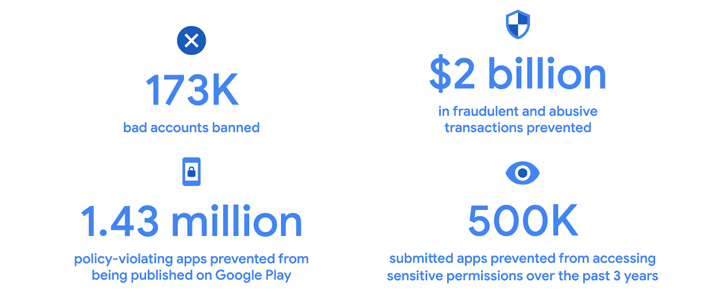
Google disclosed that its improved security features and app evaluation procedures served it block 1.43 million terrible apps from remaining released to the Participate in Store in 2022.
In addition, the firm claimed it banned 173,000 poor accounts and fended off in excess of $2 billion in fraudulent and abusive transactions by way of developer-struggling with functions like Voided Buys API, Obfuscated Account ID, and Play Integrity API.
The addition of identity verification solutions this kind of as phone quantity and email deal with to sign up for Google Perform contributed to a reduction in accounts applied to publish applications that go against its insurance policies, Google pointed out.
The research behemoth even more claimed it “prevented about 500K submitted apps from unnecessarily accessing sensitive permissions more than the past 3 years.”
“In 2022, the App Security Enhancements plan aided developers repair ~500K security weaknesses affecting ~300K apps with a combined put in foundation of approximately 250B installs,” it observed.
In distinction, Google blocked 1.2 million policy-violating applications from currently being published and banned 190,000 negative accounts in 2021.
The enhancement arrives weeks following Google enacted a new details deletion plan that involves application developers to offer a “quickly discoverable alternative” to users from the two in an app and outside the house of it.
Inspite of these attempts from Google, cybercriminals are continuing to obtain approaches all around the app storefront’s security protections and publish malicious and adware applications.
Case in position, McAfee’s Mobile Exploration Group found out 38 video games masquerading as Minecraft and which have been set up by no a lot less than 35 million users globally, mainly positioned in the U.S., Canada, South Korea, and Brazil.
These gaming applications, though providing the promised performance, have been observed to integrate the HiddenAds malware to stealthily load ads in the qualifications to produce illicit income for its operators.
Some of the most downloaded applications are as follows –
- Block Box Grasp Diamond (com.excellent.robo.video game.builder.craft.block)
- Craft Sword Mini Pleasurable (com.craft.earth.fairy.fun.everyday.block)
- Block Box Skyland Sword (com.skyland.pet.realm.block.rain.craft)
- Craft Monster Crazy Sword (com.skyland.enjoyable.block.match.monster.craft)
- Block Pro Forrest Diamond (com.monster.craft.block.enjoyable.robo.fairy)
“One of the most available written content for youthful people making use of cell products is video games,” McAfee said. “Malware authors are also aware of this and check out to disguise their malicious characteristics within games.”
Complicating the dilemma is the surge in Android banking malware that can be weaponized by menace actors to gain entry to sufferer units and harvest particular information and facts.
One more rising craze is the use of binding providers to trojanize genuine apps and conceal a rogue APK payload. This strategy has been adopted by terrible actors to distribute an Android botnet dubbed DAAM, Cyble said.
Forthcoming WEBINARLearn to Quit Ransomware with Genuine-Time Protection
Join our webinar and discover how to stop ransomware assaults in their tracks with genuine-time MFA and support account protection.
Save My Seat!
The malware, when put in, establishes connections with a distant server to carry out a wide vary of nefarious actions, such as performing as ransomware by encrypting documents stored in the equipment employing a password retrieved from the server.
DAAM also abuses Android’s accessibility companies to keep an eye on users’ exercise, therefore enabling it to log keystrokes, record VoIP phone calls from quick messaging apps, acquire browser historical past, connect with logs, photos, screenshots, and SMS messages, operate arbitrary code, and open up phishing URLs.
“Malware authors normally leverage authentic apps to distribute malicious code to steer clear of suspicion,” the cybersecurity organization stated in an assessment revealed very last month.
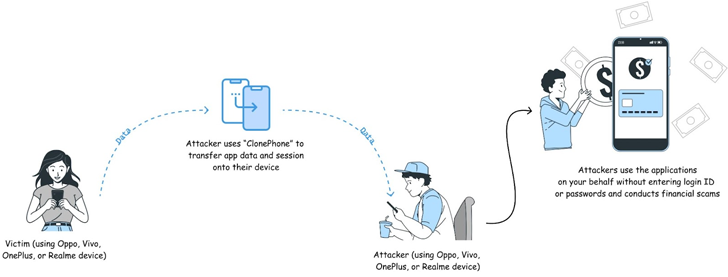
The findings also observe an advisory from CloudSEK, which identified that various well-known Android applications like Canva, LinkedIn, Strava, Telegram, and WhatsApp do not invalidate or revalidate session cookies following application information is transferred from a single system to one more.
Although this attack scenario requires an adversary to have bodily accessibility to a target’s phone, it could permit for account takeover and get unauthorized obtain to confidential facts.
To mitigate such threats, it’s recommended to enable two-variable authentication (2FA) to add an more layer of account safety, scrutinize application permissions, safe equipment with a password, and keep away from leaving them unattended in public areas.
Uncovered this short article fascinating? Observe us on Twitter and LinkedIn to study extra exclusive material we article.
Some parts of this article are sourced from:
thehackernews.com


 CISA Warns of Critical Flaws in Illumina’s DNA Sequencing Instruments
CISA Warns of Critical Flaws in Illumina’s DNA Sequencing Instruments