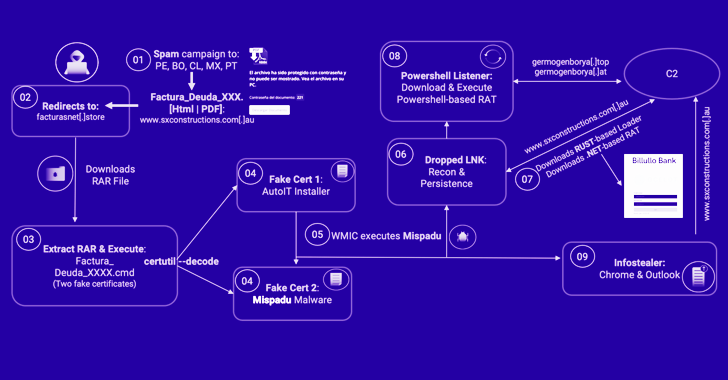
A banking trojan dubbed Mispadu has been joined to various spam campaigns concentrating on international locations like Bolivia, Chile, Mexico, Peru, and Portugal with the target of thieving qualifications and delivering other payloads.
The action, which commenced in August 2022, is now ongoing, Ocelot Workforce from Latin American cybersecurity business Metabase Q claimed in a report shared with The Hacker Information.
Mispadu (aka URSA) was to start with documented by ESET in November 2019, describing its potential to perpetrate financial and credential theft and act as a backdoor by getting screenshots and capturing keystrokes.
“A single of their principal approaches is to compromise legit internet sites, hunting for vulnerable versions of WordPress, to convert them into their command-and-regulate server to distribute malware from there, filtering out nations they do not wish to infect, dropping diverse kind of malware based on the nation getting infected,” scientists Fernando García and Dan Regalado said.
It really is also claimed to share similarities with other banking trojans concentrating on the area, like Grandoreiro, Javali, and Lampion. Attack chains involving the Delphi malware leverage email messages urging recipients to open pretend overdue invoices, thus triggering a multi-phase an infection process.
Must a victim open up the HTML attachment despatched by way of the spam email, it verifies that the file was opened from a desktop device and then redirects to a distant server to fetch the initially-stage malware.
The RAR or ZIP archive, when released, is built to make use of rogue electronic certificates – one particular which is the Mispadu malware and the other, an AutoIT installer – to decode and execute the trojan by abusing the respectable certutil command-line utility.
Mispadu is geared up to assemble the list of antivirus methods mounted on the compromised host, siphon qualifications from Google Chrome and Microsoft Outlook, and facilitate the retrieval of extra malware.
WEBINARDiscover the Concealed Hazards of 3rd-Party SaaS Applications
Are you informed of the challenges involved with 3rd-occasion app entry to your firm’s SaaS apps? Sign up for our webinar to understand about the types of permissions getting granted and how to lower risk.
RESERVE YOUR SEAT
This contains an obfuscated Visible Basic Script dropper that serves to obtain an additional payload from a difficult-coded domain, a .NET-based mostly remote accessibility resource that can run commands issued by an actor-controlled server, and a loader written in Rust that, in transform, executes a PowerShell loader to operate information directly from memory.
What is much more, the malware makes use of malicious overlay screens to acquire credentials linked with on the web banking portals and other sensitive facts.
Metabase Q observed that the certutil strategy has authorized Mispadu to bypass detection by a extensive array of security application and harvest over 90,000 financial institution account qualifications from in excess of 17,500 unique web-sites.
Uncovered this posting fascinating? Abide by us on Twitter and LinkedIn to read more unique material we article.
Some parts of this article are sourced from:
thehackernews.com

 UK Ransomware Incident Volumes Surge 17% in 2022
UK Ransomware Incident Volumes Surge 17% in 2022