A considerable range of victims in the shopper and enterprise sectors positioned throughout Australia, Japan, the U.S., and India have been afflicted by an evasive facts-thieving malware identified as ViperSoftX.
ViperSoftX was to start with documented in 2020, with cybersecurity business Avast detailing a marketing campaign in November 2022 that leveraged the malware to distribute a destructive Google Chrome extension able of siphoning cryptocurrencies from wallet purposes.
Now a new evaluation from Development Micro has exposed the malware’s adoption of “a lot more innovative encryption and basic anti-investigation approaches, such as byte remapping and web browser communication blocking.”
The arrival vector of ViperSoftX is usually a software crack or a vital generator (keygen), while also utilizing precise non-destructive software program like multimedia editors and process cleaner apps as “carriers.”
One of the critical actions performed by the malware prior to downloading a to start with-phase PowerShell loader is a sequence of anti-digital device, anti-monitoring, and anti-malware checks.
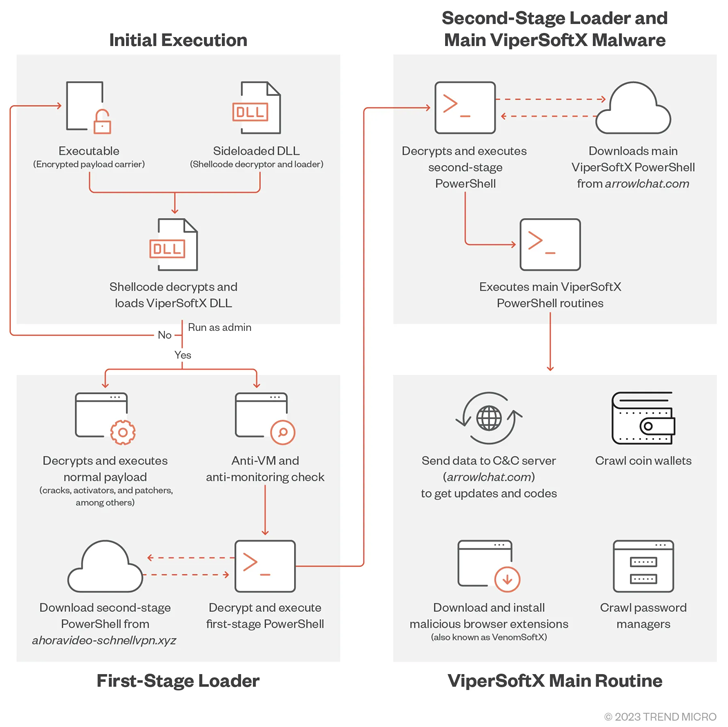
The loader then decrypts and executes a second-phase PowerShell script retrieved from a distant server, which then requires treatment of launching the principal plan accountable for setting up rogue browser extensions to exfiltrate passwords and crypto wallet info.
The major command-and-regulate (C&C) servers employed for the next stage download have been observed to adjust on a regular monthly foundation, suggesting tries on the aspect of the actor to sidestep detection.
Impending WEBINARLearn to Quit Ransomware with Genuine-Time Protection
Join our webinar and master how to end ransomware assaults in their tracks with authentic-time MFA and company account defense.
Help save My Seat!
“It also makes use of some fundamental anti-C&C analyses by disallowing communications utilizing web browsers,” Development Micro researcher Don Ovid Ladores said, incorporating the updated edition of ViperSoftX scans for the existence of KeePass 2 and 1Password password professionals.
As mitigations, it is suggested that end users obtain software only from official platforms and sources, and prevent downloading unlawful program.
“The cybercriminals behind ViperSoftX are also proficient ample to execute a seamless chain for malware execution although being less than the radar of authorities by choosing one particular of the most powerful approaches for providing malware to shoppers,” Ovid Ladores included.
Discovered this post appealing? Adhere to us on Twitter and LinkedIn to browse much more exceptional articles we article.
Some parts of this article are sourced from:
thehackernews.com

 Man Gets Four Years for Stealing Bitcoins Seized by Feds
Man Gets Four Years for Stealing Bitcoins Seized by Feds