The maintainers of the Apache Superset open resource data visualization software have produced fixes to plug an insecure default configuration that could lead to distant code execution.
The vulnerability, tracked as CVE-2023-27524 (CVSS score: 8.9), impacts variations up to and which includes 2..1 and relates to the use of a default Solution_Critical that could be abused by attackers to authenticate and access unauthorized assets on internet-uncovered installations.
Naveen Sunkavally, the chief architect at Horizon3.ai, explained the issue as “a unsafe default configuration in Apache Superset that lets an unauth attacker to acquire distant code execution, harvest qualifications, and compromise knowledge.”
It is really really worth noting that the flaw does not influence Superset circumstances that have improved the default price for the Key_Key config to a additional cryptographically safe random string.
The cybersecurity company, which uncovered that the Magic formula_Crucial is defaulted to the benefit “x02x01thisismyscretkeyx01x02\e\y\y\h” at install time, mentioned that 918 out of 1,288 publicly-accessible servers were employing the default configuration in October 2021.
An attacker who experienced understanding of the magic formula critical could then indication in to these servers as an administrator by forging a session cookie and seize manage of the devices.
On January 11, 2022, the job maintainers attempted to rectify the difficulty by rotating the Solution_Essential value to “Alter_ME_TO_A_Sophisticated_RANDOM_Key” in the Python code alongside with user instructions to override it.
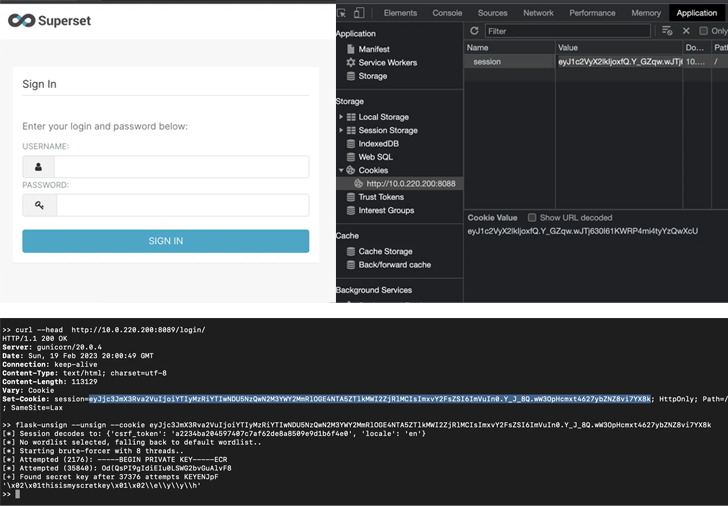
Horizon3.ai claimed it more observed two more Solution_Vital configurations that have been assigned the default values “USE_YOUR_Possess_Secure_RANDOM_Essential” and “thisISaSECRET_1234.”
An expanded lookup conducted in February 2023 with these 4 keys unearthed 3,176 cases, out of which 2,124 were being employing just one of the default keys. Some of those affected consist of big businesses, little providers, government businesses, and universities.
Pursuing liable disclosure to the Apache security team a 2nd time, a new update (model 2.1) was launched on April 5, 2023, to plug the security gap by stopping the server from commencing up completely if it truly is configured with the default Mystery_Critical.
Impending WEBINARZero Believe in + Deception: Find out How to Outsmart Attackers!
Learn how Deception can detect superior threats, cease lateral motion, and enhance your Zero Have faith in technique. Join our insightful webinar!
Help you save My Seat!
“This correct is not foolproof while as it can be nevertheless feasible to operate Superset with a default Secret_Vital if it is installed by way of a docker-compose file or a helm template,” Sunkavally stated.
“The docker-compose file is made up of a new default Mystery_Important of Test_NON_DEV_Mystery that we suspect some buyers will unwittingly operate Superset with. Some configurations also established admin/admin as the default credential for the admin person.”
Horizon3.ai has also manufactured readily available a Python script that can be made use of to identify if Superset instances are vulnerable to the flaw.
“It’s typically recognized that buyers never read documentation and purposes ought to be intended to power users together a route the place they have no selection but to be protected by default,” Sunkavally concluded. “The greatest technique is to choose the decision away from people and demand them to get deliberate steps to be purposefully insecure.”
Found this write-up appealing? Observe us on Twitter and LinkedIn to read a lot more special information we article.
Some parts of this article are sourced from:
thehackernews.com


 Quad Countries Prepare For Info Sharing on Critical Infrastructure
Quad Countries Prepare For Info Sharing on Critical Infrastructure