An ongoing Magecart marketing campaign has captivated the interest of cybersecurity scientists for leveraging practical-on the lookout fake payment screens to capture delicate knowledge entered by unsuspecting customers.
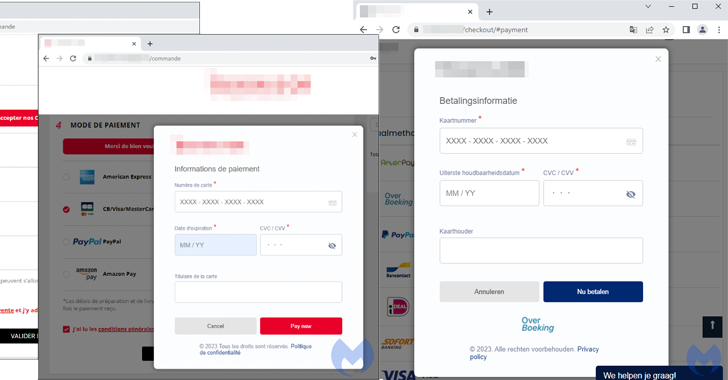
“The danger actor made use of original logos from the compromised keep and custom-made a web component identified as a modal to properly hijack the checkout web page,” Jérôme Segura, director of menace intelligence at Malwarebytes, said. “The outstanding issue right here is that the skimmer appears to be like far more authentic than the authentic payment page.”
The term Magecart is a capture-all that refers to a number of cybercrime teams which use on the net skimming tactics to steal personalized details from sites – most generally, purchaser aspects and payment information and facts on e-commerce internet sites.
The title originates from the groups’ preliminary focusing on of the Magento platform. According to details shared by Sansec, the initially Magecart-like assaults were being noticed as early as 2010. As of 2022, extra than 70,000 stores are believed to have been compromised with a web skimmer.
These digital skimming assaults, also identified as formjacking, usually leverage different forms of JavaScript trickery to siphon sensitive data from web-site end users.
The hottest iteration, as observed by Malwarebytes on an unnamed Parisian vacation accent keep operating on the PrestaShop CMS, involved the injection of a skimmer referred to as Kritec to intercept the checkout course of action and show a phony payment dialog to victims.
Kritec, previously detailed by Akamai and Malwarebytes in February 2023, has been observed to impersonate reputable third-party vendors like Google Tag Manager as an evasion method.
The cybersecurity company stated the skimmer is each sophisticated and intensely obfuscated, with the malicious modal loaded upon deciding upon a credit card as the payment possibility from the compromised site.
Once the payment card facts are harvested, a phony mistake concept about payment cancellation is briefly shown to the target before redirecting to the precise payment site, at which place the payment will go via.
“The skimmer will fall a cookie which will provide as an indication that the present-day session is now marked as concluded,” Segura stated. “If the user was to go back and try the payment once again, the malicious modal would no longer be exhibited.”
Upcoming WEBINARLearn to Cease Ransomware with Serious-Time Protection
Sign up for our webinar and study how to cease ransomware attacks in their tracks with serious-time MFA and provider account safety.
Help save My Seat!
The danger actors guiding the procedure are explained to be using distinct domains to host the skimmer, which are provided related names: “[name of store]-loader.js,” suggesting that the attacks are targeting different online retailers with tailor made modals.
“Discerning no matter if an on the net shop is dependable has become quite complicated and this case is a great example of a skimmer that would not raise any suspicion,” Segura claimed.
The results appear a minimal more than two months right after Malwarebytes unearthed another web skimmer that collects browser fingerprint data, these as IP addresses and Consumer-Agent strings, along with credit history card details, likely in an endeavor to keep track of invalid consumers these kinds of as bots and security researchers.
Uncovered this post attention-grabbing? Follow us on Twitter and LinkedIn to examine much more distinctive content we put up.
Some parts of this article are sourced from:
thehackernews.com

 Tonto Team Uses Anti-Malware File to Launch Attacks on South Korean Institutions
Tonto Team Uses Anti-Malware File to Launch Attacks on South Korean Institutions