The North Korean highly developed persistent threat (APT) actor dubbed ScarCruft is working with weaponized Microsoft Compiled HTML Aid (CHM) files to download further malware.
In accordance to multiple stories from AhnLab Security Emergency reaction Centre (ASEC), SEKOIA.IO, and Zscaler, the growth is illustrative of the group’s constant attempts to refine and retool its methods to sidestep detection.
“The team is consistently evolving its applications, tactics, and techniques whilst experimenting with new file formats and strategies to bypass security suppliers,” Zscaler researchers Sudeep Singh and Naveen Selvan explained in a new assessment published Tuesday.
ScarCruft, also tracked under the names APT37, Reaper, RedEyes, and Ricochet Chollima, has exhibited an elevated operational tempo considering that the commence of the yr, focusing on a variety of South Korean entities for espionage reasons. It is recognized to be active considering the fact that at the very least 2012.
Very last month, ASEC disclosed a campaign that used HWP data files that consider edge of a security flaw in the Hangul phrase processing application to deploy a backdoor referred to as M2RAT.
But new results reveal the danger actor is also employing other file formats these as CHM, HTA, LNK, XLL, and macro-dependent Microsoft Workplace files in its spear-phishing attacks from South Korean targets.
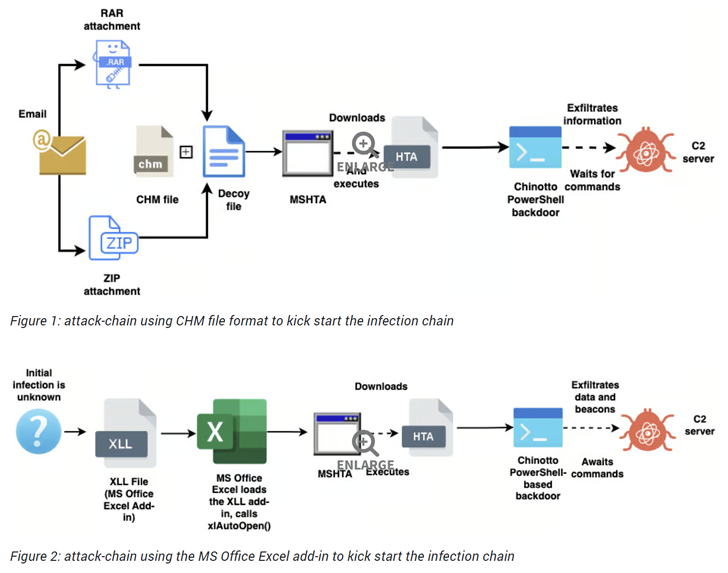
These an infection chains typically provide to show a decoy file and deploy an up to date model of a PowerShell-based mostly implant identified as Chinotto, which is capable of executing commands despatched by a server and exfiltrating delicate information.
Some of the new capabilities of Chinotto include capturing screenshots every five seconds and logging keystrokes. The captured details is saved in a ZIP archive and despatched to a distant server.
WEBINARDiscover the Hidden Risks of Third-Get together SaaS Applications
Are you aware of the threats connected with third-get together app entry to your company’s SaaS applications? Sign up for our webinar to discover about the varieties of permissions remaining granted and how to limit risk.
RESERVE YOUR SEAT
The insights about ScarCruft’s several attack vectors arrive from a GitHub repository taken care of by the adversarial collective to host malicious payloads considering the fact that October 2020.
“The risk actor was ready to maintain a GitHub repository, often staging destructive payloads for much more than two years without having getting detected or taken down,” Zscaler scientists reported.
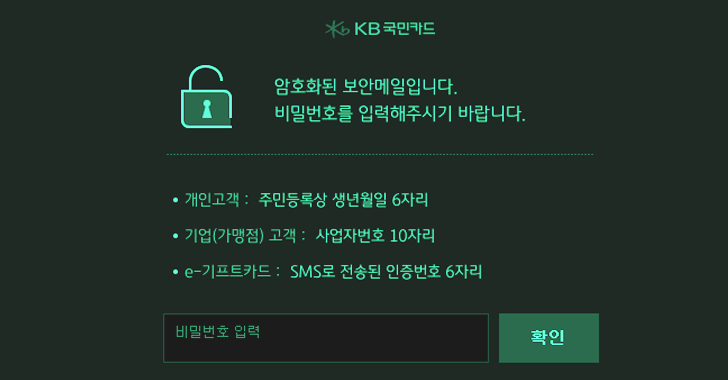
Outside the house of malware distribution, ScarCruft has also been observed serving credential phishing webpages concentrating on many email and cloud companies this kind of as Naver, iCloud, Kakao, Mail.ru, and 163.com.
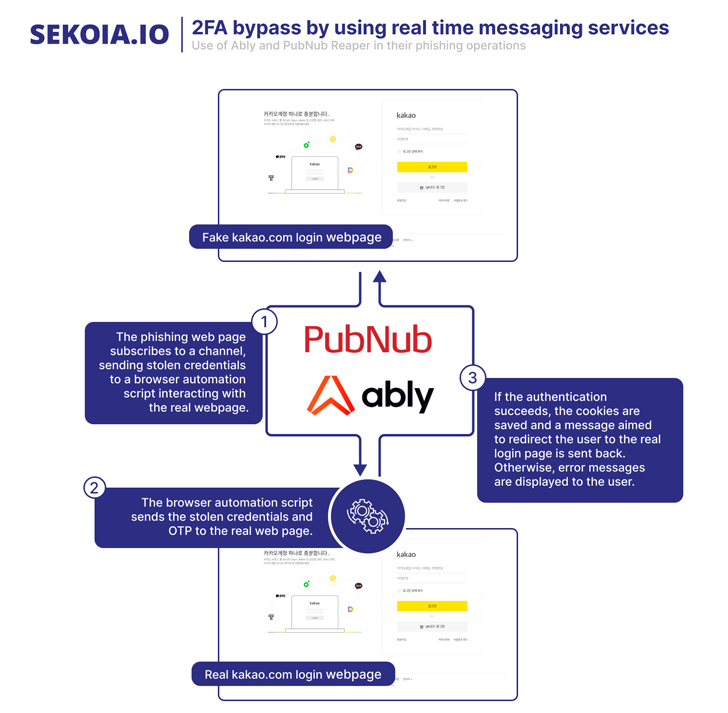
It’s even so not obvious how these web pages are accessed by the victims, increasing the risk that they might have been embedded inside iframes on web sites managed by the attacker or despatched as HTML attachments by using email.
Also found by SEKOIA.IO is a piece of malware named AblyGo, a backdoor composed in Go that makes use of the Ably serious-time messaging framework to get commands.
The use of CHM files to smuggle malware seems to be catching on with other North Korea-affiliated groups as well, with ASEC uncovering a phishing marketing campaign orchestrated by Kimsuky to distribute a backdoor liable for harvesting clipboard info and recording keystrokes.
Observed this report fascinating? Abide by us on Twitter and LinkedIn to examine extra unique information we submit.
Some parts of this article are sourced from:
thehackernews.com

 Security Researchers Spot $36m BEC Attack
Security Researchers Spot $36m BEC Attack