The menace actors guiding the CatB ransomware operation have been observed employing a strategy called DLL lookup get hijacking to evade detection and launch the payload.
CatB, also referred to as CatB99 and Baxtoy, emerged late previous year and is mentioned to be an “evolution or immediate rebrand” of a further ransomware pressure known as Pandora centered on code-level similarities.
It can be well worth noting that the use of Pandora has been attributed to Bronze Starlight (aka DEV-0401 or Emperor Dragonfly), a China-based threat actor that’s acknowledged to utilize quick-lived ransomware households as a ruse to probable conceal its genuine aims.
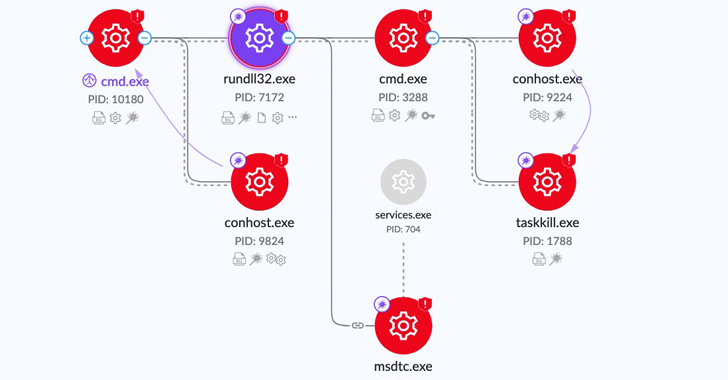
Just one of the key defining attributes of CatB is its reliance on DLL hijacking through a authentic provider called Microsoft Distributed Transaction Coordinator (MSDTC) to extract and start the ransomware payload.
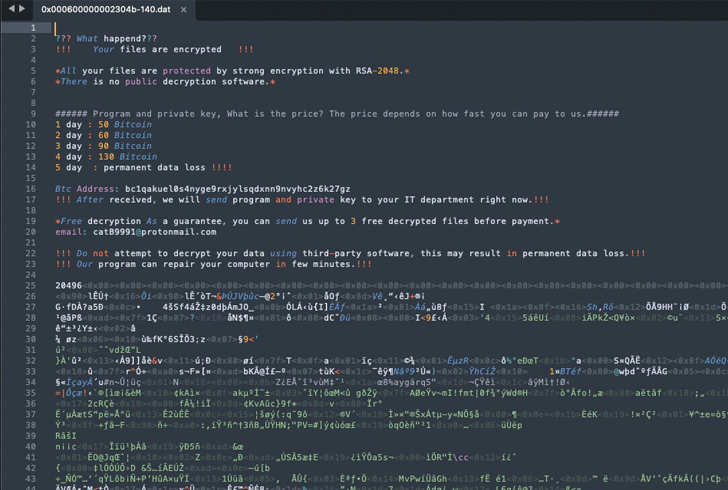
“Upon execution, CatB payloads count on DLL research order hijacking to drop and load the destructive payload,” SentinelOne researcher Jim Walter reported in a report released past 7 days. “The dropper (variations.dll) drops the payload (oci.dll) into the System32 directory.”
The dropper is also accountable for carrying out anti-investigation checks to identify if the malware is currently being executed inside a digital surroundings, and eventually abusing the MSDTC support to inject the rogue oci.dll made up of the ransomware into the msdtc.exe executable upon procedure restart.
“The [MSDTC] configurations altered are the title of the account underneath which the assistance should really operate, which is modified from Network Services to Regional Program, and the provider get started selection, which is modified from Desire start to Auto commence for persistency if a restart takes place,” Minerva Labs researcher Natalie Zargarov discussed in a preceding investigation.
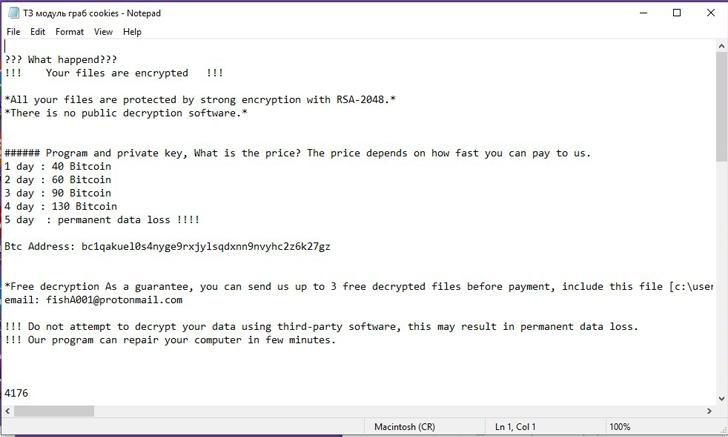
A person putting component of the ransomware is its absence of a ransom be aware. As an alternative, each encrypted file is updated with a information urging the victims to make a Bitcoin payment.
WEBINARDiscover the Concealed Risks of Third-Get together SaaS Applications
Are you aware of the pitfalls affiliated with 3rd-bash app obtain to your firm’s SaaS apps? Be a part of our webinar to discover about the types of permissions becoming granted and how to decrease risk.
RESERVE YOUR SEAT
Another trait is the malware’s ability to harvest sensitive data such as passwords, bookmarks, historical past from web browsers Google Chrome, Microsoft Edge (and Internet Explorer), and Mozilla Firefox.
“CatB joins a prolonged line of ransomware people that embrace semi-novel procedures and atypical behaviors these kinds of as appending notes to the head of information,” Walter mentioned. “These behaviors look to be applied in the fascination of detection evasion and some degree of anti-examination trickery.”
This is not the 1st time the MSDTC provider has been weaponized for destructive purposes. In May 2021, Trustwave disclosed a novel malware dubbed Pingback that leveraged the similar method to accomplish persistence and bypass security answers.
Uncovered this post interesting? Adhere to us on Twitter and LinkedIn to read additional exclusive material we write-up.
Some parts of this article are sourced from:
thehackernews.com

 Traditional App Security is No Longer Enoughwww.nonamesecurity.comAPI SecurityWhen it comes to ensuring the security of your APIs, there are four critical capabilities.
Traditional App Security is No Longer Enoughwww.nonamesecurity.comAPI SecurityWhen it comes to ensuring the security of your APIs, there are four critical capabilities.