The menace group tracked as REF2924 has been observed deploying earlier unseen malware in its attacks aimed at entities in South and Southeast Asia.
The malware, dubbed NAPLISTENER by Elastic Security Labs, is an HTTP listener programmed in C# and is built to evade “network-primarily based varieties of detection.”
REF2924 is the moniker assigned to an activity cluster connected to assaults towards an entity in Afghanistan as effectively as the Overseas Affairs Office environment of an ASEAN member in 2022.
The threat actor’s modus operandi implies overlaps with one more hacking team dubbed ChamelGang, which was documented by Russian cybersecurity corporation Constructive Technologies in October 2021.
Attacks orchestrated by the team are explained to have exploited internet-exposed Microsoft Trade servers to deploy backdoors such as DOORME, SIESTAGRAPH, and ShadowPad.
DOORME, an Internet Information Products and services (IIS) backdoor module, provides remote access to a contested network and executes further malware and applications.
SIESTAGRAPH employs Microsoft’s Graph API for command-and-handle by way of Outlook and OneDrive, and arrives with abilities to run arbitrary commands as a result of Command Prompt, upload and down load documents to and from OneDrive, and take screenshots.
ShadowPad is a privately offered modular backdoor and a successor of PlugX, enabling threat actors to keep persistent entry to compromised desktops and run shell commands and stick to-on payloads.
The use of ShadowPad is noteworthy as it signifies a potential website link to China-based mostly hacking groups, which are recognized to make use of the malware in a variety of campaigns above the years.
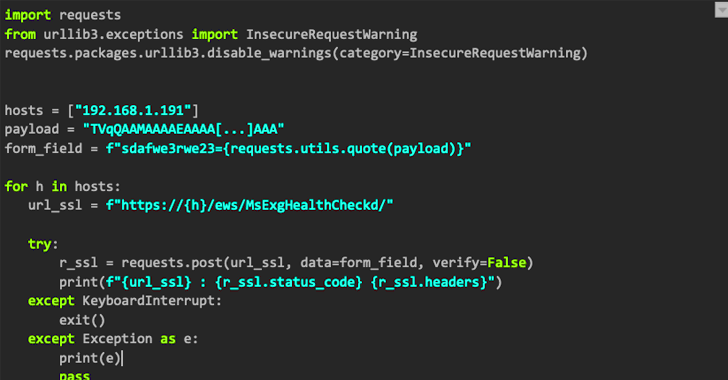
To this list of growing malware arsenal made use of by REF2924 joins NAPLISTENER (“wmdtc.exe”), which masquerades as a authentic support Microsoft Dispersed Transaction Coordinator (“msdtc.exe”) in an attempt to fly beneath the radar and establish persistent accessibility.
WEBINARDiscover the Hidden Dangers of 3rd-Party SaaS Applications
Are you mindful of the pitfalls connected with third-celebration app entry to your company’s SaaS applications? Be a part of our webinar to master about the sorts of permissions staying granted and how to limit risk.
RESERVE YOUR SEAT
“NAPLISTENER results in an HTTP request listener that can method incoming requests from the internet, reads any knowledge that was submitted, decodes it from Base64 structure, and executes it in memory,” security researcher Remco Sprooten reported.
Code assessment indicates the risk actor borrows or repurposes code from open resource initiatives hosted on GitHub to establish its individual resources, a indicator that REF2924 may possibly be actively honing a raft of cyber weapons.
The results also occur as a Vietnamese corporation was focused in late December 2022 by a earlier unidentified Windows backdoor codenamed PIPEDANCE to facilitate publish-compromise and lateral motion pursuits, which include Cobalt Strike.
Observed this article fascinating? Observe us on Twitter and LinkedIn to examine a lot more distinctive information we submit.
Some parts of this article are sourced from:
thehackernews.com

 BreachForums Administrator Baphomet Shuts Down Infamous Hacking Forum
BreachForums Administrator Baphomet Shuts Down Infamous Hacking Forum