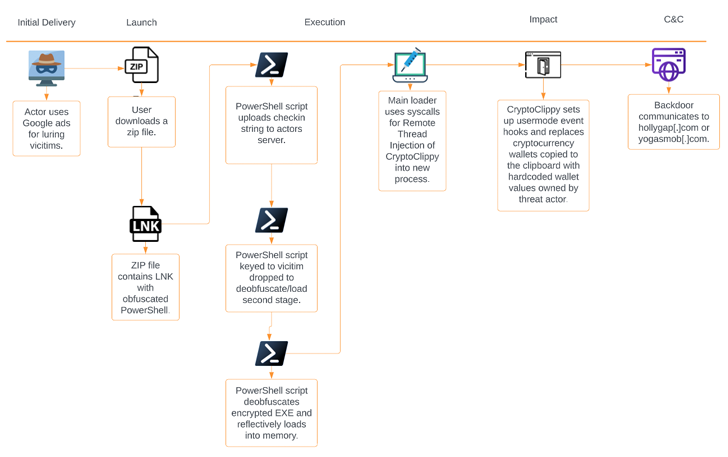
Portuguese end users are currently being targeted by a new malware codenamed CryptoClippy that is able of thieving cryptocurrency as element of a malvertising marketing campaign.
The action leverages Website positioning poisoning tactics to entice people looking for “WhatsApp web” to rogue domains hosting the malware, Palo Alto Networks Device 42 mentioned in a new report printed right now.
CryptoClippy, a C-primarily based executable, is a variety of cryware identified as clipper malware that displays a victim’s clipboard for information matching cryptocurrency addresses and substituting them with a wallet address below the menace actor’s regulate.
“The clipper malware utilizes regular expressions (regexes) to discover what variety of cryptocurrency the address pertains to,” Device 42 researchers stated.
“It then replaces the clipboard entry with a visually very similar but adversary-controlled wallet address for the appropriate cryptocurrency. Afterwards, when the victim pastes the address from the clipboard to perform a transaction, they essentially are sending cryptocurrency directly to the menace actor.”
The illicit plan is approximated to have netted its operators about $983 so considerably, with victims identified across producing, IT companies, and actual estate industries.
It truly is worthy of noting that the use of poisoned research final results to provide malware has been adopted by danger actors involved with the GootLoader malware.
Forthcoming WEBINARLearn to Protected the Id Perimeter – Verified Techniques
Boost your organization security with our future professional-led cybersecurity webinar: Investigate Identification Perimeter tactics!
Never Miss out on Out – Preserve Your Seat!
Yet another method made use of to decide appropriate targets is a traffic direction method (TDS), which checks if the preferred browser language is Portuguese, and if so, takes the user to a rogue landing site.
Users who do not fulfill the requisite standards are redirected to the genuine WhatsApp Web domain with no any further more malicious activity, thus preventing detection.
The conclusions get there days soon after SecurityScorecard thorough an data stealer identified as Lumma that is capable of harvesting facts from web browsers, cryptocurrency wallets, and a wide variety of applications this sort of as AnyDesk, FileZilla, KeePass, Steam, and Telegram.
Identified this short article intriguing? Follow us on Twitter and LinkedIn to go through additional distinctive articles we submit.
Some parts of this article are sourced from:
thehackernews.com

 FBI Leads International Effort to Seize Domains for Notorious Genesis Market
FBI Leads International Effort to Seize Domains for Notorious Genesis Market