A Chinese country-state team specific an unnamed Taiwanese media corporation to deliver an open up source crimson teaming device known as Google Command and Management (GC2) amid broader abuse of Google’s infrastructure for destructive finishes.
The tech giant’s Danger Examination Team (TAG) attributed the campaign to a danger actor it tracks underneath the geological and geographical-themed moniker HOODOO, which is also identified by the names APT41, Barium, Bronze Atlas, Wicked Panda, and Winnti.
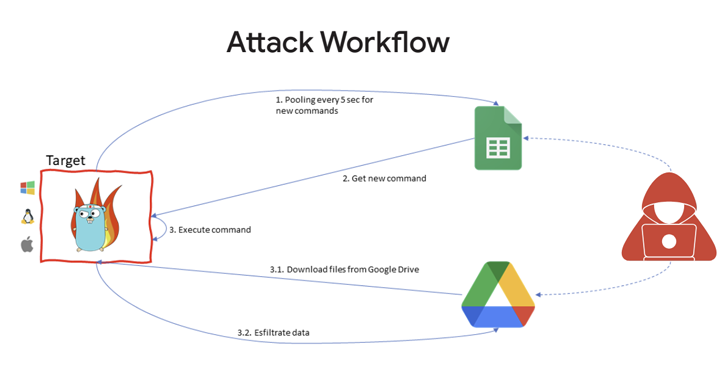
The commencing place of the attack is a phishing email that is made up of inbound links to a password-safeguarded file hosted on Google Generate, which, in change, incorporates the GC2 resource to browse instructions from Google Sheets and exfiltrate info employing the cloud storage support.
“Just after installation on the victim device, the malware queries Google Sheets to attain attacker instructions,” Google’s cloud division stated in its sixth Menace Horizons Report. “In addition to exfiltration by means of Generate, GC2 permits the attacker to obtain further information from Push onto the target method.”
Google mentioned the menace actor beforehand utilized the very same malware in July 2022 to goal an Italian task lookup site.
The progress is noteworthy for two causes: To start with, it suggests that Chinese risk teams are increasingly relying on publicly obtainable tooling like Cobalt Strike and GC2 to confuse attribution endeavours.
Secondly, it also factors to the increasing adoption of malware and equipment composed in the Go programming language, owing to its cross-system compatibility and its modular character.
Google even more cautioned that the “undeniable value of cloud companies” have created them a lucrative focus on for cybercriminals and governing administration-backed actors alike, “possibly as hosts for malware or giving the infrastructure for command-and-command (C2).”
Forthcoming WEBINARMaster the Art of Dark Web Intelligence Accumulating
Learn the artwork of extracting menace intelligence from the dark web – Be part of this professional-led webinar!
Save My Seat!
A situation in stage is the use of Google Drive for storing malware these as Ursnif (aka Gozi) and DICELOADER (aka Lizar or Tirion) in the variety of ZIP archive information as aspect of disparate phishing strategies.
“The most prevalent vector made use of to compromise any network, together with cloud scenarios is to consider more than an account’s credentials straight: possibly due to the fact there is no password, as with some default configurations, or because a credential has been leaked or recycled or is commonly so weak as to be guessable,” Google Cloud’s Christopher Porter explained.
The results come three months after Google Cloud in depth APT10’s (aka Bronze Riverside, Cicada, Potassium, or Stone Panda) targeting of cloud infrastructure and VPN technologies to breach enterprise environments and exfiltrate facts of fascination.
Uncovered this short article intriguing? Comply with us on Twitter and LinkedIn to read through far more distinctive material we write-up.
Some parts of this article are sourced from:
thehackernews.com

 Tour of the Underground: Master the Art of Dark Web Intelligence Gathering
Tour of the Underground: Master the Art of Dark Web Intelligence Gathering