South Korean instruction, construction, diplomatic, and political institutions are at the getting stop of new assaults perpetrated by a China-aligned danger actor regarded as the Tonto Staff.
“New situations have exposed that the team is working with a file relevant to anti-malware items to ultimately execute their malicious attacks,” the AhnLab Security Unexpected emergency Reaction Centre (ASEC) stated in a report posted this week.
Tonto Workforce, energetic due to the fact at the very least 2009, has a monitor file of focusing on several sectors across Asia and Japanese Europe. Earlier this year, the group was attributed to an unsuccessful phishing attack on cybersecurity business Group-IB.
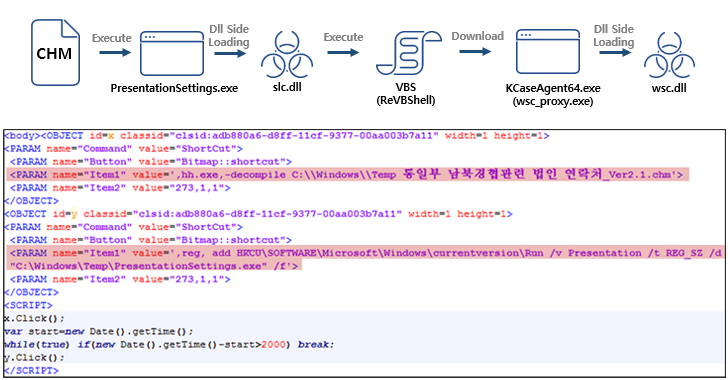
The attack sequence discovered by ASEC starts with a Microsoft Compiled HTML Aid (.CHM) file that executes a binary file to side-load a malicious DLL file (slc.dll) and launch ReVBShell, an open up resource VBScript backdoor also place to use by a further Chinese risk actor identified as Tick.
ReVBShell is subsequently leveraged to down load a next executable, a genuine Avast software package configuration file (wsc_proxy.exe), to facet-load a second rogue DLL (wsc.dll), eventually top to the deployment of the Bisonal distant entry trojan.
“The Tonto Staff is continuously evolving by many usually means these types of as using usual computer software for a lot more elaborate attacks,” ASEC claimed.
Impending WEBINARLearn to Halt Ransomware with Authentic-Time Security
Be a part of our webinar and study how to prevent ransomware assaults in their tracks with genuine-time MFA and company account protection.
Preserve My Seat!
The use of CHM data files as a distribution vector for malware is not minimal to Chinese risk actors by yourself. Very similar attack chains have been adopted by a North Korean country-state team acknowledged as ScarCruft in assaults aimed at its southern counterpart to backdoor targeted hosts.
The adversary, also recognized as APT37, Reaper, and Ricochet Chollima, has because also used LNK files to distribute the RokRAT malware, which is capable of collecting user credentials and downloading added payloads.
Identified this posting intriguing? Adhere to us on Twitter and LinkedIn to go through much more exclusive information we article.
Some parts of this article are sourced from:
thehackernews.com

 #RSAC: Securing Software Supply Chains Requires Outside-the-Box Thinking
#RSAC: Securing Software Supply Chains Requires Outside-the-Box Thinking