The cyber espionage actor tracked as Blind Eagle has been joined to a new multi-stage attack chain that qualified prospects to the deployment of the NjRAT remote obtain trojan on compromised units.
“The group is recognized for employing a wide range of innovative attack approaches, such as customized malware, social engineering techniques, and spear-phishing attacks,” ThreatMon mentioned in a Tuesday report.
Blind Eagle, also referred to as APT-C-36, is a suspected Spanish-talking team that chiefly strikes private and general public sector entities in Colombian. Attacks orchestrated by the group have also qualified Ecuador, Chile, and Spain.
An infection chains documented by Examine Place and BlackBerry this yr have unveiled the use of spear-phishing lures to deliver commodity malware households like BitRAT, AsyncRAT, and in-memory Python loaders able of launching a Meterpreter payload.
The hottest discovery from ThreatMon entails the use of a JavaScript downloader to execute a PowerShell script hosted in Discord CDN. The script, in switch, drops an additional PowerShell script and a Windows batch file, and saves a VBScript file in the Windows startup folder to realize persistence.
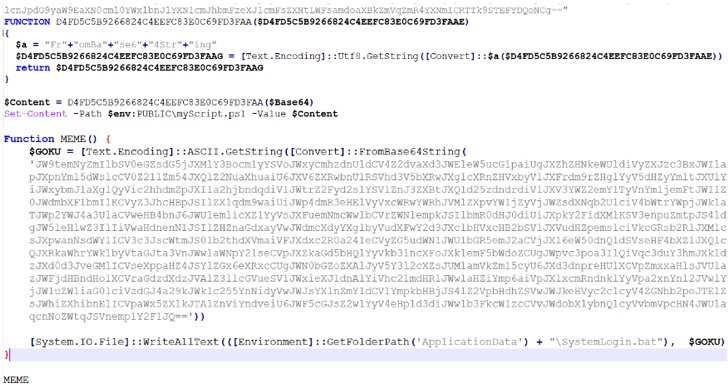
The VBScript code is then operate to start the batch file, which is subsequently deobfuscated to run the PowerShell script that was formerly delivered alongside with it. In the closing stage, the PowerShell script is used to execute njRAT.
“njRAT, also recognised as Bladabindi is a distant accessibility device (RAT) with person interface or trojan which enables the holder of the method to management the conclude-user’s laptop or computer,” the cybersecurity organization mentioned.
Observed this post intriguing? Comply with us on Twitter and LinkedIn to read much more exclusive content material we put up.
Some parts of this article are sourced from:
thehackernews.com

 Google Chrome Hit by Second Zero-Day Attack – Urgent Patch Update Released
Google Chrome Hit by Second Zero-Day Attack – Urgent Patch Update Released