An Iranian governing administration-backed actor recognized as Mint Sandstorm has been joined to assaults aimed at critical infrastructure in the U.S. amongst late 2021 to mid-2022.
“This Mint Sandstorm subgroup is technically and operationally mature, capable of building bespoke tooling and speedily weaponizing N-working day vulnerabilities, and has demonstrated agility in its operational emphasis, which appears to align with Iran’s nationwide priorities,” the Microsoft Risk Intelligence workforce claimed in an evaluation.
Targeted entities consist of seaports, strength providers, transit programs, and a main U.S. utility and gasoline firm. The activity is suspected to be retaliatory and in response to assaults focusing on its maritime, railway, and gas station payment units that took area in between May 2020 and late 2021.
It is really value noting in this article that Iran subsequently accused Israel and the U.S. of masterminding the attacks on the fuel stations in a bid to produce unrest in the country.
Mint Sandstorm is the new name assigned to the threat actor Microsoft was previously monitoring under the identify Phosphorus, and also recognized as APT35, Charming Kitten, ITG18, TA453, and Yellow Garuda.
The adjust in nomenclature is element of Microsoft’s change from chemical features-influenced monikers to a new weather conditions-themed danger actor naming taxonomy, in section pushed by the rising “complexity, scale, and quantity of threats.”
In contrast to MuddyWater (aka Mercury or Mango Sandstorm), which is acknowledged to run on behalf of Iran’s Ministry of Intelligence and Security (MOIS), Mint Sandstorm is reported to be associated with Islamic Revolutionary Guard Corps (IRGC).
The attacks specific by Redmond demonstrate the adversary’s means to consistently refine its methods as section of really-specific phishing strategies to receive access to specific environments.
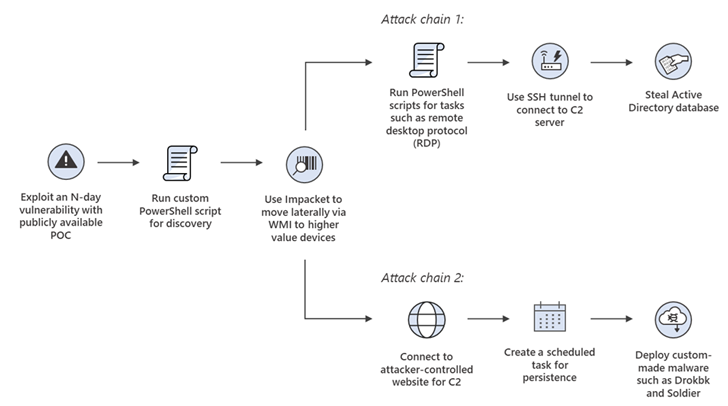
This features immediate adoption of publicly disclosed evidence-of-principles (PoCs) joined to flaws in internet-struggling with apps (e.g., CVE-2022-47966 and CVE-2022-47986) into their playbooks for initial accessibility and persistence.
A effective breach is adopted by the deployment of a personalized PowerShell script, which is then used to activate a single of the two attack chains, the initially of which relies on added PowerShell scripts to link to a remote server and steal Energetic Listing databases.
Approaching WEBINARMaster the Art of Dark Web Intelligence Collecting
Find out the artwork of extracting threat intelligence from the dark web – Be part of this pro-led webinar!
Help you save My Seat!
The other sequence involves the use of Impacket to connect to an actor-managed server and deploy a bespoke implant identified as Drokbk and Soldier, with the latter remaining a multistage .NET backdoor with the capability to download and operate instruments and uninstall alone.
Drokbk was formerly in-depth by Secureworks Counter Menace Unit (CTU) in December 2022, attributing it to a danger actor known as Nemesis Kitten (aka Cobalt Mirage, TunnelVision, or UNC2448), a sub-cluster of Mint Sandstorm.
Microsoft also referred to as out the threat actor for conducting very low-volume phishing strategies that culminate in the use of a third tailor made and modular backdoor referred to as CharmPower, a PowerShell-primarily based malware that can read through information, acquire host facts, and exfiltrate the info.
“Capabilities noticed in intrusions attributed to this Mint Sandstorm subgroup are concerning as they allow operators to conceal C2 conversation, persist in a compromised process, and deploy a array of publish-compromise applications with varying capabilities,” the tech large additional.
Located this article attention-grabbing? Adhere to us on Twitter and LinkedIn to read through far more special articles we post.
Some parts of this article are sourced from:
thehackernews.com


 Critical Flaws in vm2 JavaScript Library Can Lead to Remote Code Execution
Critical Flaws in vm2 JavaScript Library Can Lead to Remote Code Execution