Three new security flaws have been disclosed in Microsoft Azure API Administration service that could be abused by destructive actors to get entry to delicate info or backend services.
This includes two server-aspect ask for forgery (SSRF) flaws and one instance of unrestricted file add performance in the API Management developer portal, according to Israeli cloud security company Ermetic.
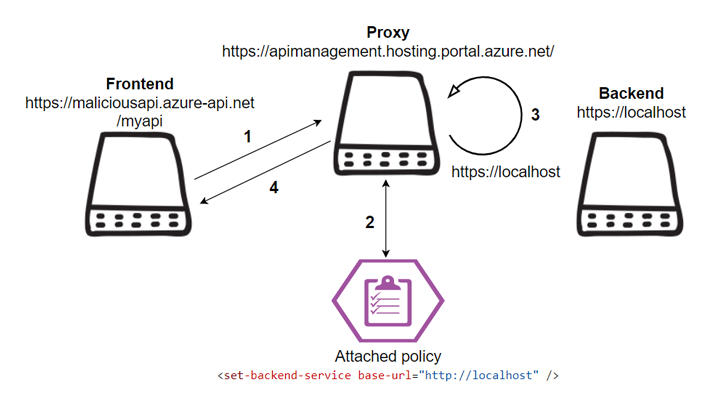
“By abusing the SSRF vulnerabilities, attackers could mail requests from the service’s CORS Proxy and the hosting proxy by itself, access interior Azure property, deny service and bypass web application firewalls,” security researcher Liv Matan claimed in a report shared with The Hacker News.
“With the file upload path traversal, attackers could add destructive files to Azure’s hosted internal workload.”
Azure API Management is a multicloud management platform that lets businesses to securely expose their APIs to external and interior clients and enable a vast vary of linked experiences.

Of the two SSRF flaws discovered by Ermetic, a person of them is a bypass for a deal with set in put by Microsoft to address a similar vulnerability reported by Orca earlier this yr. The other vulnerability resides in the API Administration proxy purpose.
Exploitation of SSRF flaws can final result in loss of confidentiality and integrity, allowing a menace actor to go through interior Azure sources and execute unauthorized code.
The route traversal flaw found in the developer portal, on the other hand, stems from a deficiency of validation of the file style and path of the documents uploaded.
An authenticated user can leverage this loophole to add malicious data files to the developer portal server and likely even execute arbitrary code on the underlying system.
Approaching WEBINARLearn to Prevent Ransomware with Authentic-Time Safety
Be a part of our webinar and find out how to quit ransomware attacks in their tracks with genuine-time MFA and support account safety.
Conserve My Seat!
Subsequent liable disclosure, all the a few flaws have been patched by Microsoft.
The findings appear months immediately after researchers from Orca specific a “by-style flaw” in Microsoft Azure could be exploited by attackers to get obtain to storage accounts, transfer laterally in the environment, and even execute remote code.
It also follows the discovery of a further Azure vulnerability dubbed EmojiDeploy that could enable an attacker to seize management of a focused application.
Uncovered this article fascinating? Stick to us on Twitter and LinkedIn to read much more unique material we put up.
Some parts of this article are sourced from:
thehackernews.com


 Researchers Uncover New Exploit for PaperCut Vulnerability That Can Bypass Detection
Researchers Uncover New Exploit for PaperCut Vulnerability That Can Bypass Detection