Cybersecurity scientists have specific the interior workings of a remarkably evasive loader named “in2al5d p3in4er” (go through: invalid printer) that’s utilized to produce the Aurora data stealer malware.
“The in2al5d p3in4er loader is compiled with Embarcadero RAD Studio and targets endpoint workstations utilizing superior anti-VM (virtual device) strategy,” cybersecurity business Morphisec mentioned in a report shared with The Hacker Information.
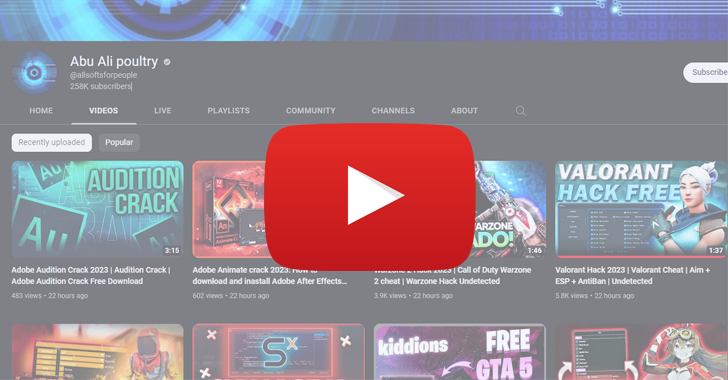
Aurora is a Go-primarily based facts stealer that emerged on the risk landscape in late 2022. Supplied as a commodity malware to other actors, it is really dispersed through YouTube movies and Search engine optimization-poised faux cracked application obtain web-sites.
Clicking the back links present in YouTube video descriptions redirects the target to decoy internet sites wherever they are enticed into downloading the malware underneath the garb of a seemingly-authentic utility.
The loader analyzed by Morphisec is made to question the vendor ID of the graphics card put in on a process, and compared it versus a established of allowlisted seller IDs (AMD, Intel, or NVIDIA). If the benefit will not match, the loader terminates by itself.
The loader in the long run decrypts the remaining payload and injects it into a legitimate approach called “sihost.exe” applying a technique known as process hollowing. Alternatively, some loader samples also allocate memory to compose the decrypted payload and invoke it from there.
“For the duration of the injection course of action, all loader samples take care of the necessary Get APIs dynamically and decrypt these names employing a XOR essential: ‘in2al5d p3in4er,'” security scientists Arnold Osipov and Michael Dereviashkin said.

One more vital facet of the loader is its use of Embarcadero RAD Studio to deliver executables for multiple platforms, thereby enabling it to evade detection.
“These with the lowest detection rate on VirusTotal are compiled applying ‘BCC64.exe,’ a new Clang based mostly C++ compiler from Embarcadero,” the Israeli cybersecurity business explained, pointing out its potential to evade sandboxes and digital machines.
“This compiler makes use of a distinct code foundation this kind of as ‘Standard Library’ (Dinkumware) and ‘Runtime Library’ (compiler-rt) and generates optimized code which changes the entry place and execution movement. This breaks security vendors’ indicators, these as signatures composed from ‘malicious/suspicious code block.'”
Future WEBINARMaster the Art of Dark Web Intelligence Collecting
Study the art of extracting danger intelligence from the dark web – Join this professional-led webinar!
Save My Seat!
In a nutshell, the findings demonstrate that the risk actors powering in2al5d p3in4er are leveraging social engineering solutions for a high-effect campaign that employs YouTube as a malware distribution channel and directs viewers to convincing-searching pretend internet websites to distribute the stealer malware.
The growth will come as Intel 471 unearthed one more malware loader AresLoader which is marketed for $300/month as a service for legal actors to force information stealers disguised as popular computer software working with a binder resource. The loader is suspected to be created by a group with ties to Russian hacktivism.
Some of the notable malware households distribute using AresLoader given that January 2023 involve Aurora Stealer, Laplas Clipper, Lumma Stealer, Stealc, and SystemBC.
Observed this short article appealing? Adhere to us on Twitter and LinkedIn to study far more exceptional written content we submit.
Some parts of this article are sourced from:
thehackernews.com

 Cyber Intrusion Detection Time at an All-Time Low
Cyber Intrusion Detection Time at an All-Time Low