourced from 17 distinct IPs assigned to Pakistani cellular companies and 4 Proton VPN nodes,” noting inbound connections to the IP address from IP addresses assigned to Indian ISPs.
Forthcoming WEBINARLearn to Cease Ransomware with Authentic-Time Protection
Be part of our webinar and discover how to halt ransomware attacks in their tracks with genuine-time MFA and services account protection.
Save My Seat!
In all, as lots of as 18 distinctive victims in India have been detected as connecting to C2 servers related with Motion RAT and 236 exceptional victims, once more situated in India, connecting to C2 servers linked with AllaKore RAT.
The most recent conclusions lend credence to SideCopy’s Pakistan back links, not to mention underscore the point that the campaign has been successful in concentrating on Indian consumers.
“The Motion RAT infrastructure, related to SideCopy, is managed by end users accessing the Internet from Pakistan,” Team Cymru mentioned. “Target action predated the public reporting of this campaign, in some conditions by various months.”
Located this article attention-grabbing? Observe us on Twitter and LinkedIn to browse a lot more exceptional content we article.
Some parts of this article are sourced from:
thehackernews.com


 Amazon’s Echo Show 8 drops to $75 in new smart display sale
Amazon’s Echo Show 8 drops to $75 in new smart display sale