Danger activity clusters affiliated with the Chinese and Russian cybercriminal ecosystems have been observed making use of a new piece of malware that is made to load Cobalt Strike on to contaminated machines.
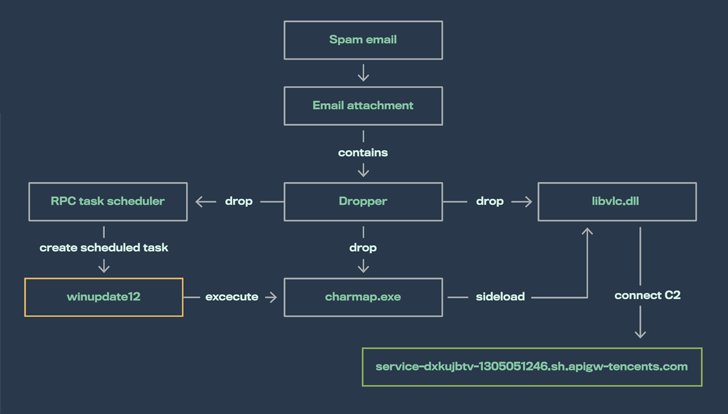
Dubbed SILKLOADER by Finnish cybersecurity organization WithSecure, the malware leverages DLL aspect-loading strategies to supply commercial adversary simulation computer software.
The development comes as improved detection capabilities from Cobalt Strike, a authentic publish-exploitation device made use of for crimson group functions, is forcing menace actors to request choice possibilities or concoct new strategies to propagate the framework to evade detection.
“The most typical of these include introducing complexity to the car-generated beacon or stager payloads by means of the utilization of packers, crypters, loaders, or very similar strategies,” WithSecure scientists claimed.
SILKLOADER joins other loaders such as KoboldLoader, MagnetLoader, and LithiumLoader that have been recently learned incorporating Cobalt Strike elements.
It also shares overlaps with LithiumLoader in that each hire the DLL aspect-loading process to hijack a legitimate application with the objective of jogging a independent, malicious dynamic connection library (DLL).
SILKLOADER achieves this by using specially crafted libvlc.dll files that are dropped alongside a authentic but renamed VLC media participant binary (Charmap.exe).
WithSecure claimed it discovered the shellcode loader subsequent an evaluation of “many human-operated intrusions” targeting many entities spanning a extensive range of corporations situated in Brazil, France, and Taiwan in Q4 2022.
While these attacks have been unsuccessful, the action is suspected to be a guide-up to ransomware deployments, with the techniques and tooling “greatly overlapping” with those people attributed to the operators of the Enjoy ransomware.
In just one attack aimed at an unnamed French social welfare corporation, the threat actor attained a foothold into the network by exploiting a compromised Fortinet SSL VPN equipment to stage Cobalt Strike beacons.
“The menace actor preserved a foothold in this group for a number of months,” WithSecure said. “For the duration of this time, they executed discovery and credential stealing activities, followed by deployment of several Cobalt Strike beacons.”
But when this endeavor unsuccessful, the adversary switched to employing SILKLOADER to bypass detection and produce the beacon payload.
That’s not all. An additional loader identified as BAILLOADER, which is also utilised to distribute Cobalt Strike beacons, has been linked to attacks involving Quantum ransomware, GootLoader, and the IcedID trojan in recent months.
BAILLOADER, for its portion, is explained to exhibit similarities with a crypter codenamed Tron that has been put to use by distinctive adversaries to distribute Emotet, TrickBot, BazarLoader, IcedID, Conti ransomware, and Cobalt Strike.
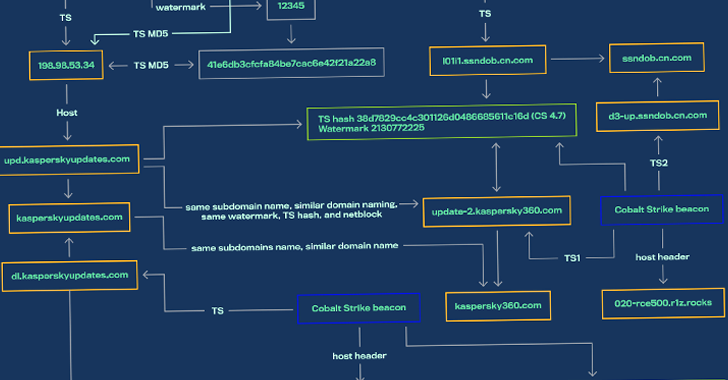
This has supplied increase to the possibility that disparate danger actors share Cobalt Strike beacons, crypters, and infrastructure provided by third-party affiliates to support a number of intrusions utilizing diverse techniques.
In other words, SILKLOADER is most likely remaining available as an off-the-shelf loader by way of a Packer-as-a-Support program to Russian-based menace actors.
“This loader is becoming delivered possibly instantly to ransomware teams or probably via teams supplying Cobalt Strike/Infrastructure-as-a-Service to trusted affiliate marketers,” WithSecure said.
WEBINARDiscover the Hidden Risks of Third-Celebration SaaS Apps
Are you conscious of the dangers involved with third-celebration app obtain to your firm’s SaaS applications? Be part of our webinar to find out about the sorts of permissions remaining granted and how to lessen risk.
RESERVE YOUR SEAT
“Most of these affiliates show up to have been aspect of or have experienced near functioning associations with the Conti team, its users, and offspring immediately after its alleged shutdown.”
SILKLOADER samples analyzed by the company clearly show that early variations of the malware day back to the get started of 2022, with the loader solely place to use in distinctive attacks concentrating on victims in China and Hong Kong.
The shift from East Asian targets to other countries this sort of as Brazil and France is believed to have transpired about July 2022, just after which all SILKLOADER-linked incidents have been attributed to Russian cybercriminal actors.
This has even more presented way to a speculation that “SILKLOADER was initially prepared by danger actors performing inside of the Chinese cybercriminal ecosystem” and that the “loader was utilised by the threat actors within just this nexus at minimum as early as Could 2022 till July 2022.”
“The builder or source code was later acquired by a risk actor within just the Russian cybercriminal ecosystem in between July 2022 and September 2022,” WithSecure explained, adding, “the original Chinese creator sold the loader to a Russian menace actor at the time they no for a longer period experienced any use for it.”
Both equally SILKLOADER and BAILLOADER are just the latest illustrations of danger actors refining and retooling their techniques to continue to be forward of the detection curve.
“As the cybercriminal ecosystem results in being far more and far more modularized through provider offerings, it is no longer probable to attribute attacks to menace groups simply just by
linking them to particular parts inside their attacks,” WithSecure researchers concluded.
Located this article exciting? Adhere to us on Twitter and LinkedIn to read additional unique content we put up.
Some parts of this article are sourced from:
thehackernews.com

 NCSC Calms Fears Over ChatGPT Threat
NCSC Calms Fears Over ChatGPT Threat