Several threat actors have been observed making use of two new variants of the IcedID malware in the wild with much more limited features that gets rid of features relevant to on the internet banking fraud.
IcedID, also identified as BokBot, started off as a banking trojan in 2017. It really is also able of delivering additional malware, which include ransomware.
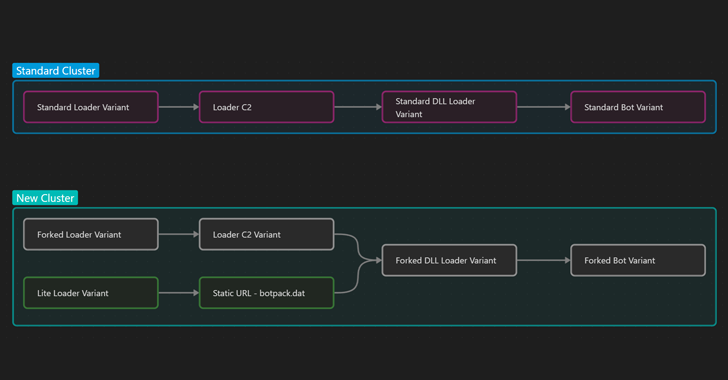
“The properly-acknowledged IcedID version consists of an original loader which contacts a Loader [command-and-control] server, downloads the standard DLL Loader, which then delivers the regular IcedID Bot,” Proofpoint said in a new report released Monday.
A person of the new versions is a Lite variant that was earlier highlighted as being dropped as a comply with-on payload by the Emotet malware in November 2022. Also newly noticed in February 2023 is a Forked variant of IcedID.
Each these variants are intended to fall what is actually identified as a Forked edition of IcedID Bot that leaves out the web injects and backconnect operation that would commonly be made use of for banking fraud, the company security firm noted.
“It is likely a cluster of threat actors is working with modified variants to pivot the malware absent from typical banking trojan and banking fraud exercise to concentration on payload supply, which most likely incorporates prioritizing ransomware supply,” Proofpoint mentioned.
The February campaign has been tied to a new group christened TA581, with the danger actor distributing the Forked variant working with weaponized Microsoft OneNote attachments. A different malware applied by TA581 is the Bumblebee loader.
WEBINARDiscover the Hidden Risks of Third-Party SaaS Applications
Are you aware of the hazards involved with 3rd-celebration application obtain to your company’s SaaS apps? Sign up for our webinar to understand about the styles of permissions becoming granted and how to reduce risk.
RESERVE YOUR SEAT
In all, the Forked IcedID variant has been used in seven various campaigns to day, some of which have been undertaken by initial entry brokers (IABs).
The use of existing Emotet infections to provide the Lite variant has elevated the chance of a potential partnership among Emotet builders and IcedID operators.
“Though traditionally IcedID’s primary functionality was a banking trojan, the removal of banking functionality aligns with the general landscape shift away from banking malware and an growing focus on remaining a loader for observe-on infections, together with ransomware,” the researchers stated.
Observed this report exciting? Stick to us on Twitter and LinkedIn to read far more exclusive content material we publish.
Some parts of this article are sourced from:
thehackernews.com

 Breaking the Mold: Pen Testing Solutions That Challenge the Status Quo
Breaking the Mold: Pen Testing Solutions That Challenge the Status Quo