Why is Visibility into OT Environments Critical?
The significance of Operational Technology (OT) for organizations is undeniable as the OT sector prospers together with the presently thriving IT sector. OT features industrial control units, production tools, and units that oversee and manage industrial environments and critical infrastructures. In latest several years, adversaries have acknowledged the absence of detection and security in a lot of industrial devices and are actively exploiting these vulnerabilities. In reaction, IT security leaders have turn out to be much more conscious of the require to protect their OT environments with security monitoring and reaction abilities. This growth was accelerated by extreme earlier cyber incidents concentrating on critical OT environments and even resulting in actual physical injury to infrastructures. Presented the pivotal purpose these methods engage in in small business operations and modern-day society, making sure their security is of utmost significance.
The underlying craze is apparent: OT and IoT networks are progressively integrated with standard IT networks for administration and entry functions, leading to improved conversation among these gadgets both equally internally and externally. This not only affects the networks alone but also carries considerable ramifications for the security groups accountable for safeguarding the surroundings. Although this convergence of OT and IT presents several positive aspects, this sort of as improved performance and lessened operational fees, it also presents increase to new security hazards and challenges, rendering OT environments extra vulnerable to cyber threats. As evidenced by previous assaults, these threats frequently go undetected due to inadequate security monitoring, allowing for danger actors to remain undetected for prolonged durations. As a final result, reaching holistic visibility and helpful anomaly detection in OT environments is pivotal for retaining steadfast security and regulate.
What Troubles Arise in Checking OT Environments?
To start with and foremost, comprehension the special threat landscape of OT environments is very important. Regular IT security detection techniques drop limited in this context, as they demand various sensitivity thresholds and much more refined monitoring for network segments or product teams, as very well as OT-distinct detection mechanisms. As opposed to IT attacks that concentrate on information theft, OT assaults usually purpose for actual physical impact. In addition, as latest illustrations show, ransomware in the context of OT is on the rise and instantly affects the availability of control devices and safety.
Second, monitoring OT environments involves the thought of many features, such as supplier entry management, unit management, and network communications. Managing and overseeing provider accessibility to OT and IoT networks is complicated, as connections in between exterior and internal networks can come about by way of several signifies like VPNs, immediate cell connections, and leap hosts. One more hurdle is system management, which encompasses update mechanisms and protection against unauthorized entry or manipulation. Implementing typical updating routines and deploying Endpoint Detection & Reaction (EDR) on OT and IoT units is frequently restricted or infeasible. The assortment of products, their lifestyle spans, and machine-precise functioning techniques make deploying security computer software to keep track of OT equipment hard and cumbersome.
Third, common IT network detection methods demand in-depth protocol information, which, in the OT context, consists of a huge assortment of various protocols and attack eventualities absent in common rule sets. OT network products join IoT sensors and devices employing communication protocols unheard of in common IT networks. In terms of extra intrusive security options, lively vulnerability scanning methods can also be problematic in OT environments, as they may cause disruptions or even outages. The same applies to Intrusion Prevention Methods (IPS) due to the fact they could block network packets, impacting security and business continuity in OT environments. As a final result, passive network detection devices like Network Detection & Response (NDR) options are improved suited for this purpose.
How Can I Effectively Monitor and Protected My OT Setting?
When safe obtain administration and unit lifecycle administration are critical, their seamless implementation can be extremely hard. In this context, Network Detection and Response (NDR) methods supply a non-intrusive and efficient method to checking OT environments. By concentrating on communication designs for OT devices, the intersection involving IT and OT, and third-party entry to OT networks, NDR devices supply thorough visibility and detection abilities without disrupting industrial operations and company procedures.
In individual, NDR answers with advanced baselining capabilities excel at identifying new and abnormal conversation designs that could show malicious routines inside of OT networks. Utilizing circulation information for baselining, these NDR devices provide protocol and device-independent anomaly detection by learning who communicates with whom and at what frequency. Rather of manually configuring these parameters, the NDR learns the baseline and alerts the security groups on unconventional requests or alterations in the frequency. In addition, a flexible use scenario framework makes it possible for placing great-tuned thresholds for OT-specific monitoring, together with the potential to set load monitoring with network zone-unique granularity. What’s more, the use of Machine Learning algorithms allows for more correct detection of anomalies and opportunity threats in contrast to standard rule-dependent methods.
As a outcome, the passive monitoring capabilities of NDR answers are very important for OT and IoT environments, where alternate checking solutions may be tricky to apply or trigger disruptions. ExeonTrace, a specially robust and effortless-to-implement ML-driven NDR process for OT environments, analyzes log facts from regular IT environments, OT networks, and soar host gateways, to give a comprehensive and holistic see of network action. Therein, the versatility of integrating many 3rd-bash log sources, this kind of as OT-unique logs, is very important. Also, ExeonTrace’s ability to combine with other OT-specific detection platforms enhances its capabilities and makes sure considerable security protection.
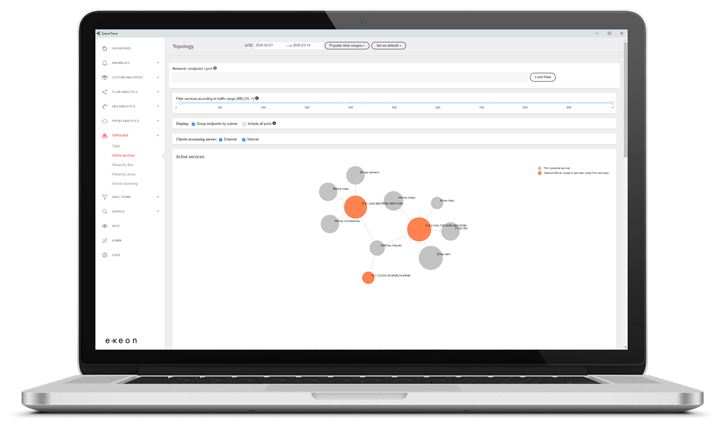 ExeonTrace System: OT Network Visibility
ExeonTrace System: OT Network Visibility
In summary, NDR options like ExeonTrace properly deal with the distinct difficulties of OT monitoring, creating the Swiss NDR system as the favored detection tactic for safeguarding OT environments. By utilizing ML-pushed NDR systems like ExeonTrace, businesses can reliably watch and safe their industrial functions, making sure small business continuity by way of an automated, economical, and hardware-free solution. Obtain out if ExeonTrace is the suitable answer for your organization and ask for a demo right now.
Observed this write-up intriguing? Observe us on Twitter and LinkedIn to read through extra unique content material we put up.
Some parts of this article are sourced from:
thehackernews.com


 Critical Infrastructure Firms Concerned Over Insider Threat
Critical Infrastructure Firms Concerned Over Insider Threat