The Laptop Emergency Reaction Crew of Ukraine (CERT-UA) has warned of cyber assaults perpetrated by Russian nation-state hackers concentrating on several federal government bodies in the nation.
The agency attributed the phishing marketing campaign to APT28, which is also known by the names Fancy Bear, Forest Blizzard, FROZENLAKE, Iron Twilight, Sednit, and Sofacy.
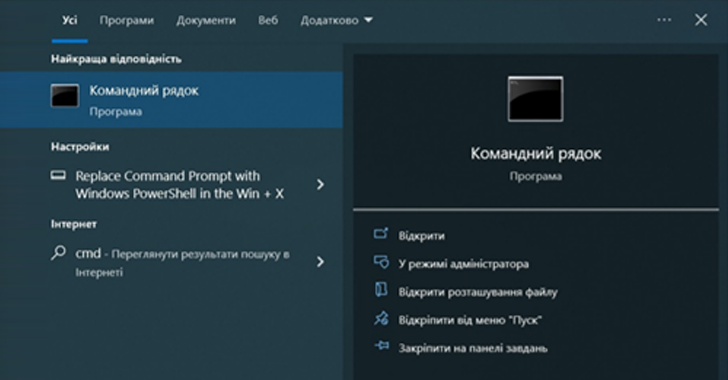
The email messages arrive with the subject line “Windows Update” and purportedly comprise guidance in the Ukrainian language to operate a PowerShell command under the pretext of security updates.
Operating the script loads and executes a upcoming-phase PowerShell script that is created to collect simple method details by way of commands like tasklist and systeminfo, and exfiltrate the details by means of an HTTP ask for to a Mocky API.

To trick the targets into working the command, the emails impersonated technique directors of the targeted federal government entities applying pretend Microsoft Outlook email accounts made with the employees’ true names and initials.
CERT-UA is recommending that corporations limit users’ means to operate PowerShell scripts and keep track of network connections to the Mocky API.
The disclosure will come months right after the APT28 was tied to assaults exploiting now-patched security flaws in networking equipment to perform reconnaissance and deploy malware versus choose targets.
Google’s Danger Analysis Team (TAG), in an advisory printed last thirty day period, thorough a credential harvesting operation carried out by the danger actor to redirect visitors of Ukrainian federal government web sites to phishing domains.
Russian-primarily based hacking crews have also been connected to the exploitation of a critical privilege escalation flaw in Microsoft Outlook (CVE-2023-23397, CVSS score: 9.8) in intrusions directed against the govt, transportation, electricity, and army sectors in Europe.
Approaching WEBINARLearn to Stop Ransomware with True-Time Security
Sign up for our webinar and find out how to end ransomware attacks in their tracks with authentic-time MFA and support account security.
Help save My Seat!
The enhancement also comes as Fortinet FortiGuard Labs uncovered a multi-stage phishing attack that leverages a macro-laced Term doc supposedly from Ukraine’s Energoatom as a entice to deliver the open resource Havoc publish-exploitation framework.
“It continues to be remarkably very likely that Russian intelligence, armed forces, and regulation enforcement expert services have a longstanding, tacit knowledge with cybercriminal danger actors,” cybersecurity business Recorded Long term stated in a report before this calendar year.
“In some instances, it is pretty much particular that these organizations keep an set up and systematic connection with cybercriminal threat actors, possibly by indirect collaboration or by means of recruitment.”
Identified this article fascinating? Abide by us on Twitter and LinkedIn to study additional unique content material we submit.
Some parts of this article are sourced from:
thehackernews.com

 Google Blocks 1.43 Million Malicious Apps, Bans 73,000 Bad Accounts in 2022
Google Blocks 1.43 Million Malicious Apps, Bans 73,000 Bad Accounts in 2022